Begin utilizing a brand new app and also you’ll typically be requested to grant it permissions. However blindly accepting them may expose you to severe privateness and safety dangers.
27 Feb 2026
•
,
5 min. learn

App permissions are virtually like an invisible sentry, governing what sort of knowledge and gadget entry your apps get. For those who’ve ever downloaded a brand new app or activated a brand new characteristic, the possibilities are you’ll have been introduced with a permissions immediate. However how many people have absent-mindedly clicked “enable” with out pondering?
Some permissions are applicable for the app. However some might (deliberately or not) push the boundaries of what’s strictly mandatory. And others could possibly be outright malicious. It’s vital to know which to wave by way of and which to dam.
What’s the take care of app permissions?
An app permission pop-up is basically a dialog between your cellular OS and your self. It’s successfully telling you {that a} new utility has requested to entry sure information or options. And it’s asking your approval (permission) for the app to take action. These requests used to return pre-installation. However fashionable iOS variations floor permissions prompts at runtime, if you first begin utilizing the app. Android does each, popping up install-time prompts just for low-risk permissions.
Since Android 6.0, permissions fall into two classes: regular permissions, similar to web entry, that are granted silently at set up time with no person immediate, and harmful permissions, similar to location, microphone, or contacts, which have to be explicitly authorised by the person at runtime ( if you first try to make use of the related characteristic). Newer variations have additionally launched extra permissions, similar to background location and notifications, which will require separate or multi-step consent flows. iOS surfaces all delicate permissions at runtime in an identical manner.
For builders, permissions are a vital solution to ship seamless, feature-rich experiences to customers. If an app needed to request entry to gadget information/features every time it used them, it could be virtually unusable.
Each iOS and Android have launched significant built-in protections lately that mitigate the dangers related to granting extreme privileges to apps. Nonetheless, the ultimate determination normally rests with you.
The hazards of app permissions
Whether or not maliciously or in any other case, some apps ask for extra entry than they want. Consider a cellular recreation asking for entry to your contacts, or a calculator app requesting permission to entry your mic and digicam, for instance.
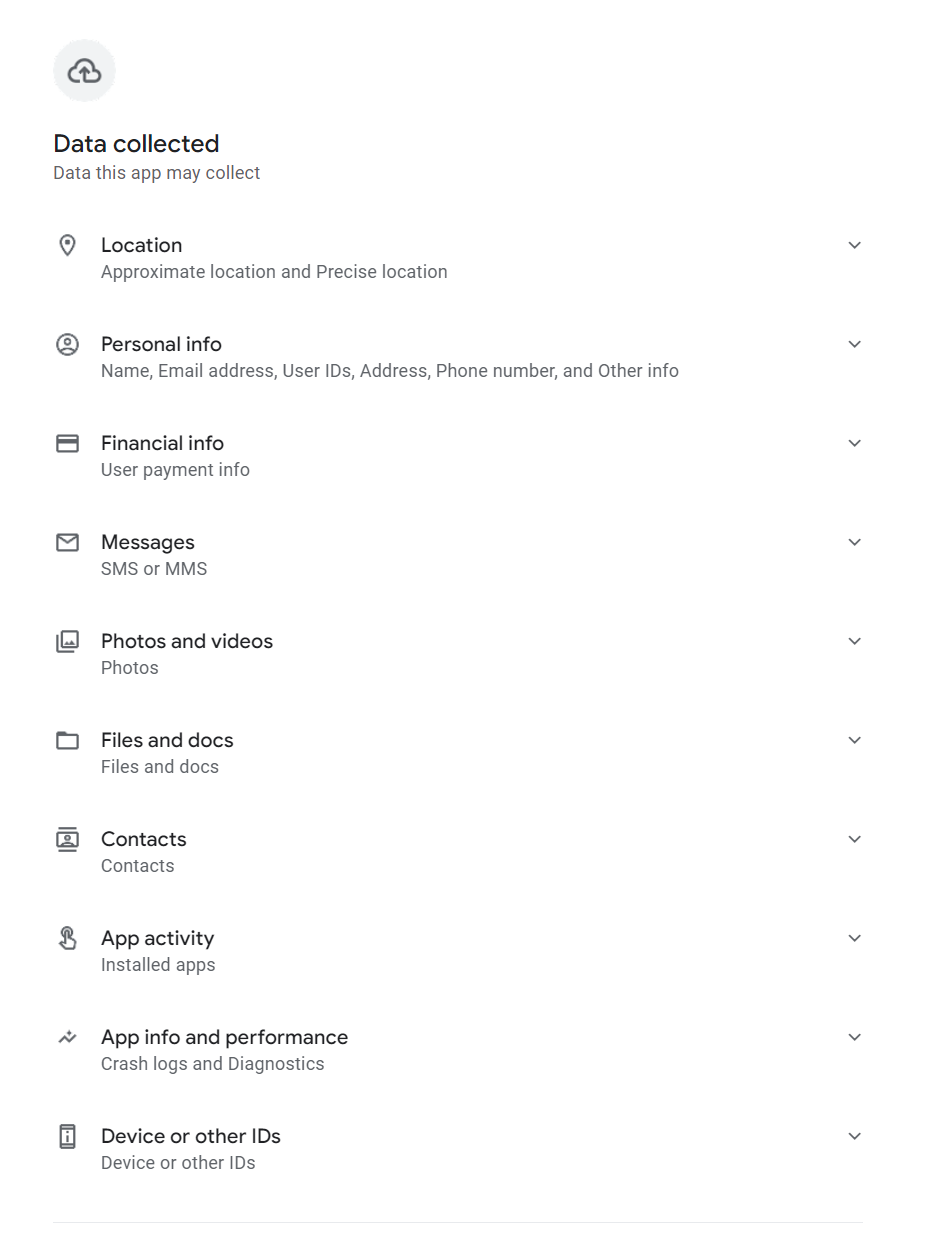
By approving permissions with out taking time to consider it, you would possibly allow malicious builders to entry delicate smartphone information (calendar, messaging apps, SMS, recordsdata and storage, contacts, name logs, location, mic and digicam and so on). They may theoretically even learn your display as you sort. With this entry they might:
Harvest passwords to your most delicate accounts (e.g., on-line banking)
- Intercept one-time SMS passcodes
- Enrol your gadget in premium-rate subscription providers
- Construct up an image of your digital life to promote to advertisers
- Put your bodily security in danger by monitoring your location
- Swap on digicam/mic to show your smartphone right into a bugging gadget
- Encrypt your recordsdata and maintain them to ransom
- Instal malware in your gadget (e.g., infostealers, ransomware)
AI assistant apps (to not point out apps masquerading as such) signify a rising permissions threat value singling out. Many request always-on microphone entry for wake-word detection, in addition to contacts, calendar, and in some circumstances display content material. Deal with AI apps with the identical scrutiny as every other class. Well being and health information is one other underappreciated publicity. Apps with entry to your well being metrics can share or promote that information in methods with real-world penalties, together with implications for insurance coverage and information brokerage.
