ESET Analysis has found a brand new China-aligned APT group that we’ve named GopherWhisper, which targets Mongolian governmental establishments
23 Apr 2026
•
,
6 min. learn

ESET researchers have found a beforehand undocumented China-aligned APT group that we named GopherWhisper. The group wields a big selection of instruments principally written in Go, utilizing injectors and loaders to deploy and execute varied backdoors in its arsenal. Within the noticed marketing campaign, the menace actors focused a governmental entity in Mongolia.
GopherWhisper abuses respectable providers, notably Discord, Slack, Microsoft 365 Outlook, and file.io for command and management (C&C) communication and exfiltration. Crucially, after we recognized a number of Slack and Discord API tokens, we managed to extract numerous C&C messages from these providers, which offered us with nice perception into the group’s actions.
This blogpost summarizes the findings from our investigation of GopherWhisper’s toolset and C&C visitors, which may be present in our white paper on the subject.
Key factors of the blogpost:
- ESET Analysis uncovered a brand new China-aligned APT group we’ve named GopherWhisper that focused a governmental entity in Mongolia.
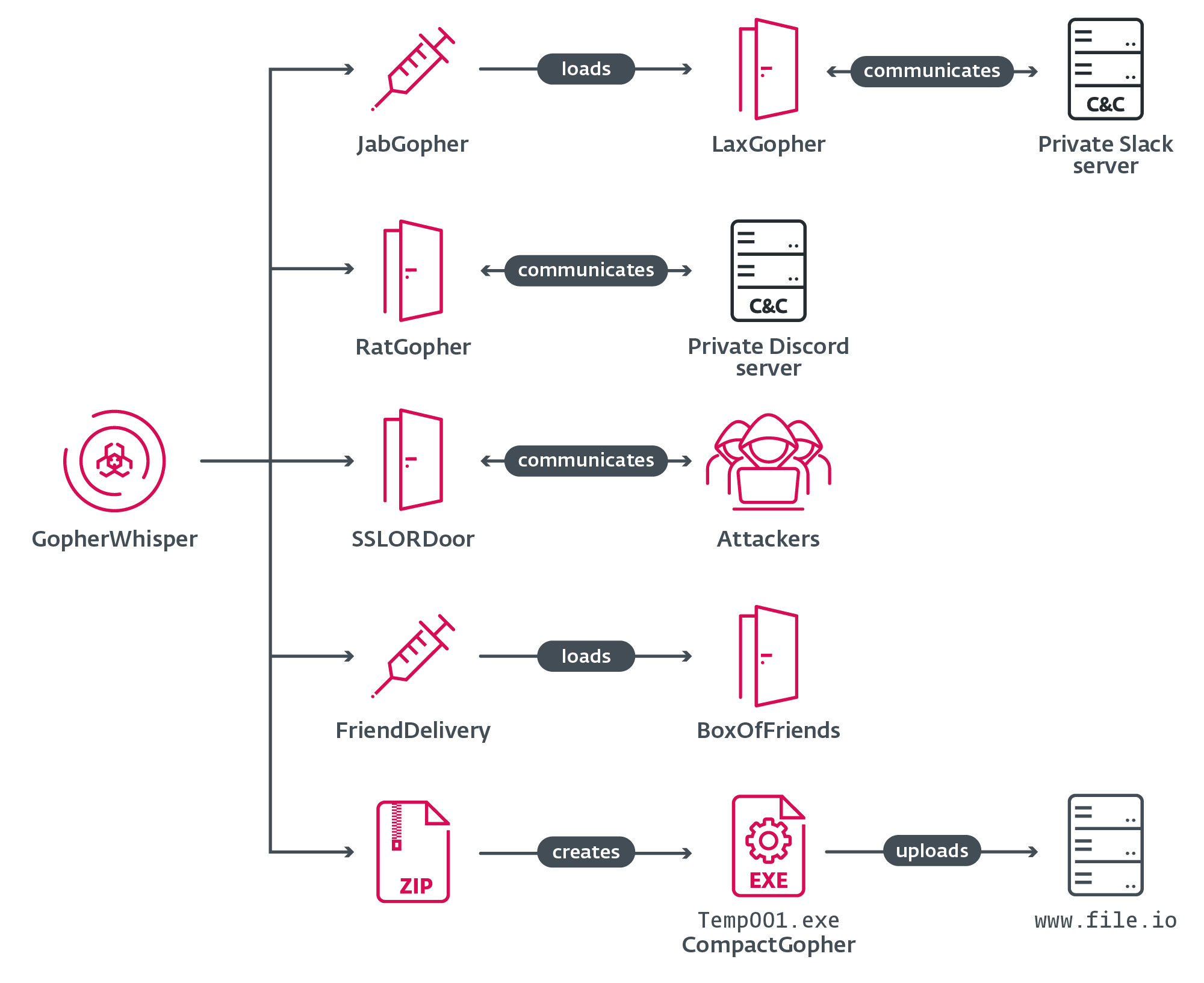
- The group’s toolset contains customized Go-based backdoors LaxGopher, RatGopher, and BoxOfFriends, the injector JabGopher, the exfiltration device CompactGopher, the loader FriendDelivery, and the C++ backdoor SSLORDoor.
