
A safety researcher claims Microsoft quietly mounted an Azure Backup for AKS vulnerability after rejecting his report, and blocking a CVE from being issued.
The researcher’s report describes a essential privilege escalation flaw that allowed cluster-admin entry from the low-privileged “Backup Contributor” function.
Microsoft disputes the declare, telling BleepingComputer the habits was anticipated and that “no product adjustments have been made,” regardless of the researcher documenting new permission checks and failed exploit makes an attempt after disclosure, suggestive of a silent patch.
CERT agrees it is a bug, however Microsoft blocks CVE
Safety researcher Justin O’Leary found the safety flaw this March, and reported it to Microsoft on March 17.
Microsoft Safety Response Middle (MSRC) rejected the report on April 13, claiming the problem solely concerned acquiring cluster-admin on a cluster the place “the attacker already held administrator entry,” a characterization O’Leary says misrepresents the assault totally.
“That is factually incorrect,” states the researcher.
“The vulnerability permits a person with zero Kubernetes permissions to realize cluster-admin. The assault doesn’t require current cluster entry — it grants it.”
O’Leary additional says that Microsoft described the submission to MITRE as “AI-generated content material,” one thing he says didn’t deal with the technical deserves of the report.
After the rejection, O’Leary escalated the problem to CERT Coordination Middle, which independently validated the vulnerability on April 16 and, in response to the researcher, assigned it an identifier, VU#284781:
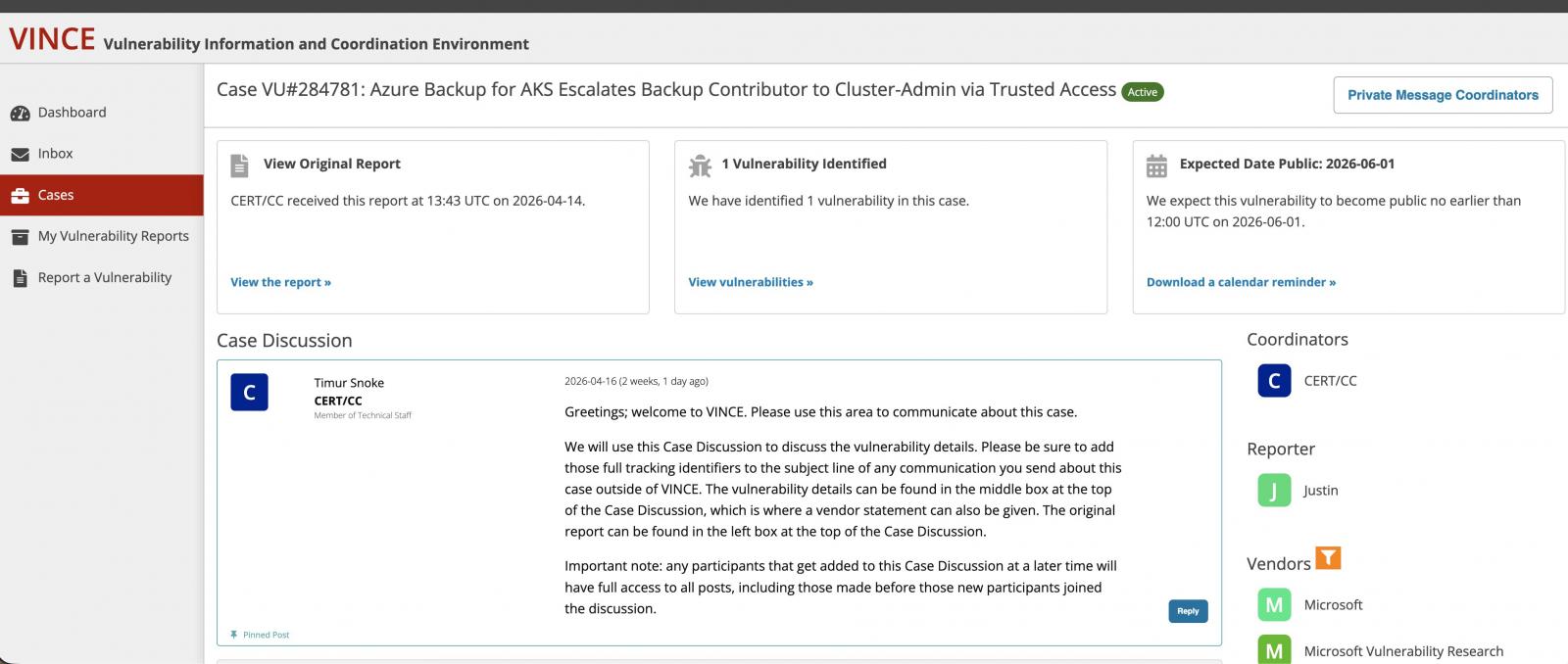
(Justin O’Leary)
CERT/CC had initially scheduled public disclosure for June 1, 2026, however that disclosure by no means occurred.
