Silver Fox is again in Japan, spoofing tax and HR emails timed to the one season when nobody thinks twice about opening them
27 Mar 2026
•
,
4 min. learn

Japan has entered its annual tax submitting and organizational change season, a interval when corporations generate a excessive quantity of official monetary and HR‑associated communications. A risk actor often known as Silver Fox is actively exploiting this busy interval by conducting a focused spearphishing marketing campaign in opposition to Japanese producers and different companies.
The continuing marketing campaign makes use of convincing phishing lures associated to tax compliance violations, wage changes, job place modifications, and worker inventory possession plans. All emails share the identical objective – trick the recipients into opening malicious hyperlinks or attachments. As workers truly count on to obtain emails about these topics this time of 12 months, they’re extra prone to belief and act on such messages with no second thought. For sure, this considerably will increase the danger of compromise.
The operation can also be a reminder for organizations to extend vigilance, reinforce consciousness round phishing makes an attempt, and be certain that workers confirm the authenticity of tax‑ and HR‑themed requests – together with people who look routine. Instant reporting of suspicious emails to safety groups is crucial to scale back publicity and stop profitable compromise.
What’s the risk?
Lively since no less than 2023, Silver Fox initially centered on Chinese language-speaking targets earlier than increasing into Southeast Asia, Japan, and doubtlessly North America, operating every marketing campaign in an area language. This broadened scope exhibits within the vary of verticals the group has hit through the years – finance, healthcare, schooling, gaming, authorities and even cybersecurity. The group additionally primarily operates in Southeast Asia and has a well-documented historical past of finance-themed spearphishing campaigns throughout seasonal enterprise cycles.
Within the ongoing marketing campaign, the group is making the most of Japan’s annual cycle of tax submitting, monetary reporting, wage changes, and personnel modifications. This sample isn’t new – comparable exercise was noticed throughout the identical interval final 12 months, indicating that Silver Fox intentionally aligns its operations with this season. The quantity and urgency of official inner communication round these matters is excessive this time of 12 months, which is strictly what Silver Fox is relying on and what makes its campaigns efficient.
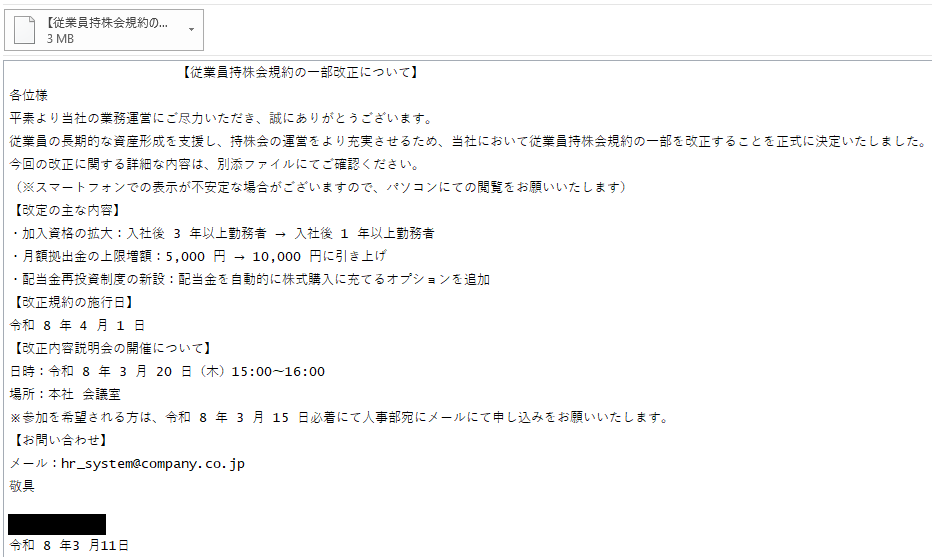
On this operation, Silver Fox sends tailor-made spearphishing emails crafted to appear like official HR or tax-related messages. To make the emails seem genuine, the attackers typically embody the identify of the focused firm immediately within the topic line. Examples of topics noticed on this marketing campaign embody:
- 「会社名 」【従業員持株会規約改正に関するお知らせ】
(Translation:Discover of amendments to the ESOP phrases and situations]) - 「会社名 」【従業員持株会規約の一部改正について】
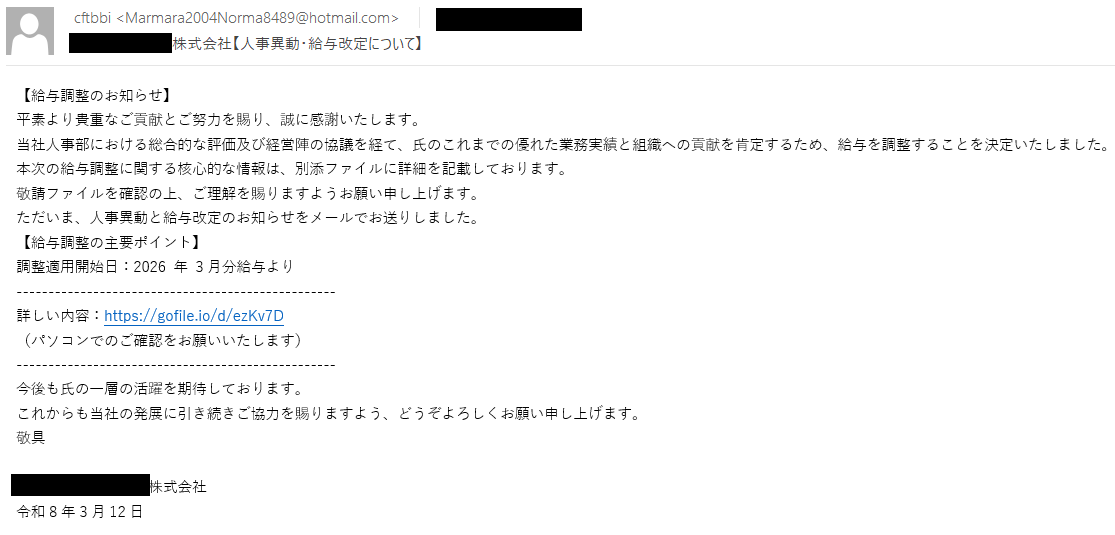
(Translation:[Revisions to the ESOP Terms and Conditions]) - 「会社名 」【人事異動・給与改定について】
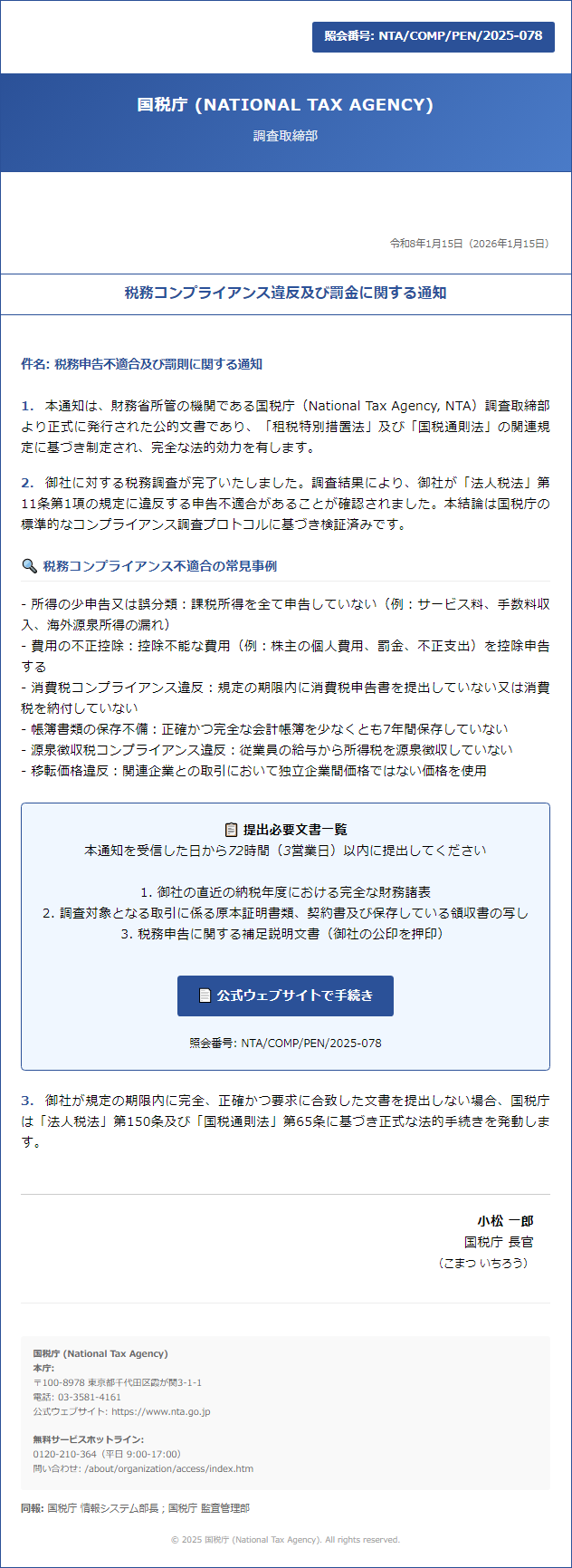