Which app permissions ought to ring alarm bells?
App permissions depend upon context. What one app requests to ship the expertise customers count on could also be very totally different to the permissions one other wants. Nonetheless, there are particular permissions that ought to all the time increase some crimson flags. They embody:
- Accessibility providers: Also referred to as “God mode,” this might enable malicious builders to see what you sort, learn your messages and covertly grant itself different permissions with out you figuring out. (Observe, this isn’t natively obtainable on iOS. New Android OS variations is not going to enable apps put in exterior of the Play Retailer to request this permission. And they’ll examine each few weeks whether or not you need to proceed granting this permission.)
- Background location: This might allow a malicious actor to trace your gadget all over the place you go, to construct an in depth image of your each day life. (Observe: to mitigate this threat, Android and iOS gained’t allow you to “all the time enable” up entrance, and they’re going to periodically ask you to verify you need to keep “all the time enable” monitoring).
- SMS/name logs: Few apps really want entry to your textual content messages and name historical past. By doing so, a hacker may learn your one-time passcodes and hijack your accounts. (Observe: For an app to ask for these permissions on Android, it should first be registered because the Default App for that operate. iOS doesn’t enable any apps downloaded from the App Retailer to request permission to “Learn SMS” or “See Name Historical past.”)
- Overlay permission: Permits an app to attract a “window” on prime of one other app you may be utilizing, which may allow “clickjacking” assaults. (Observe: Android requires customers to explicitly allow this by way of Settings > Apps > Particular App Entry > Seem on prime. iOS doesn’t have an identical permission).
Managing app permissions safely
Earlier than permitting or blocking, all the time take into account if a permission is critical for the app in query to do its job.
One other good rule of thumb is to solely “enable as soon as” or “whereas utilizing.” Solely security apps like “Discover My” ought to actually have entry 24/7/365.
You need to be requested to evaluation your permissions repeatedly with many apps. However it could be a good suggestion to proactively audit permissions. Right here’s how:
iOS
- Go to Settings > Privateness & Safety.
- Scroll to the underside and faucet (or activate) App Privateness Report.
- This reveals you which ones apps accessed your information and when.
Alternatively:
- Go to Settings > Apps.
- Choose a selected app (e.g., Instagram).
- You will note an inventory of all toggles (Digital camera, Mic, Contacts). Flip off something that is not important.
Android
- Go to Settings > Safety & Privateness > Privateness > Privateness Dashboard.
- Faucet on 7-Day View (prime proper menu) to see a timeline of each app that used your sensors over the past week. (These steps will not be the identical throughout all Android-powered units, so do examine.)
- For those who see an app utilizing the microphone at 3:00 AM, faucet it to revoke entry instantly.
Alternatively (navigation paths nonetheless differ throughout Android skins):
- Go to Settings > Apps > [App Name].
- Guarantee “Handle app if unused” (or “Pause app exercise if unused”) is toggled ON.
- For those who do not use the app for a number of months, Android will mechanically strip its permissions, delete non permanent recordsdata, and cease notifications.
Above all, solely ever obtain apps from official shops (Google Play/App Retailer). Learn their critiques first earlier than deciding whether or not to take action. Contemplate putting in a cellular safety answer from a good safety supplier.
Keep secure!


