Sign, the encrypted messaging app trusted by security-savvy customers world wide, has confirmed that hackers have managed to takeover accounts — with authorities officers and journalists amongst these being focused.
The warning got here earlier this week, when Sign posted on Bluesky that assaults had taken place, whereas underlining that its encryption and underlying central infrastructure remained intact and uncompromised.
The issue is just not with Sign itself, however somewhat with its customers being tricked into handing over the keys to their accounts.
On the identical day, the Dutch Basic Intelligence and Safety Service (AIVD) and Defence Intelligence and Safety Service (MIVD) printed a joint advisory blaming assaults towards Sign and WhatsApp customers on Russian-backed hackers.
Based on the Dutch intelligence companies, the operation is “large-scale and international,” with victims confirmed to incorporate Dutch authorities workers. Journalists are additionally understood to have been focused.
The assaults spotlight that even the strongest encryption can’t shield you in case you are tricked into management of your account over to a malicious hacker.
Slightly than attempting to interrupt the cryptography which protects messages despatched by way of Sign or WhatsApp, attackers are merely persuading customers at hand over their verification codes or unwittingly hyperlink a second gadget to their account — quietly giving attackers a entry to non-public conversations.
The hacking marketing campaign makes use of two most important strategies, neither of which requires exploiting any vulnerability in Sign or WhatsApp. As a substitute, the attackers depend on the tried-and-trusted trick of social engineering.
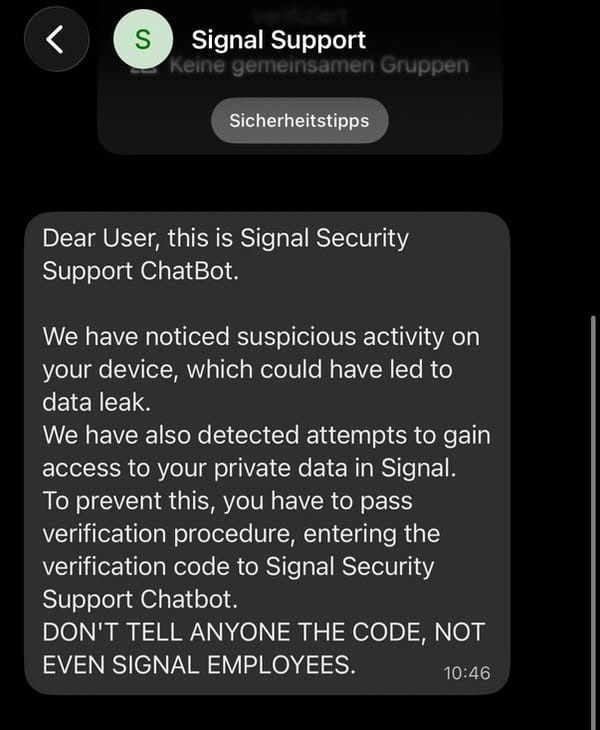
As Sign defined in its publish, focused victims obtain an in-app message which purports to return from “Sign Safety Assist Chatbot”, or the same official-sounding account.
The message claims that suspicious exercise has been detected, and the sufferer is prompted to finish a “verification process” by coming into their SMS verification code and Sign PIN.
After all, as soon as the credentials have been handed over, attackers can register the sufferer’s account on a tool underneath their management – having access to incoming messages and group chats.
One other assault methodology abuses the “linked gadgets” characteristic utilized by Sign and WhatsApp. A hacker can ship their meant goal a QR code or hyperlink that seems to be a gaggle chat invitation or routine safety immediate. The fact is that scanning the QR code hyperlinks the attacker’s gadget to the sufferer’s account, permitting their conversations to be monitored surreptitiously.
Based on Sign, it’s engaged on including extra warnings inside its app to alert customers to the potential risks of responding to a phishing message.
Based on the corporate, it says it can by no means contact customers by way of in-app messages, SMS, or social media to request verification credentials. And if somebody contacts you claiming to be the “Sign Safety Assist Chatbot” – properly, they’re an attacker.
You may assessment what gadgets are linked to your Sign and WhatsApp accounts by going to Settings > Linked Gadgets, and take away something that you don’t recognise.
And keep in mind – no quantity of encryption can prevent from being socially engineered.