- GopherWhisper leverages Discord, Slack, Microsoft 365 Outlook, and file.io for C&C communications and exfiltration.
- We analyzed C&C visitors from the attacker’s Slack and Discord channels, gaining details about the group’s inner operations and post-compromise actions.
Backdoors galore
We found the group in January 2025, once we discovered a beforehand undocumented backdoor, which we named LaxGopher, on the system of a governmental entity in Mongolia. Digging deeper, we managed to uncover a number of extra malicious instruments, primarily varied backdoors, all deployed by the identical group. The vast majority of these instruments, together with LaxGopher, are written in Go.
Because the set of malware we discovered has no code similarities linking it to any recognized menace actor, and there was no overlap in ways, methods, and procedures (TTPs) with another group, we determined to attribute the instruments to a brand new group. We selected to call it GopherWhisper because of the majority of the group’s instruments being written within the Go programming language, which has a gopher as its mascot, and based mostly on the filename whisper.dll, a malicious part that’s side-loaded.
The malware we initially found consists of the next:
- JabGopher: an injector that executes the LaxGopher backdoor disguised as whisper.dll. It creates a brand new occasion of svchost.exe and injects LaxGopher into the svchost.exe course of reminiscence.
- LaxGopher: a Go-based backdoor that interacts with a personal Slack server to retrieve C&C messages. It executes instructions by way of cmd.exe and publishes the outcomes again to the Slack channel configured within the code. LaxGopher may obtain additional malware to the compromised machine.
- CompactGopher: a Go-based file assortment device deployed by operators to shortly compress information from the command line and robotically exfiltrate them to the file.io file sharing service. It is likely one of the payloads deployed by LaxGopher.
- RatGopher: a Go-based backdoor that interacts with a personal Discord server to retrieve C&C messages. On profitable execution of a command, the outcomes are printed again to the configured Discord channel.
- SSLORDoor: a backdoor in-built C++ that makes use of OpenSSL BIO for communication by way of uncooked sockets on port 443. It may enumerate drives, and run instructions based mostly on C&C enter, primarily associated to opening, studying, writing, deleting, and importing information.
Primarily based on the data we gained throughout our evaluation, we have been capable of finding two further GopherWhisper instruments, which have been once more deployed in opposition to the identical Mongolian governmental entity:
- FriendDelivery: a malicious DLL file serving as a loader and injector that executes the BoxOfFriends backdoor.
- BoxOfFriends: a Go-based backdoor that makes use of the Microsoft 365 Outlook mail REST API from Microsoft Graph to create and modify draft e mail messages for its C&C communications.
A schematic overview of GopherWhisper’s arsenal is offered in Determine 1.
Revealing messages
As talked about within the introduction, GopherWhisper is characterised by the in depth use of respectable providers comparable to Slack, Discord, and Outlook for C&C communication. Throughout our investigation, we managed to extract hundreds of Slack and Discord messages, in addition to a number of draft e mail messages from Microsoft Outlook. This gave us nice perception into the inside workings of the group.
