
The Seiko USA web site was defaced over the weekend, displaying a message from attackers claiming they stole its Shopify buyer database and threatening to leak it except a ransom is paid.
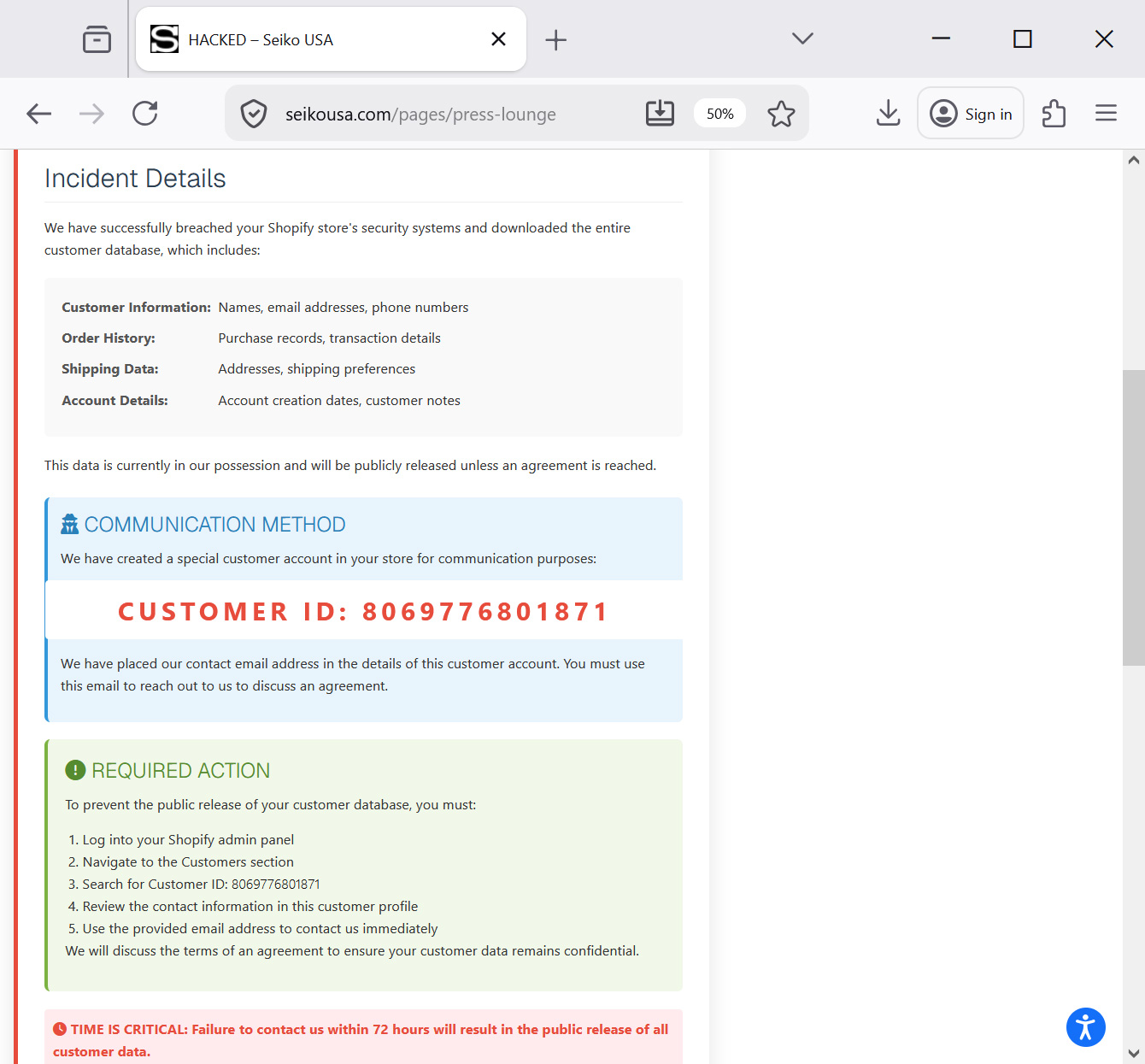
Guests to the “Press Lounge” part of the location have been proven a web page titled “HACKED,” which changed regular content material with what gave the impression to be a ransom demand and information breach notification.
The message warned that attackers had gained entry to the corporate’s Shopify backend and exfiltrated delicate buyer data.
“That is an pressing safety notification relating to your Shopify retailer. Your buyer database has been compromised,” learn the defaced webpage.
“We’ve got efficiently breached your Shopify retailer’s safety programs and downloaded all the buyer database.”
Supply: BleepingComputer
The menace actors declare the stolen information comprises the next data:
- Buyer Info: Names, e-mail addresses, telephone numbers
- Order Historical past: Buy data, transaction particulars
- Delivery Information: Addresses, transport preferences
- Account Particulars: Account creation dates, buyer notes
The attackers warn that the stolen information might be publicly launched except Seiko USA enters into negotiations.
As a part of the demand, they instructed the corporate to find a particular buyer account, recognized as ID 8069776801871, throughout the Shopify admin panel. The menace actors say {that a} contact e-mail deal with was added to that account profile and needs to be used to provoke negotiations.
The defacement additional warned that Seiko USA had 72 hours to contact them or the alleged database can be printed.
BleepingComputer has not been capable of decide what menace actor is behind the assault and whether or not their claims are respectable.
Seiko USA has not publicly confirmed or responded to BleepingComputer emails in regards to the incident, however has since eliminated the extortion message from the web site.
AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of recent exploits is coming.
On the Autonomous Validation Summit (Might 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls maintain, and closes the remediation loop.



