As organizations plan their defenses for the instant future, 51% of companies rank cybersecurity assaults and breaches as the highest danger to their efficiency in 2026.
On the similar time, the ratio of cybersecurity spending to monetary losses is staggering; whereas world spending was $185 billion in 2024 towards $9.22 trillion in losses, this hole is projected to extend to 68 instances by 2030, with $262 billion in spending versus $18 trillion in losses.
This stark monetary actuality exhibits that conventional protection mechanisms are not adequate. On this weblog, we’ll give attention to AI for Cybersecurity, defensive methods, danger administration, and workforce adaptation that should structurally change to handle the evolution of automated and clever threats.
Summarize this text with ChatGPT
Get key takeaways & ask questions
The Rising Dynamics of AI-Pushed Threats
The normal mannequin of cybersecurity relied on figuring out recognized patterns of malicious code, however the introduction of machine studying has allowed attackers to maneuver past these predictable strategies.
Trendy threats at the moment are characterised by their potential to be taught from the environments they infect, making them tougher to trace and neutralize utilizing customary software program.
Attackers are utilizing synthetic intelligence in cybersecurity not simply to maneuver quicker, however to create extremely customized campaigns that exploit human psychology and system vulnerabilities concurrently.
The evolution of those ways is outlined by a number of crucial developments in how malicious actors make the most of automated intelligence:
- Autonomous and Self-Evolving Malware: Malicious software program not requires fixed directions from a central server to execute its mission. As a substitute, it may possibly enter a community and independently analyze the surroundings to search out probably the most worthwhile information or the weakest safety factors, usually altering its personal code to keep away from being detected by antivirus scanners.
- Hyper-Customized Social Engineering: By processing huge quantities of public information, attackers can generate phishing emails or messages that completely mimic the tone and elegance of a trusted colleague or government. This removes the frequent warning indicators of fraud, reminiscent of poor grammar or generic greetings, making these assaults extremely profitable.
- Adversarial Manipulation of Protection Programs: As a result of many safety instruments now use synthetic intelligence to detect threats, attackers have begun focusing on the logic of those instruments. By introducing “poisoned” information right into a system’s studying course of, they’ll trick the safety software program into ignoring particular kinds of malicious exercise.
- Giant-Scale Vulnerability Discovery: Automated instruments can scan hundreds of thousands of traces of code in seconds to search out “zero-day” vulnerabilities that haven’t but been found by software program builders. This permits attackers to take advantage of weaknesses in frequent functions earlier than a patch will be created or deployed.
These developments imply that the window of time obtainable to reply to an assault has shrunk from days to seconds.