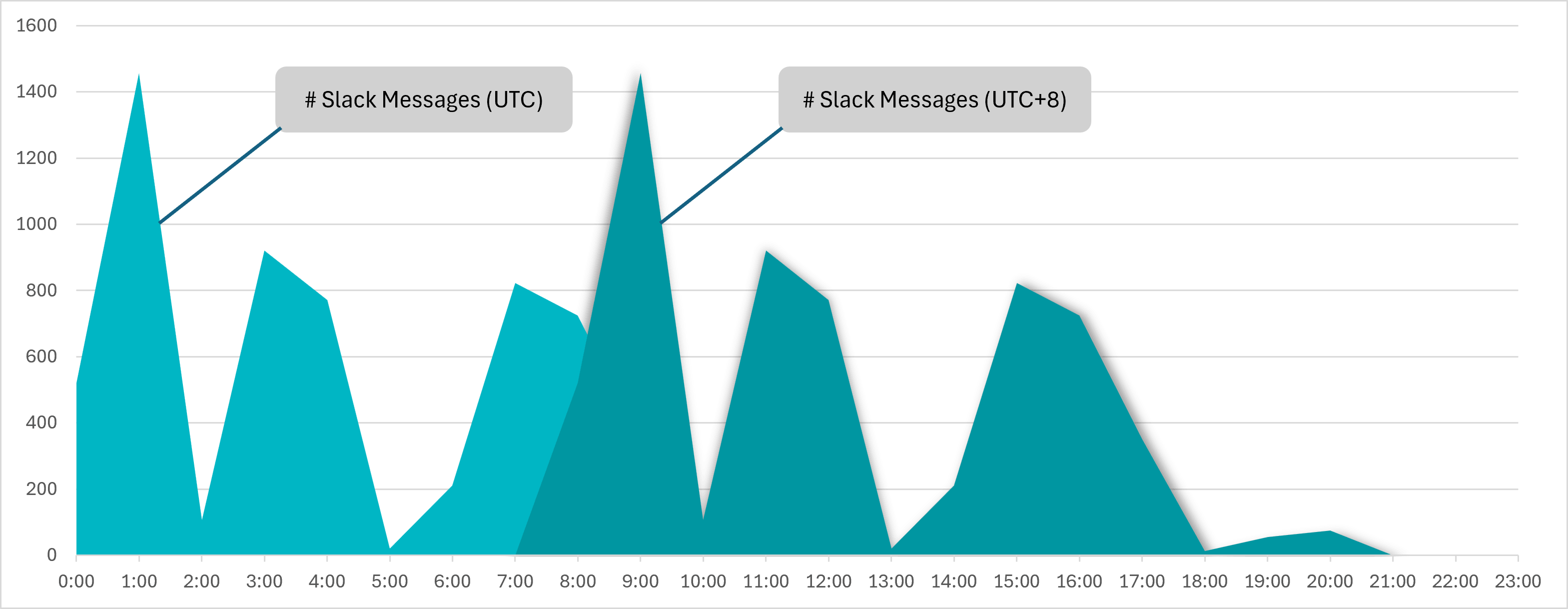
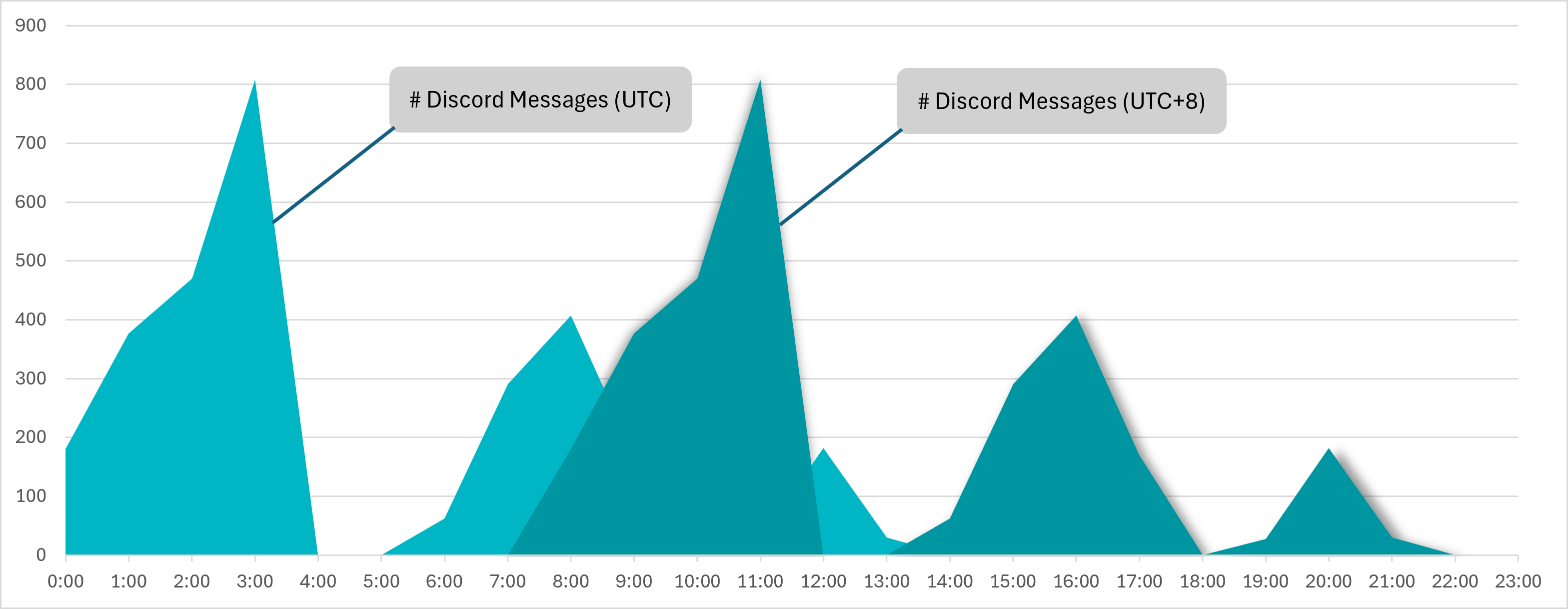
Timestamp inspection of the Slack and Discord messages confirmed us that the majority of them have been despatched throughout working hours, i.e. between 8 am and 5 pm, in UTC+8 (see Determine 2 and Determine 3), which aligns with China Commonplace Time. Moreover, the locale for the configured consumer in Slack metadata was additionally set to this time zone. We due to this fact consider that GopherWhisper is a China-aligned group.
Primarily based on our investigation, the group’s Slack and Discord servers have been first used to check the performance of the backdoors, after which later, with out clearing the logs, additionally used as C&C servers for the LaxGopher and RatGopher backdoors on a number of compromised machines.
LaxGopher’s Slack channel
The messages we collected revealed that LaxGopher C&C communications have been primarily used to ship instructions for disk and file enumeration.
As well as, a number of attention-grabbing hyperlinks to GitHub repositories with malicious code have been found among the many Slack messages, as listed in Desk 1. Primarily based on the supply code of every repository, we assume that these repositories may have been used as a useful resource for studying and a reference throughout growth.
Desk 1. GitHub repositories discovered inside take a look at uploads from operators
RatGopher’s Discord channel
Aside from C&C communication, RatGopher’s Discord channel additionally contained Go supply code which will have been an early iteration of the backdoor.
