With an id supplier (IdP), you’ll be able to handle your consumer identities exterior of AWS and provides these exterior consumer identities permissions to make use of AWS assets in your AWS accounts. Exterior IdPs, resembling Ping Identification, can combine with AWS IAM Identification Middle to be the supply of fact for Amazon SageMaker Unified Studio. SageMaker Unified Studio additionally helps trusted id propagation for SQL analytics, together with Amazon Athena and Amazon Redshift.
SageMaker Unified Studio offers an built-in expertise to make use of your information and instruments for analytics and AI. You need to use SageMaker Unified Studio to find your information and put it to work utilizing acquainted AWS analytics and machine studying (ML) providers for mannequin improvement, generative AI, large information processing, and SQL analytics, assisted by Amazon Q Developer. By default, SageMaker domains help AWS Identification and Entry Administration (IAM) consumer credentials. You can too allow entry to SageMaker domains in SageMaker Unified Studio for customers with single sign-on (SSO) with IAM Identification Middle and direct SAML integration with SageMaker Unified Studio.
Customers can entry SageMaker Unified Studio with their current company credentials. With IAM Identification Middle, directors can join their current exterior IdPs and proceed to handle customers and teams in these current id methods, which might then be synchronized with IAM Identification Middle utilizing System for Cross-domain Identification Administration (SCIM).On this put up, we present how one can arrange workforce entry with SageMaker Unified Studio utilizing Ping Identification as an exterior IdP with IAM Identification Middle.
On this put up, we present how one can arrange workforce entry with SageMaker Unified Studio utilizing Ping Identification as an exterior IdP with IAM Identification Middle.
Resolution overview
We stroll by means of the next high-level steps to implement this answer:
- Allow IAM Identification Middle.
- Create a SageMaker Unified Studio area.
- Arrange your IdP (for this instance, Ping Identification).
- Join Ping Identification and IAM Identification Middle.
- Arrange computerized provisioning of customers and teams in IAM Identification Middle.
- Configure SageMaker Unified Studio SSO consumer entry.
Stipulations
For this walkthrough, you need to have the next conditions:
- An AWS account with IAM Identification Middle enabled. It’s endorsed to make use of an organization-level IAM Identification Middle occasion for finest practices and centralized id administration throughout your AWS group.
- A Ping Identification account.
- A browser with community connectivity to Ping Identification and SageMaker Unified Studio.
Allow IAM Identification Middle
To allow IAM Identification Middle, observe the directions in Allow IAM Identification Middle.
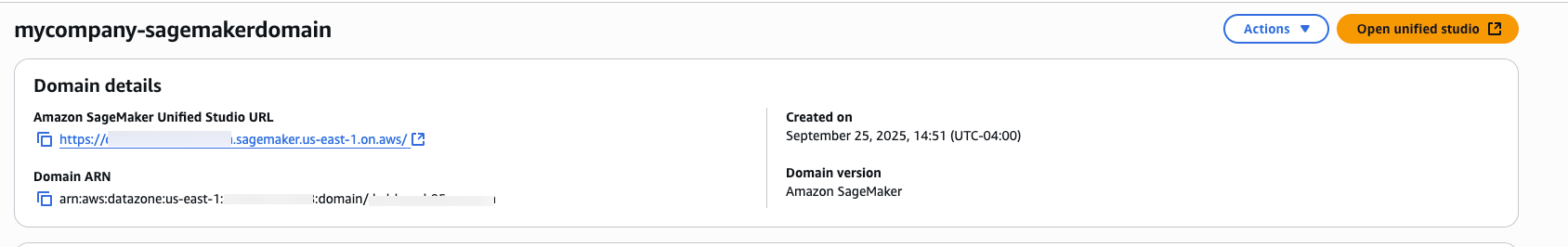
Create a SageMaker Unified Studio area
To create a SageMaker Unified Studio area, check with the directions in Create a Amazon SageMaker Unified Studio area – guide setup.