When threats can assume and adapt on their very own, a handbook response from a human safety staff is usually too sluggish to stop information theft or system lockdowns.
Organizations should subsequently acknowledge that they’re not simply preventing human hackers, however extremely environment friendly, automated software program brokers.
Strengthening the Core Safety Buildings for Higher Safety
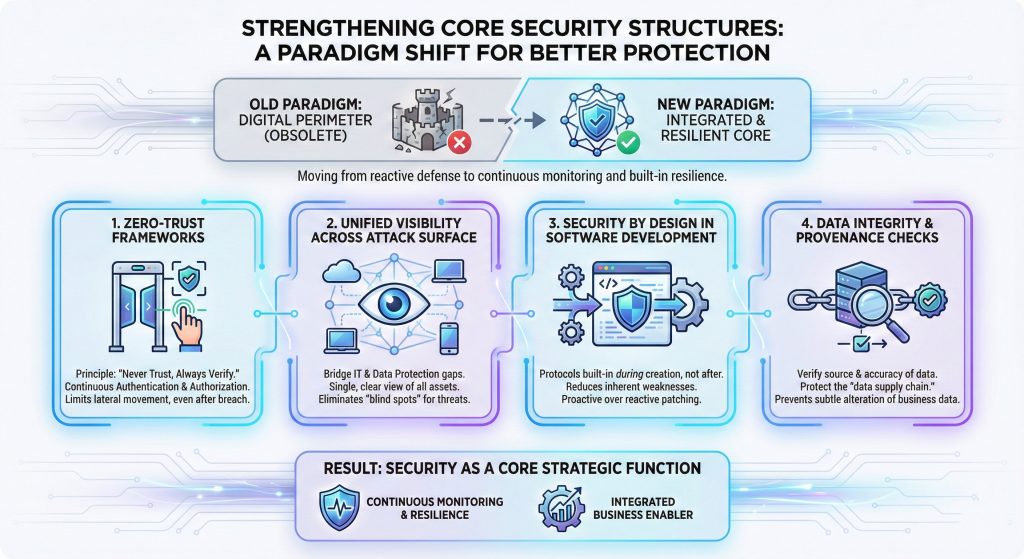
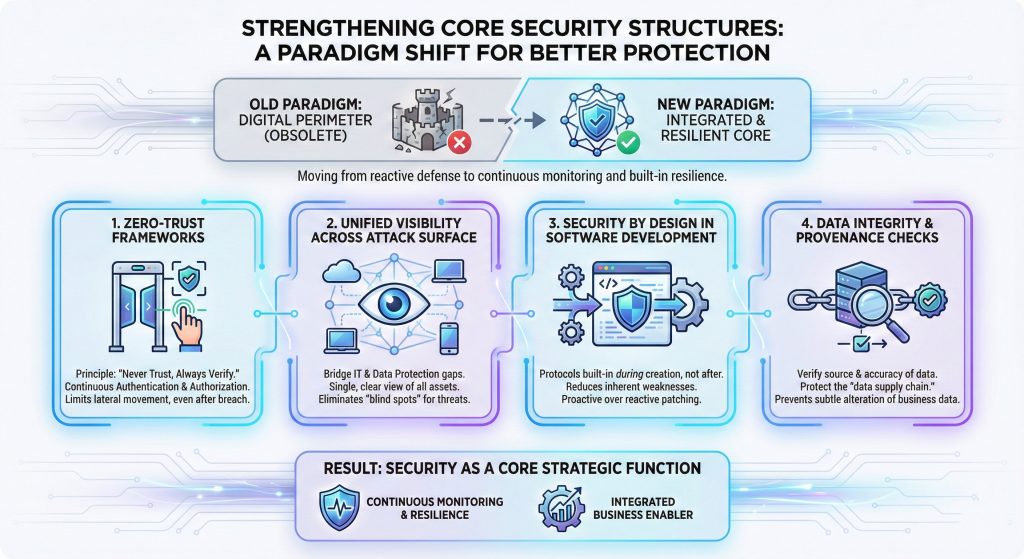
Defending a company on this surroundings requires extra than simply shopping for new software program; it requires an entire change in how a community is constructed and managed.
The outdated thought of a “digital perimeter” the place everybody inside a constructing is trusted, and everybody outdoors is blocked, is not related in a world of distant work and cloud computing.
Safety should now be built-in into each single gadget, software, and person interplay throughout the enterprise ecosystem.
To deal with these vulnerabilities, organizations are transferring towards a extra built-in and disciplined structural mannequin:
- Implementation of Zero-Belief Frameworks: This technique operates on the precept of “by no means belief, at all times confirm.” Each person and gadget should be repeatedly authenticated and approved to entry particular information, guaranteeing that even when an attacker positive factors entry, they can’t transfer freely throughout the complete community.
- Unified Visibility Throughout the Assault Floor: Safety groups should bridge the hole between IT operations and information safety to achieve a single, clear view of all related belongings. This contains figuring out each laptop computer, cloud server, and cell gadget to make sure that no “blind spots” exist the place an automatic menace may cover.
- Safety by Design in Software program Improvement: Reasonably than checking for safety flaws after a product is completed, safety protocols at the moment are constructed into the very starting of the software program creation course of. This reduces the variety of inherent weaknesses that may be exploited later by clever scanning instruments.
- Knowledge Integrity and Provenance Checks: Organizations should implement strict controls to confirm the supply and accuracy of the information they use to coach their very own inside programs. Defending the “information provide chain” ensures that the data used for enterprise selections has not been subtly altered by an out of doors celebration.
By adopting these structural adjustments, companies transfer from reactive protection to steady monitoring and built-in resilience, making safety a core strategic perform somewhat than a separate division.
This shift can be creating sturdy expertise demand, with authorities projections estimating almost 140,100 job openings yearly for software program and safety testing professionals via 2033, highlighting how crucial superior safety experience has turn into to sustained digital development.
For these trying to confidently lead on this evolving digital surroundings, the Certificates Program in Generative AI & Brokers Fundamentals from Johns Hopkins College gives a extremely related, 8-week on-line studying path.