Moreover, we have been capable of get hold of particulars about operator machines, since they typically used them to run enumeration processes for testing functions. This confirmed us, amongst different issues, that an operator used a digital machine based mostly on VMware, and that the machine had been booted and put in at a time that aligns very properly with the UTC+8 time zone.
Microsoft 365 Outlook communication
Along with the Slack and Discord communication, we have been additionally capable of extract e mail messages used for communication between the BoxOfFriends backdoor and its C&C by way of the Microsoft Graph API. There we observed that the welcome e mail message from Microsoft, from when the account was created, had by no means been deleted. This message confirmed that the account barrantaya.1010@outlook[.]com was created on July 11th, 2024, simply 11 days earlier than the creation of the FriendDelivery DLL – the loader used to execute BoxOfFriends – on July 22nd, 2024.
Conclusion
Our investigation into GopherWhisper revealed an APT group that makes use of a assorted toolset of customized loaders, injectors, and backdoors. By analyzing the C&C communications obtained from the attacker-operated Slack and Discord channels, and from draft Outlook e mail messages, we have been capable of acquire further details about the group’s inside workings and post-compromise actions.
For an in depth evaluation of the toolset and the obtained C&C visitors, learn our full white paper.
A complete checklist of indicators of compromise (IoCs) may be present in the white paper and in our GitHub repository.



