The conflict in Iran was lower than 24 hours previous when it produced a historic first: the deliberate concentrating on of economic information facilities. On March 1st, Iranian drones hit three Amazon Internet Providers (AWS) amenities within the United Arab Emirates and Bahrain, disrupting core cloud infrastructure and knocking out finance apps and enterprise instruments not solely throughout the Gulf, but in addition distant from the area. The assaults confirmed that bodily distance from a battle zone isn’t any assure of insulation from the impacts of kinetic warfare.
For many organizations, nevertheless, the extra instant threat performs out in our on-line world and entails all method of risk actors. Inside hours of the US-Israel ‘Operation Epic Fury’ (‘Operation Roaring Lion’) on February 28th, Iran-nexus cyber-actors mobilized in giant numbers – Palo Alto Networks’ Unit 42 counted greater than 60 energetic pro-Iranian hacktivist teams. Additionally inside hours, cybersecurity businesses within the United Kingdom and Canada each warned about heightened risk ranges. Earlier than lengthy, related warnings had been echoed by Europol and the US Division of Homeland Safety.
Threats and risk actors
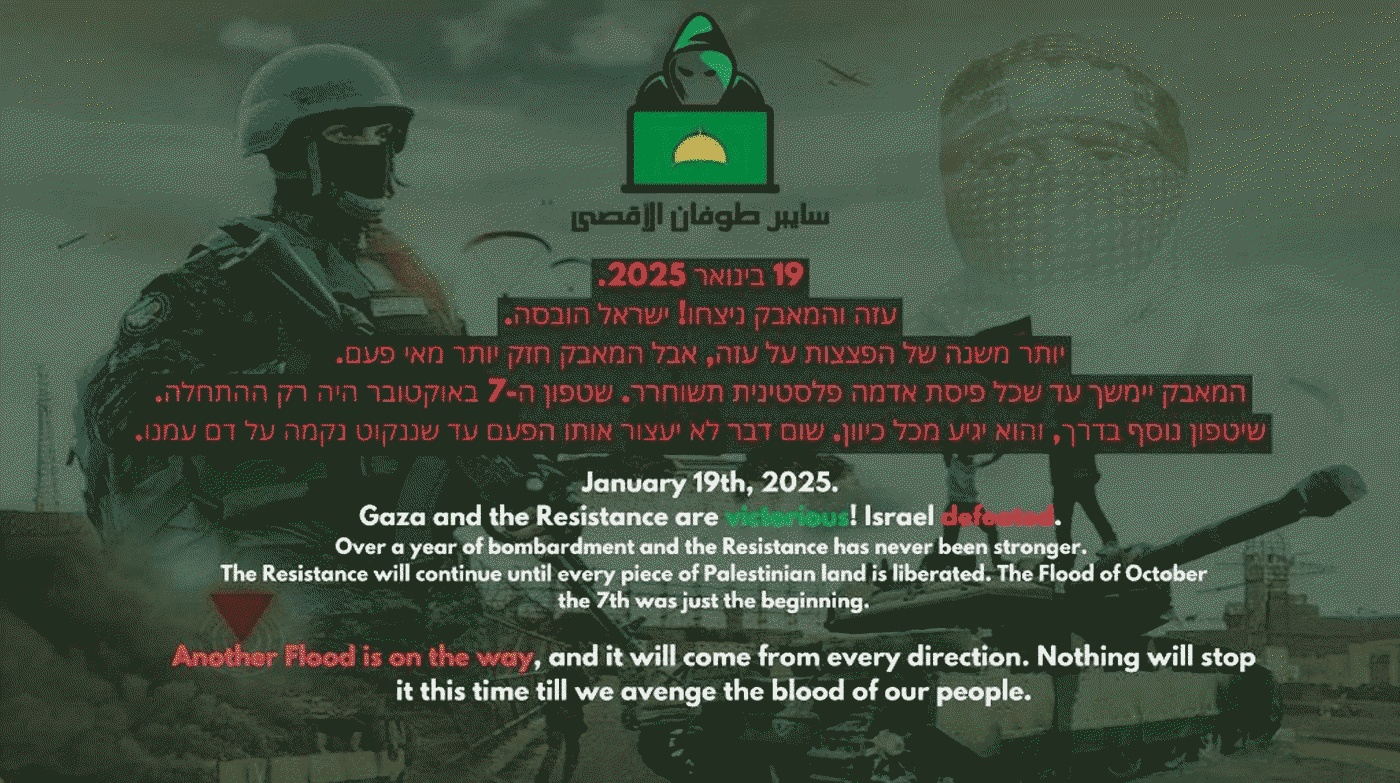
The outbreak of a kinetic battle typically broadens each the quantity and the forged of cyber-actors concerned. Hacktivist exercise – noisy and infrequently wrapped in bluster and bravado – typically surges first. Superior Persistent Menace (APT) operations involving reconnaissance and preliminary entry run in parallel or carefully behind. As soon as footholds are established and targets are mapped, the stage is ready for regardless of the operation was really designed to perform, be it espionage, disruption, sabotage or different objectives.