This program requires no programming expertise and equips technical leaders and enterprise professionals with a dependable basis in AI, together with essential modules on accountable AI practices and safety.
How does this program empower your profession?
This government training program is particularly designed to assist professionals leverage synthetic intelligence in cybersecurity whereas understanding the crucial guardrails required for safe enterprise deployment. Right here is the way it immediately advantages you:
- Sort out AI Safety Dangers Head-On: The curriculum dedicates particular focus to Accountable AI, instructing you determine main Giant Language Mannequin (LLM) safety dangers reminiscent of immediate injection, information poisoning, and jailbreaking.
- Apply Safety Frameworks to AI: You’ll learn to actively apply the CIA Triad (Confidentiality, Integrity, Availability) to evaluate and mitigate safety dangers inside LLM deployments.
- Perceive Provide Chain Vulnerabilities: Aligning completely with the necessity for information provenance, this system explains how provide chain vulnerabilities and repair denial can compromise AI reliability and accountability.
- Construct Sensible AI Expertise With out Coding: You’ll be taught to design agentic workflows, perceive Immediate Engineering, and apply AI brokers to enterprise operations, all while not having any prior programming information.
In an period the place cybersecurity and AI have gotten deeply interconnected, packages like this allow professionals to not solely perceive rising applied sciences but additionally deploy them responsibly and securely.
As assaults turn into smarter, defensive instruments should additionally achieve the flexibility to cause and act with out ready for human intervention.
The purpose of a contemporary protection system is to attain “predictive safety,” the place the software program can anticipate an attacker’s subsequent transfer based mostly on delicate adjustments in community habits.
This requires a transition from reactive instruments that fireside alerts after an incident to proactive programs that actively hunt for threats. The effectiveness of those proactive methods depends on a number of key technical capabilities:
- Behavioral Anomaly Detection: As a substitute of on the lookout for a selected virus, these programs be taught what “regular” appears like for each worker and server. If a quiet accountant all of a sudden begins downloading hundreds of encrypted information at midnight, the system acknowledges this as an anomaly and instantly restricts their entry.
- Automated Incident Triage and Response: Superior safety platforms can now deal with the primary levels of an assault mechanically. They’ll isolate contaminated computer systems, block suspicious net visitors, and reset compromised passwords in real-time, permitting human analysts to give attention to investigating the basis trigger.
- Steady Risk Looking: Specialised software program brokers always crawl via a company’s inside logs and exterior menace databases to search out indicators of hidden intruders. This energetic looking helps discover “low and sluggish” assaults that attempt to keep beneath the radar for months.
- Clever Content material Filtering: Communication instruments now use context-aware evaluation to cease deepfake audio or video and phishing makes an attempt earlier than they attain an worker’s inbox, successfully neutralizing the attacker’s most potent instrument.
Utilizing these superior methodologies permits a safety staff to handle a a lot greater quantity of threats than was beforehand potential.
To successfully implement these superior, automated protection mechanisms, from behavioral anomaly detection to steady menace searching, safety professionals want specialised, up-to-date coaching.
Constructing the aptitude to transition a company from a reactive posture to a predictive safety mannequin requires hands-on expertise with trendy instruments and defensive frameworks.
For these able to grasp these proactive methodologies and keep forward of automated threats, exploring industry-aligned Cyber Safety Programs gives the important sensible expertise and strategic information required to confidently fortify any digital infrastructure.
