
A menace actor tracked as ‘Hazy Hawk’ is hijacking forgotten DNS CNAME information pointing to deserted cloud providers, taking up trusted subdomains of governments, universities, and Fortune 500 firms to distribute scams, faux apps, and malicious adverts.
In keeping with Infoblox researchers, Hazy Hawk first scans for domains with CNAME information pointing to deserted cloud endpoints, which they decide by way of passive DNS knowledge validation.
Subsequent, they register a brand new cloud useful resource with the identical identify because the one within the deserted CNAME, inflicting the unique area’s subdomain to resolve to the menace actor’s new cloud-hosted web site.
Utilizing this method, the menace actors hijacked a number of domains to cloak malicious actions, host rip-off content material, or use them as redirection hubs for rip-off operations.
Some notable examples of the hijacked domains embrace:
- cdc.gov – U.S. Facilities for Illness Management and Prevention
- honeywell.com – Multinational conglomerate
- berkeley.edu – College of California, Berkeley
- michelin.co.uk – Michelin Tires UK
- ey.com, pwc.com, deloitte.com – World “Large 4” consulting companies
- ted.com – Well-known nonprofit media group (TED Talks)
- well being.gov.au – Australian Division of Well being
- unicef.org – United Nations Kids’s Fund
- nyu.edu – New York College
- unilever.com – World Client Items Firm
- ca.gov – California State Authorities
The entire record of compromised domains will be discovered within the Infoblox report.
As soon as the menace actor good points management of a subdomain, they generate tons of of malicious URLs underneath it, which seem legit in search engines like google as a result of mother or father area’s excessive belief rating.
Victims clicking on the URLs are redirected by layers of domains and TDS infrastructure that profile them based mostly on their machine kind, IP handle, VPN use, and so on., to qualify victims.
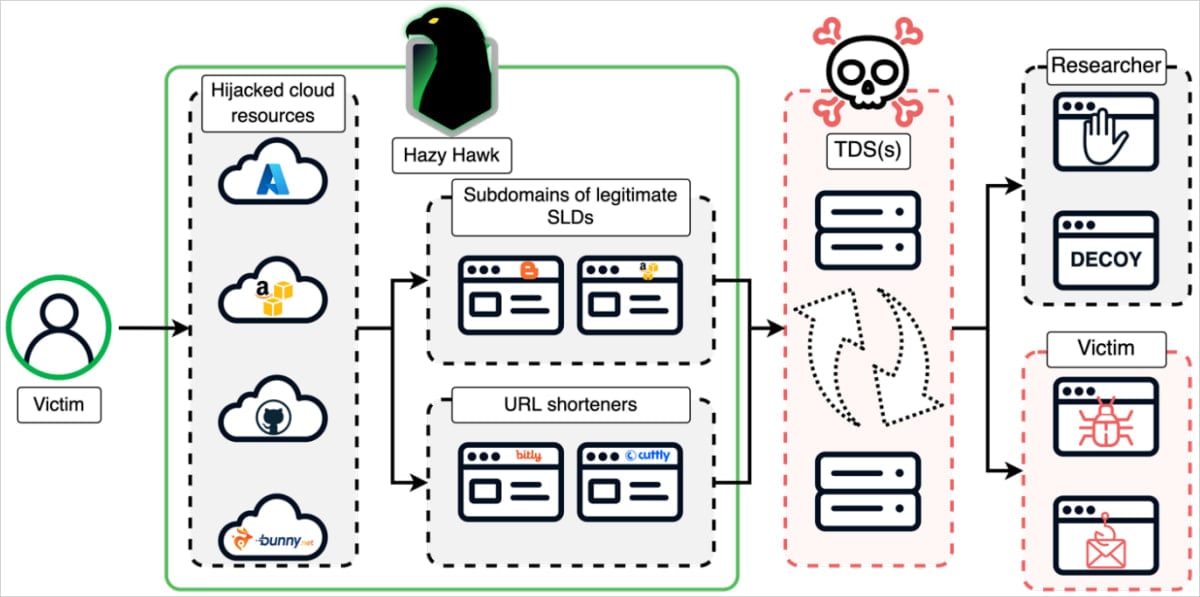
Supply: Infoblox
Infoblox’s report says the websites are used for tech assist scams, bogus antivirus alerts, faux streaming/porn websites, and phishing pages.
Customers tricked into permitting browser push notifications get persistent alerts even after they depart the rip-off websites, which may generate important income for Hazy Hawk.
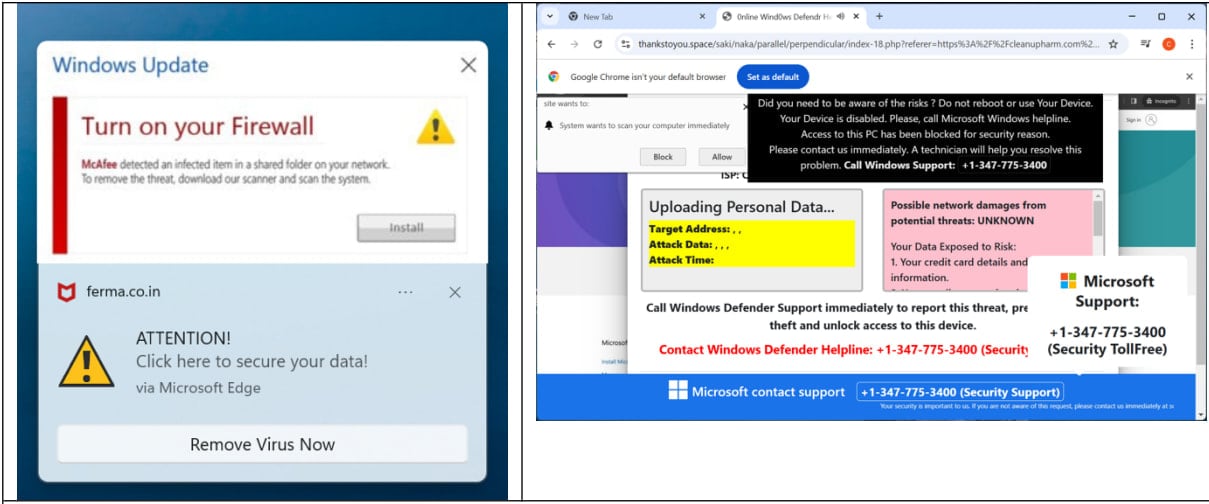
Supply: Infoblox
The identical researchers reported beforehand about one other menace actor, ‘Savvy Seahorse,’ who additionally abused CNAME information to construct an atypical TDS that redirected customers to faux funding platforms.
It is easy to miss CNAME information, so they’re susceptible to stealthy abuse, and it seems that an growing variety of menace actors notice this and try to take benefit.
Within the case of Hazy Hawk, the operation’s success additionally depends on organizations failing to delete DNS information after cloud providers are decommissioned, which allows attackers to duplicate the unique useful resource identify with out authentication.