On Might 4, Microsoft employees reportedly contacted MITRE recommending in opposition to CVE task, once more arguing the problem required pre-existing administrative entry:
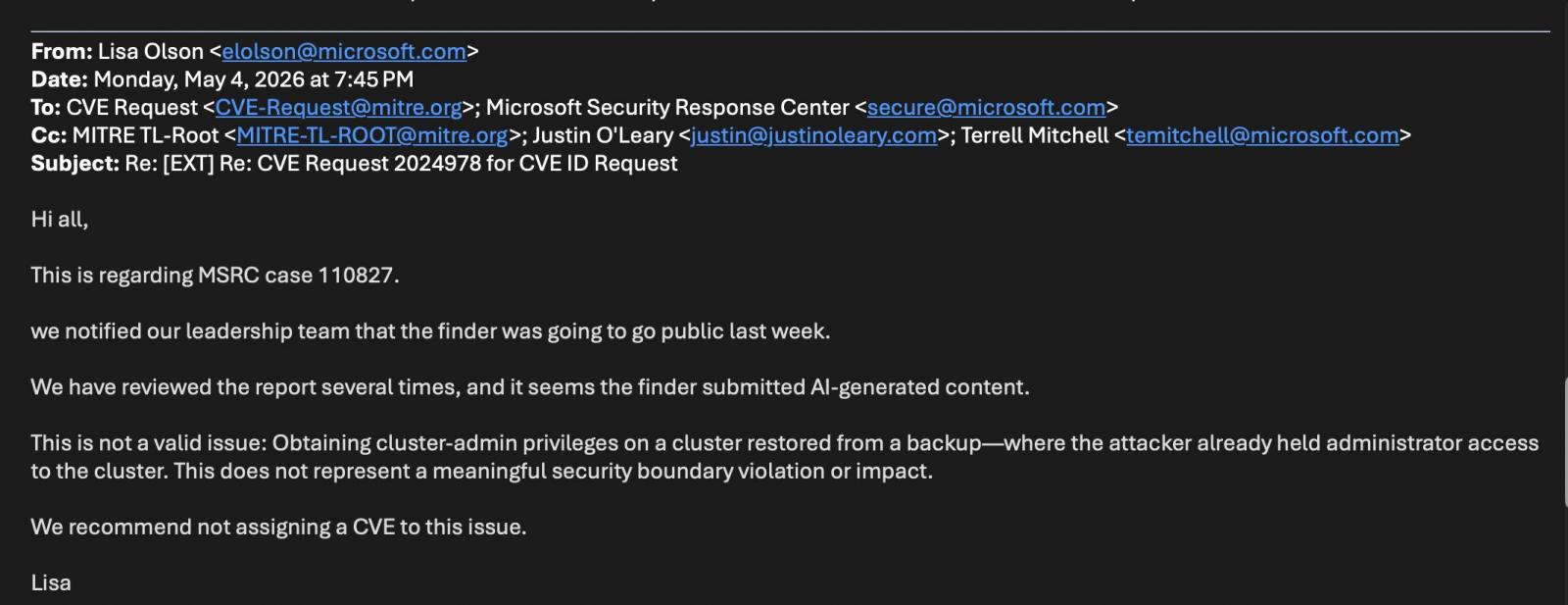
(Justin O’Leary)
CERT/CC later closed the case below CNA hierarchy guidelines, successfully leaving Microsoft (which is a CNA) with last authority over CVE issuance for its personal merchandise.