On the SageMaker console, go to the area particulars and duplicate the Amazon Useful resource Title (ARN) beneath Area ARN. You’ll use this worth if you add your belief coverage and if you join your IAM IdP to your Ping Identification occasion.
Arrange your IdP (Ping Identification)
On this part, we stroll by means of the process to arrange your IdP (for this instance, Ping Identification).
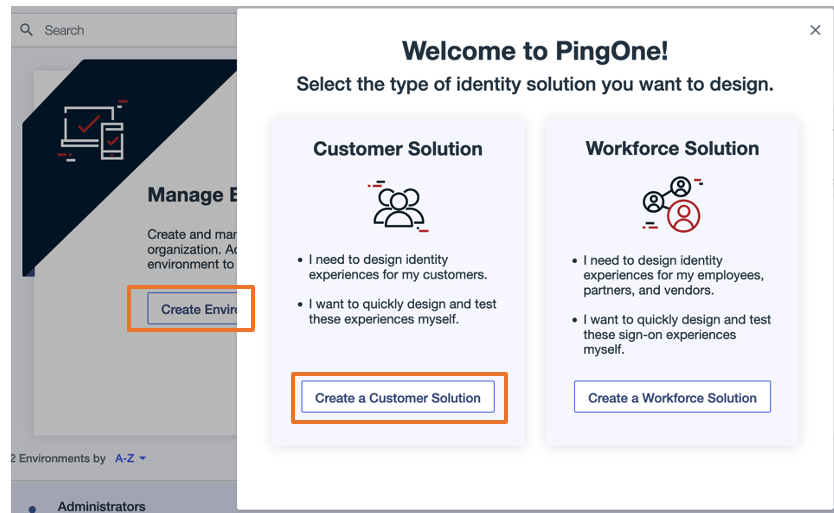
Create an surroundings in Ping Identification
Full the next steps to create an surroundings for Ping Identification:
- Log in to your Ping Identification account.
- Select Create Surroundings.
- Select Create a Buyer Resolution.