The Position of Agentic Programs in Safety Operations
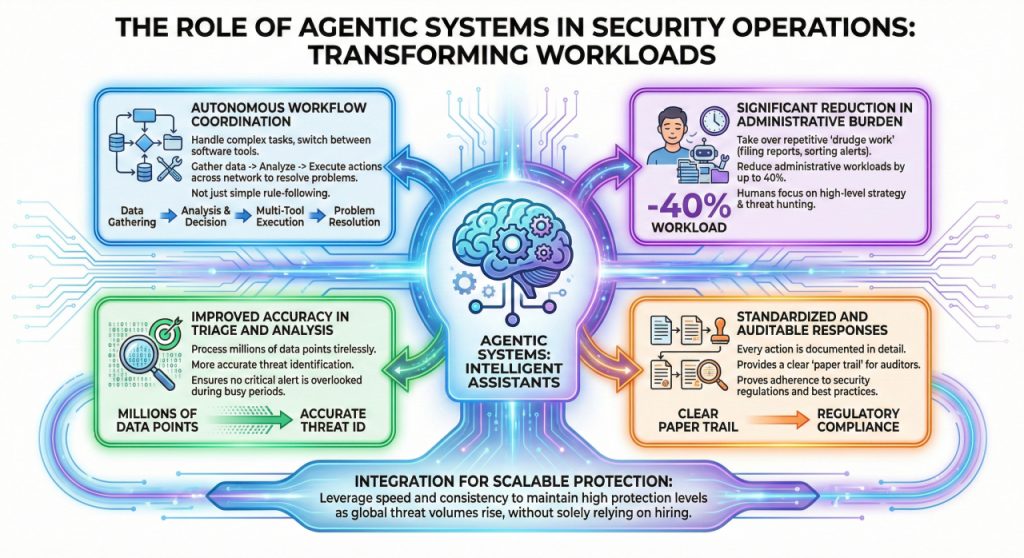
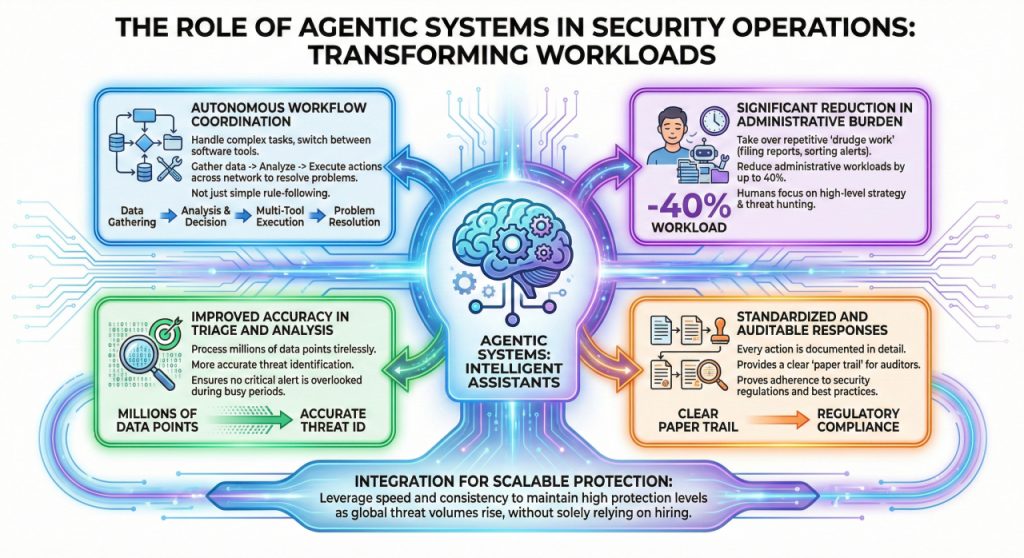
A major breakthrough in managing safety workloads is the usage of “agent” programs that may assume via an issue and execute a number of steps to resolve it. These instruments are reworking the day-to-day operations of safety departments by performing as clever assistants:
- Autonomous Workflow Coordination: In contrast to easy automation that follows one rule, agentic programs can deal with complicated duties that require switching between totally different software program instruments. They’ll collect information, analyze it, after which execute a collection of actions throughout the community to resolve an issue.
- Vital Discount in Administrative Burden: By taking on the repetitive “drudge work” of safety, reminiscent of submitting experiences and sorting via low-level alerts, these programs can scale back administrative workloads by as much as 40%. This permits human groups to spend their time on high-level technique and menace searching.
- Improved Accuracy in Triage and Evaluation: Automated brokers can course of hundreds of thousands of knowledge factors with out getting drained or distracted. This results in extra correct identification of threats and ensures that no crucial alert is ignored throughout a busy interval.
- Standardized and Auditable Responses: When an agent handles a safety activity, each motion they take is documented intimately. This gives a transparent “paper path” for auditors and helps the group show it’s following all crucial safety laws and finest practices.
The combination of those programs permits safety departments to scale their efforts with out essentially hiring tons of of latest workers members.
By leveraging the velocity and consistency of agentic programs, organizations can keep a excessive stage of safety whilst the quantity of world threats continues to rise.