How the assault labored
Azure Backup for AKS makes use of Trusted Entry to grant backup extensions cluster-admin privileges inside Kubernetes clusters.
Based on O’Leary, the flaw allowed anybody with solely the Backup Contributor function on a backup vault to set off that Trusted Entry relationship with out already having Kubernetes permissions.
An attacker might allow backup on a goal AKS cluster, inflicting Azure to routinely configure Trusted Entry with cluster-admin privileges. From there, an attacker might extract secrets and techniques by way of backup operations or restore malicious workloads into the cluster.
O’Leary labeled the problem as a Confused Deputy vulnerability (CWE-441), the place Azure RBAC and Kubernetes RBAC belief boundaries interacted in a way that bypassed anticipated authorization controls.
Microsoft says no adjustments made, habits says in any other case
BleepingComputer reached out to Microsoft to know if the tech large thought-about this discovering to be a legitimate safety vulnerability.
A Microsoft spokesperson instructed BleepingComputer:
“Our evaluation concluded that this isn’t a safety vulnerability, however reasonably anticipated habits that requires pre-existing administrative privileges inside the buyer’s setting. Due to this fact, no product adjustments have been made to deal with this report and no CVE or CVSS rating have been issued.”
Nonetheless, following the disclosure of his report this month, O’Leary noticed that the unique assault path now not works.
“Present habits returns errors that didn’t exist in March 2026,” he states:
ERROR: UserErrorTrustedAccessGatewayReturnedForbidden
“The Trusted Entry function binding is lacking/has gotten eliminated”
Based on O’Leary, Azure Backup for AKS now requires Trusted Entry to be manually configured earlier than backup will be enabled, reversing the sooner habits the place Azure configured it routinely.
He additionally noticed further permission checks that have been absent throughout his unique testing in March. The vault MSI now requires Reader permissions on each the AKS cluster and snapshot useful resource group, whereas the AKS cluster MSI requires Contributor permissions on the snapshot useful resource group.
In different phrases, the vulnerability seems to have been mounted, however Microsoft has neither issued a public advisory nor notified prospects.
The visibility downside for defenders
And not using a CVE or advisory, defenders have little visibility into the publicity window or remediation timeline.
“Organizations that granted Backup Contributor between an unknown begin date and Might 2026 have been uncovered to privilege escalation,” writes the researcher.
“And not using a CVE, safety groups can not observe this publicity. Silent patching protects distributors, not prospects.”
The case highlights a structural downside with no straightforward repair.
Disputes between safety researchers and main distributors over severity, exploitability, and disclosure have develop into widespread lately, particularly as vulnerability disclosure applications face rising volumes of experiences.
Some open-source maintainers have additionally publicly complained that AI-assisted experiences are overwhelming bug bounty and safety triage techniques, making it more durable for reputable findings to obtain well timed consideration. Circumstances the place huge tech ignored patching legitimate flaws regardless of repeated contact by completely different researchers aren’t unusual both.
And not using a framework that realigns incentives for all events, accountable disclosure dangers turning into a bureaucratic train that serves nobody—least of all of the organizations left uncovered at the hours of darkness.
Automated pentesting instruments ship actual worth, however they have been constructed to reply one query: can an attacker transfer by way of the community? They weren’t constructed to check whether or not your controls block threats, your detection guidelines fireplace, or your cloud configs maintain.
This information covers the 6 surfaces you really have to validate.