- Within the Tailor your experiences pop-up, select Skip.
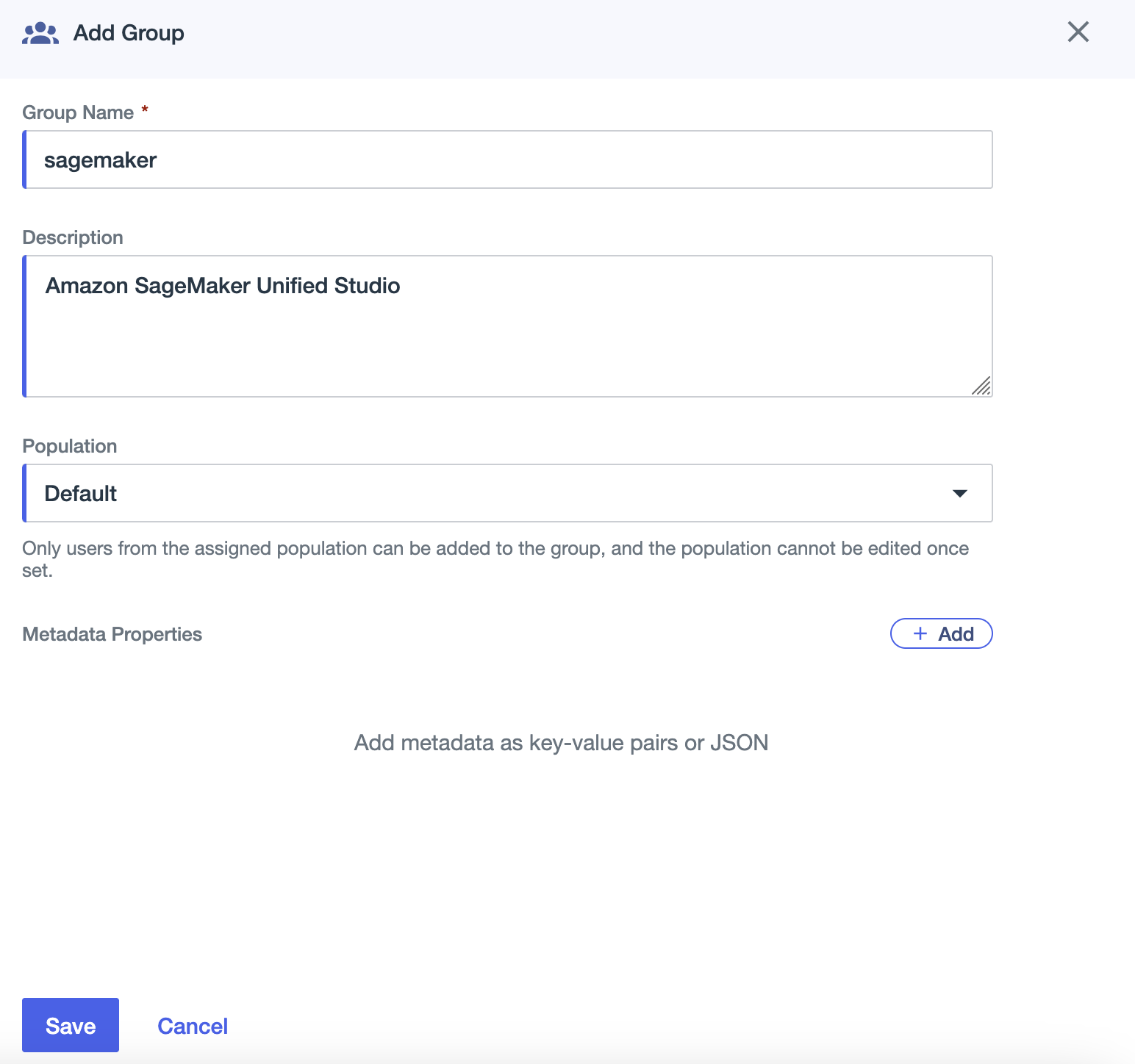
Create a gaggle in Ping Identification
Full the next steps to create a group in Ping Identification:
- On the Environments web page, select Handle Environments.
- Within the navigation pane, select Listing, then select Teams.
- Select the plus signal so as to add a gaggle.
- For Group Title, enter
sagemaker - For Description, enter an elective description (for instance,
Amazon SageMaker Unified Studio). - For Inhabitants, select Default.
- Select Save.
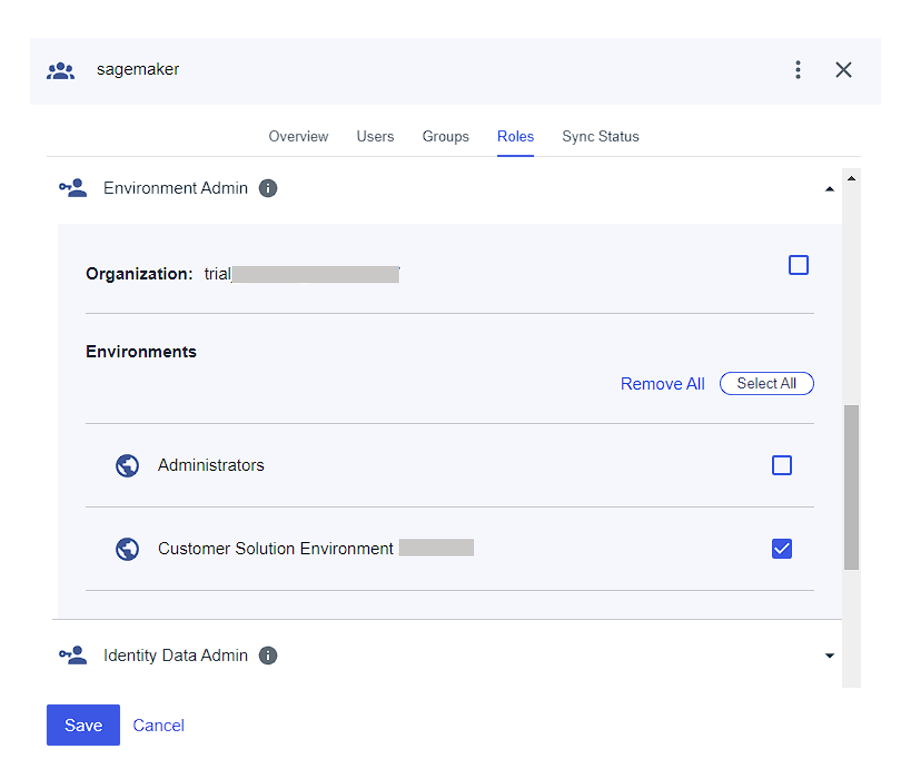
- On the Roles tab for the
sagemakergroup, assign the Surroundings Admin position to the group.