(Translation:[Personnel Changes and Salary Adjustments]) - 税務コンプライアンスおよび罰金通知
(Translation: Tax Compliance and Penalty Discover)
The sender fields impersonate actual workers and even CEOs on the focused corporations. Silver Fox is clearly performing some reconnaissance on every goal earlier than sending what aren’t generic blasts. The attackers are selecting names that the targets are prone to acknowledge and belief, which makes it harder for the recipients to tell apart the malicious messages from actual inner notifications.
The emails sometimes comprise both a malicious attachment or a hyperlink resulting in a malicious file. The recordsdata are named to resemble frequent HR, monetary, or tax-related paperwork, equivalent to:
- 【給与調整のお知らせ】
(Translation: Wage Adjustment Discover) - 人事異動・給与改定について
(Translation: Personnel Adjustments and Wage Changes) - 人事異動及び給与改定に関するお知らせ
(Translation: Discover relating to personnel modifications and wage changes) - 【従業員持株会規約の一部改正について】
(Translation: [Partial amendment to the Employee Stock Ownership Plan terms and conditions])
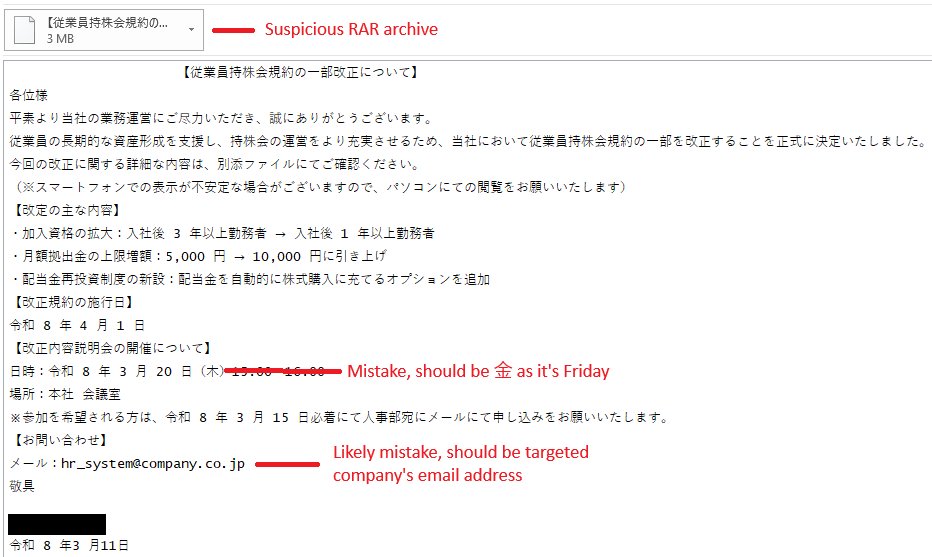
The next are examples of noticed emails and lures:
Opening the malicious recordsdata drops ValleyRAT, a distant entry trojan that Silver Fox has used throughout a number of campaigns. ESET merchandise detect this malware as Win64/Valley. As soon as deployed, ValleyRAT permits the actor to take distant management of the compromised machine, harvest delicate info, monitor person exercise, and keep persistence within the focused atmosphere. This could enable the attacker to burrow deeper into the community, steal confidential knowledge, or put together further levels of an assault.