The strains aren’t essentially clear-cut, in fact, and a few techniques will be deployed in tandem: an internet site defacement or distributed denial-of-service (DDoS) assault that appears like a nuisance-level hacktivist operation is likely to be a deliberate distraction from an precise assault that’s quietly exploiting the goal by a distinct vector.
Iran-nexus teams rank among the many most energetic and resourceful state-aligned teams worldwide, and their offensive cyber-capabilities and toolsets have matured not too long ago. The risk is very acute for organizations with provide chain relationships within the Center East or different ties to the area, to not point out these with cloud dependencies there.
The CyberAv3ngers group’s marketing campaign in opposition to water and wastewater utilities within the US and different nations in 2023 illustrated how that concentrating on logic is operationalized. The ominous message that the dangerous actor left on compromised programs – “You may have been hacked, down with Israel. Each tools ‘made in Israel’ is CyberAv3ngers authorized goal” – learn like hacktivist output, however the group was rapidly discovered to be working underneath Iranian state path. This blurring of hacktivist id and state-aligned operations, whose roots could properly return to the Saudi Aramco incident in 2012, has a reputation, too: “faketivism.”
Operational overlaps amongst distinct teams run even deeper than that, nevertheless. ESET researchers have beforehand documented shut hyperlinks between a number of Iran-aligned APT actors. Notably, MuddyWater has labored carefully with Lyceum, a subgroup of OilRig, in addition to in all probability acted as an preliminary entry dealer (IAB) for different Iran-aligned teams.
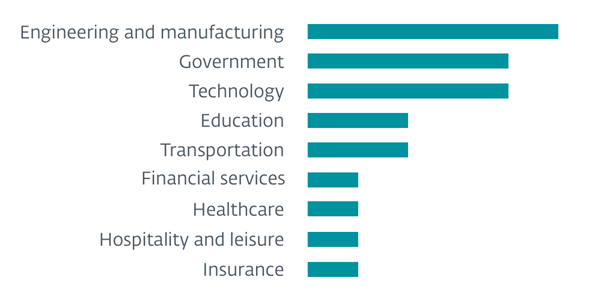
Muddying the waters additional, a number of pro-Russian hacktivist teams have now apparently joined the fray in assist of Iran, and there are reviews of Iran-linked teams partaking with IABs on Russian cybercrime boards. This successfully expands each the out there instruments and the vary of reachable targets. Important infrastructure is without doubt one of the most coveted ‘trophies’ by all method of adversaries, and up to date ESET telemetry reveals that Iran-aligned actors disproportionately goal entities that function in engineering and manufacturing.
Additionally, every time the aim is retaliation, destruction tends to take precedence over, say, ransomware-fueled extortion. Knowledge-wiping malware is a constant characteristic of recent conflict-adjacent operations – Russia-aligned teams have demonstrated this sample repeatedly in Ukraine.
In relation to assaults that give dangerous actors a variety of bang for his or her buck, provide chain compromise usually reigns supreme. Again in 2022, ESET Analysis documented how the Iran-aligned Agrius group deployed a damaging wiper referred to as Fantasy by a supply-chain assault that abused an Israeli software program developer, hitting targets in varied verticals and properly past Israel. The blast radius of a supply-chain assault may attain organizations that had been by no means immediately focused and don’t have any apparent connection to the battle.
A associated threat issues managed companies suppliers (MSPs) and their clients. Additionally in 2022, ESET documented a marketing campaign the place the adversary compromised an MSP to be able to achieve entry to their finish targets. They didn’t must infiltrate their targets immediately; as an alternative, they let the MSP’s entry pathways do the legwork for them. The marketing campaign was orchestrated by the MuddyWater cyberespionage group, not too long ago a powerhouse in Iranian APT circles that has undergone a notable evolution.
As soon as recognized for loud, automated assaults, MuddyWater is now more and more leaning in direction of extra stealthy and refined operations involving ‘hands-on-keyboard’ actions in focused environments. Very like another Iran-aligned collectives, MuddyWater has additionally pivoted to the tried-and-tested strategy of abusing reputable Distant Monitoring and Administration (RMM) software program. That approach, the group can mix into reputable community visitors and complicate detection.
The group can also be recognized to favor inside spearphishing from already-compromised inboxes – emails from a colleague’s account moderately than an exterior sender – with a excessive success fee, for apparent causes. Spearphishing attachments and hyperlinks have lengthy been the preferred preliminary entry strategies amongst most Iran-aligned APT teams, together with OilRig and APT33. Nevertheless, exploitation of recognized software program vulnerabilities isn’t unprecedented, both, as seen in a latest Ballistic Bobcat marketing campaign.
MuddyWater stays very a lot energetic in 2026 – final month, safety researchers at Broadcom’s Symantec and Carbon Black recognized the group within the networks of a number of US entities, together with an airport, a financial institution, and a software program agency with ties to Israel. Nonetheless, the general quantity of offensive cyber-activity from Iran-aligned actors usually is to this point no match to the flurry of exercise noticed by ESET researchers after the assault on Israel on October 7th, 2023. This may occasionally partly be a by-product of Iran’s largely self-imposed, near-total web blackout.