Making certain Compliance Via Efficient Threat and Governance Practices
Managing danger in an AI for Cybersecurity requires new guidelines and clear accountability. Governance should bridge the hole between technical capabilities and moral obligations to make sure that safety instruments are used successfully and safely:
- Adherence to Standardized Threat Frameworks: Organizations ought to align their operations with globally acknowledged requirements, such because the NIST AI Threat Administration Framework. These pointers present a structured technique to determine, measure, and handle the particular dangers related to utilizing clever programs in a company surroundings.
- Institution of Moral Use Insurance policies: Corporations should create clear guidelines for the way automated instruments are used, significantly concerning worker privateness and information utilization. This prevents “shadow AI,” the place staff use unauthorized instruments which may by accident leak delicate firm info into public databases.
- Rigorous Third-Get together and Provide Chain Audits: As companies rely extra on outdoors distributors for software program and information companies, they have to confirm that these companions keep excessive safety requirements. A vulnerability in a single provider can present a “backdoor” into dozens of different corporations, making provide chain safety a prime precedence.
- Emphasis on Human-in-the-Loop Oversight: Whereas automation gives velocity, human judgment stays important for complicated decision-making and moral concerns. Governance fashions should outline precisely when a human should intervene, particularly in high-stakes conditions like shutting down crucial enterprise programs throughout a suspected assault.
Sturdy governance ensures that, as a company adopts extra highly effective expertise, it does so with a full understanding of the potential penalties.
This creates a stability the place the advantages of automation are maximized whereas the authorized and operational dangers are saved beneath strict management.
Nevertheless, establishing these strong frameworks and sustaining a robust organizational safety posture requires specialised technical experience.
With an IBM examine revealing that 95% of cybersecurity breaches end result from human error, cultivating a extremely skilled workforce is probably the most crucial protection a company can deploy.
To fulfill the surging demand for expertise, professionals should systematically improve their talent set,s and that’s the place packages like The Publish Graduate Program in Cybersecurity, offered by the McCombs College of Enterprise at The College of Texas at Austin in collaboration with Nice Studying, are recognized to be a one-stop answer.
Designed by main college, this curriculum offers you the instruments to analyze assaults, construct strong cybersecurity programs, and achieve a aggressive edge within the job market. Right here is how this system immediately interprets to profession development:
- Grasp Governance, Threat, and Compliance (GRC): You’ll achieve a deep understanding of important requirements and frameworks to construct a robust organizational safety posture. The curriculum develops your technical experience in navigating information safety legal guidelines like GDPR and DPDP, making use of ISO 27001:2022, and managing third-party provide chain dangers.
- Perceive and Fight Trendy Cyber Assaults: You’ll be taught to view threats from an adversary’s lens, using frameworks like MITRE ATT&CK and the Cyber Kill Chain. This prepares you to acknowledge and defend towards threats reminiscent of Superior Persistent Threats (APTs) and Ransomware.
- Design and Implement Safety Controls: You’ll uncover efficient strategies for making use of safety methods, diving deeply into Endpoint Detection and Response (EDR), Identification and Entry Administration (IDAM), Knowledge Loss Prevention (DLP), and steady monitoring utilizing SIEM.
- Acquire Sensible, Arms-On Expertise: This system goes past concept by providing in depth lab classes. You’ll follow capturing community visitors with Wireshark, configuring Subsequent Technology Firewalls (NGFW), executing net software penetration assessments, and securing information on Microsoft Azure.
By constructing experience throughout GRC, menace intelligence, safety structure, and hands-on protection practices, this program equips you to scale back organizational danger, strengthen resilience, and place your self as a trusted cybersecurity chief in an more and more high-stakes digital dangers.
Conclusion
Adapting cybersecurity pondering for the age of AI requires a transfer away from the “defend and react” mindset of the previous. It’s not sufficient to attend for an assault to occur after which attempt to repair it; as a substitute, safety should be an energetic, clever, and foundational a part of each enterprise course of.
This transformation entails deploying autonomous defenses that may match the velocity of attackers, restructuring networks to take away unearned belief, and constructing a workforce that’s deeply expert within the nuances of recent expertise.
By specializing in resilience, governance, and steady adaptation, organizations can navigate this new period with confidence, guaranteeing they keep forward of the curve in a quickly altering menace surroundings.