Methods to acknowledge the risk and shield your self
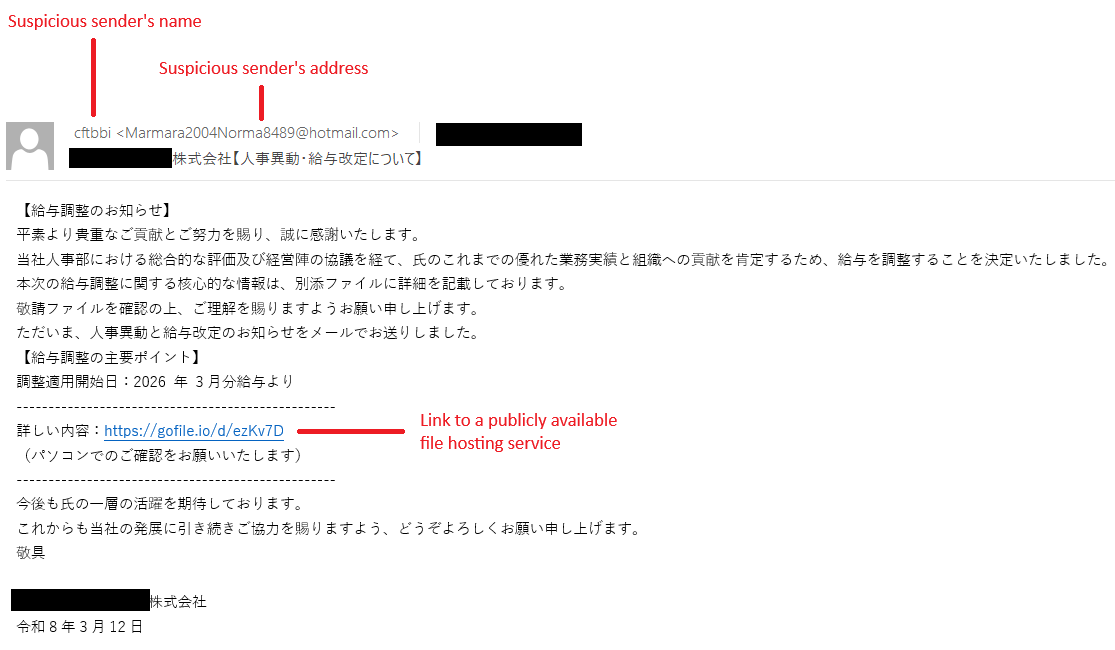
Whereas Silver Fox’s emails could seem credible on the first look, particularly throughout Japan’s busy tax and organizational change season, a better look reveals hints rendering the emails suspicious. The next indicators are the important thing to recognizing and stopping the assault:
- In the event you obtain an e mail about wage modifications, tax penalties, or personnel updates, confirm it by way of a separate channel (Groups, telephone, or direct e mail lookup) earlier than appearing on it. This is applicable even when the message seems to be routine.
- Even when the sender’s identify belongs (or appears to belong) to a colleague, be sure that the e-mail handle and the identify match. In the event that they don’t or the handle seems to be unfamiliar, deal with the e-mail as suspicious.
- Ask your self whether or not this communication follows your organization’s regular HR or Finance course of.
- Be cautious if the language feels overly formal, stiff, or mismatched with typical inner communications. Because the risk actor shouldn’t be a local Japanese speaker, the emails could comprise awkward phrasing and delicate giveaways.
- Paperwork are unlikely to be shared by way of a publicly obtainable file internet hosting companies equivalent to gofile[.]io or WeTransfer.
- Take note of the attachment kind. If it’s an archive equivalent to RAR or ZIP, have a look at what’s truly inside earlier than opening the recordsdata.
- Set up software program updates when prompted.
- Guarantee your safety software program is operating and up-to-date.
- If one thing feels off about an e mail, ahead it as an attachment to your IT or safety group. Reporting is rarely a mistake – even when the e-mail seems to be official.
The next are illustrative examples of what to be careful for:
IoCs
A complete checklist of indicators of compromise (IoCs) and samples may be present in our GitHub repository.