At any fee, as Google’s Menace Evaluation Group (TAG) additionally stated in its evaluation of cyber-activity across the Israel-Hamas conflict, “cyber capabilities […] are a software of first resort.” This remark stays related as we speak – and was exemplified by the primary main cyberattack, on March 12th, because the conflict started. An information-wiping assault, courtesy of pro-Iranian hacktivist group Hamdala, on US-based medical expertise firm Stryker, reportedly brought on the corporate’s programs to close down globally.
Staying resilient: the place to focus
Threats vary from opportunistic DDoS and defacement campaigns to focused data-wiping incursions and cyberespionage with lengthy dwell instances, all the best way to supply-chain harm that wouldn’t spare organizations with no direct connection to the battle. The measures outlined beneath will probably be acquainted to most safety groups. The main target is on the place Iran-aligned actors have traditionally discovered the weak spots.
Know what’s uncovered
Begin with figuring out and securing something internet-facing: distant entry, internet functions, VPN gateways, and internet-connected OT/ICS gadgets in case your group operates such programs. Default credentials needs to be modified on all gadgets. If a tool would not assist sturdy authentication, contemplate whether or not it needs to be linked to the general public web in any respect.
The CyberAv3ngers’ marketing campaign in 2023 focused programmable logic controllers (PLCs) that also had factory-default passwords. CISA’s advisory discusses the particular strategies used and is value reviewing intimately in case your group runs industrial management programs.
Restrict the assault floor
OT/ICS environments pose a particular problem: gadgets deployed a long time in the past with out safety necessities in thoughts and infrequently ever inventoried. Default credentials and web publicity are the obvious issues, however the wider concern is that many of those programs had been by no means designed to be secured after deployment.
Disconnect OT/ICS gadgets from the general public web wherever operationally possible. Wherever doable, apply all out there patches, as susceptible internet-facing gadgets stay some of the dependable entry factors out there to attackers. The place that is not doable, implement community segmentation between IT and OT environments and set up behavioral baselines for industrial protocols in order that anomalous visitors can set off alerts.
Shut the gaps
Most Iranian state-sponsored teams have made id compromise their constant focus. A joint CISA/FBI/NSA advisory from October 2024 documented a year-long marketing campaign through which Iranian actors used password spraying and multi-factor authentication (MFA) push-bombing (flooding customers with login requests till somebody approves one) to breach organizations throughout healthcare, authorities, vitality and IT. As soon as inside, they modified MFA registrations to lock in persistent entry and offered harvested credentials on felony boards.
To counter the risk, implement phishing-resistant MFA throughout all external-facing programs, and audit present MFA configurations for unauthorized registrations.
Audit your provide chain and third-party entry
Audit all third-party and different distant entry pathways. With teams like CyberAv3ngers particularly attempting to find Israeli-made OT tools, evaluate whether or not any of your tools falls into that class.
In case you depend on MSPs, inquire about how they safe their distant entry instruments and whether or not they’ve reviewed their very own publicity in gentle of the battle. MuddyWater’s exploitation of the SimpleHelp software at MSPs confirmed that your supplier’s safety posture is successfully a part of your assault floor.
Be careful for phishing
As MuddyWater and different teams typically depend on human-centered approaches, most notably spearphishing messages from compromised inside accounts, workers must confirm all requests by separate channels, notably these involving credentials, entry modifications, pressing “safety updates” and something referencing the present battle.
Adversaries use frequent AI instruments not solely to generate nuanced phishing lures, but in addition for different steps all through the assault lifecycle, together with to analysis vulnerabilities and assist malware growth.
Map your cloud dependencies
Map which software-as-a-service (SaaS) suppliers you rely upon and discover out the place their infrastructure is hosted. Even if you happen to do not run workloads within the Center East, your suppliers would possibly. Following the AWS strikes, a number of distributors, together with Snowflake and Purple Hat, issued failover advisories, thus successfully reminding their clients that regional cloud disruptions propagate by the availability chain in ways in which aren’t all the time seen till one thing breaks. AWS, for one, has explicitly suggested clients with Center East workloads emigrate them.
Put together for destruction, not simply theft
Throughout conflict-adjacent operations, state-aligned actors are likely to favor wipers over ransomware. Both approach, ensure that at the least one copy of essential backups is offline and air-gapped, moderately than simply replicated to a different cloud area which may share the identical underlying dependencies.
Take a look at whether or not your catastrophe restoration plan covers a full-region cloud outage, as a result of most plans are constructed round single-zone failures. Importantly, confirm that your backups really restore, as a result of wiper and different malware typically targets backup programs particularly.
The whole lot is honest recreation
The risk image will proceed to shift because the battle develops. Hacktivist noise could intensify or fade, whereas APT operations have a tendency to maneuver extra slowly and floor later. The organizations that fare greatest on this setting are usually people who had already closed the essential gaps earlier than the risk turned acute. If primary work (reminiscent of an asset stock) continues to be excellent, the present scenario is grounds sufficient to speed up it.
In case your group has entry to best-of-breed risk intelligence and analysis, now’s the time to maintain an in depth eye on it.

