
Hackers trojanized installers for the DAEMON Instruments software program and since April 8, delivered a backdoor to 1000’s of programs that downloaded the product from the official web site.
The availability-chain assault led to 1000’s of infections in additional than 100 nations. Nonetheless, second-stage payloads had been deployed solely to a dozen machines, indicating a focused assault aimed toward high-value targets.
Among the many victims receiving next-stage payloads are retail, scientific, authorities, and manufacturing organizations in Russia, Belarus, and Thailand.
A report right now from cybersecurity firm Kaspersky notes that the assault is ongoing and that trojanized software program contains DAEMON Instruments variations from 12.5.0.2421 by means of 12.5.0.2434, particularly the DTHelper.exe, DiscSoftBusServiceLite.exe, and DTShellHlp.exe binaries.
DAEMON Instruments is a Home windows utility that permits mounting disk picture information as digital drives. The software program was extraordinarily fashionable within the 2000s, particularly amongst players and energy customers, however right now its deployment is proscribed to environments the place digital drive administration is required.
As of right now, Kaspersky says that the assault is ongoing.
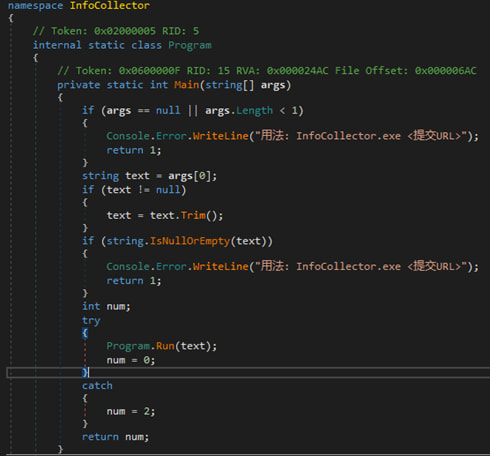
As soon as unsuspecting customers obtain and execute the digitally signed trojanized installers, they set off the malicious code embedded within the compromised binaries. The payload establishes persistence and prompts a backdoor on system startup.
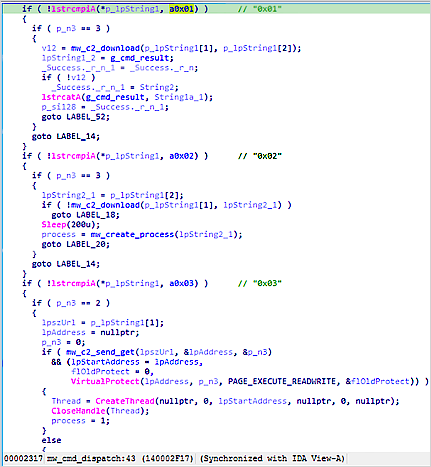
The server can reply with instructions that instruct the system to obtain and execute extra payloads.
The primary-stage malware is a primary info stealer that collects system knowledge, similar to hostname, MAC handle, operating processes, put in software program, and system locale, and sends them to the attackers for sufferer profiling.
Supply: Kaspersky
Primarily based on the outcomes, some programs obtain a second stage, which is a light-weight backdoor that may execute instructions, obtain information, and run code immediately in reminiscence.
Supply: Kaspersky
In not less than one case concentrating on a Russian instructional institute, Kaspersky noticed the deployment of a extra superior malware pressure dubbed QUIC RAT, which helps a number of communication protocols and might inject malicious code into reliable processes.
BleepingComputer has contacted DAEMON Instruments with a request for a touch upon the availability chain assault, however we’ve got not heard again by publication.
Kaspersky describes the DAEMON Instruments supply-chain assault as a sufficiently subtle compromise that evaded detection for nearly one month.
“Given the excessive complexity of the assault, it’s paramount for organizations to fastidiously look at machines that had DAEMON Instruments put in, for irregular cybersecurity-related actions that occurred on or after April 8,” the researchers say.
Though Kaspersky doesn’t attribute the assault to a specific risk actor, primarily based on strings discovered within the first-stage payload, the researchers consider that the attacker is Chinese language talking.
Because the starting of the 12 months, software program supply-chain assaults have been detected virtually each month: eScan in January, Notepad++ in February, CPU-Z in April, and DAEMON Instruments this month.
Comparable assaults concentrating on code repositories, packages, and extensions have been much more prevalent this 12 months, with Trivy, Checkmarx, and the Glassworm campaigns being among the many most outstanding.
AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of recent exploits is coming.
On the Autonomous Validation Summit (Could 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls maintain, and closes the remediation loop.