Create a consumer in Ping Identification
Full the next steps to create a consumer:
- Within the navigation pane, select Listing, then select Customers.
- Select the plus signal to create a consumer.
- Present values for Given title, Household title, Username, and Electronic mail.
- For Password, select First time password.
- Select Save.
You’ll be able to add extra customers as wanted.
Assign group to consumer
Full the next steps to assign your group to your consumer:
- Within the navigation pane, select Listing, then select Teams.
- Select the
sagemakergroup you created. - On the Customers tab, select the plus signal so as to add a consumer.
- Add the consumer you created.
Join Ping Identification and IAM Identification Middle
To configure the combination between Ping Identification and IAM Identification Middle, you want entry to each administration consoles. Though Ping Identification’s software catalog contains IAM Identification Middle, we advocate configuring a normal SAML software for higher management over settings and attribute mappings.
Full the next steps:
- Go to the Ping Identification surroundings you created and select Functions within the navigation pane.
- Select the plus signal so as to add an software:
- For Utility title, enter a reputation (for this instance, we use
unifiedstudio). - For Description, enter an elective description.
- For Utility Sort, select SAML Utility.
- Select Configure.
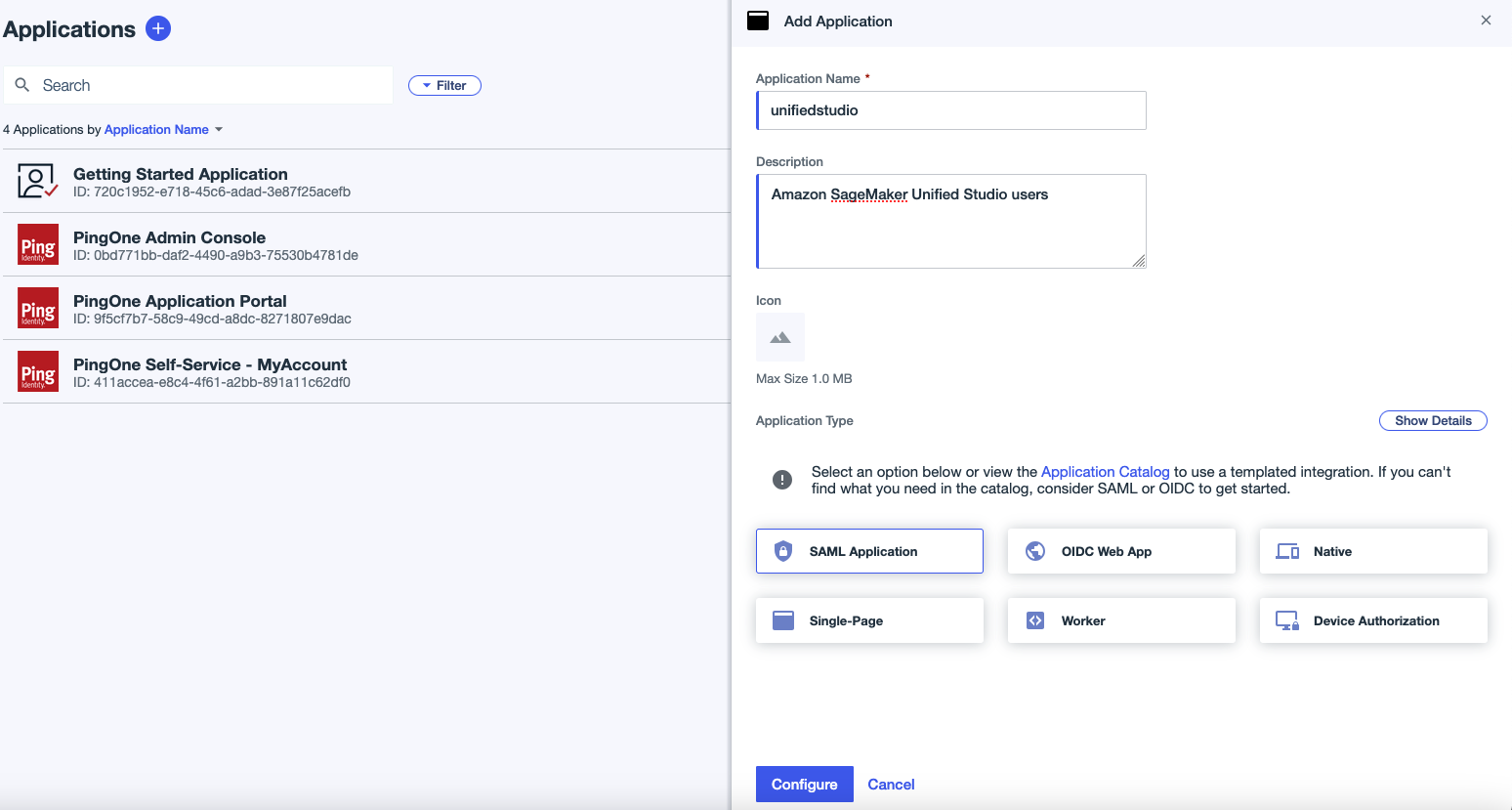
- For Utility title, enter a reputation (for this instance, we use
- Register to the IAM Identification Middle console as a consumer with administrative privileges.
- Within the navigation pane, select Settings to replace your settings:
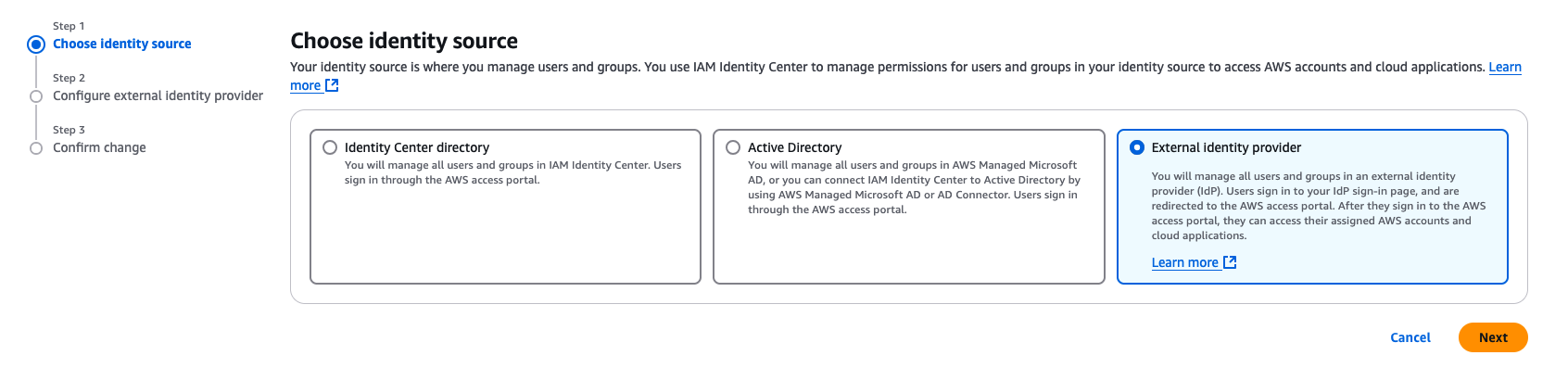
- On the Identification supply tab, select Change id supply on the Actions dropdown menu.
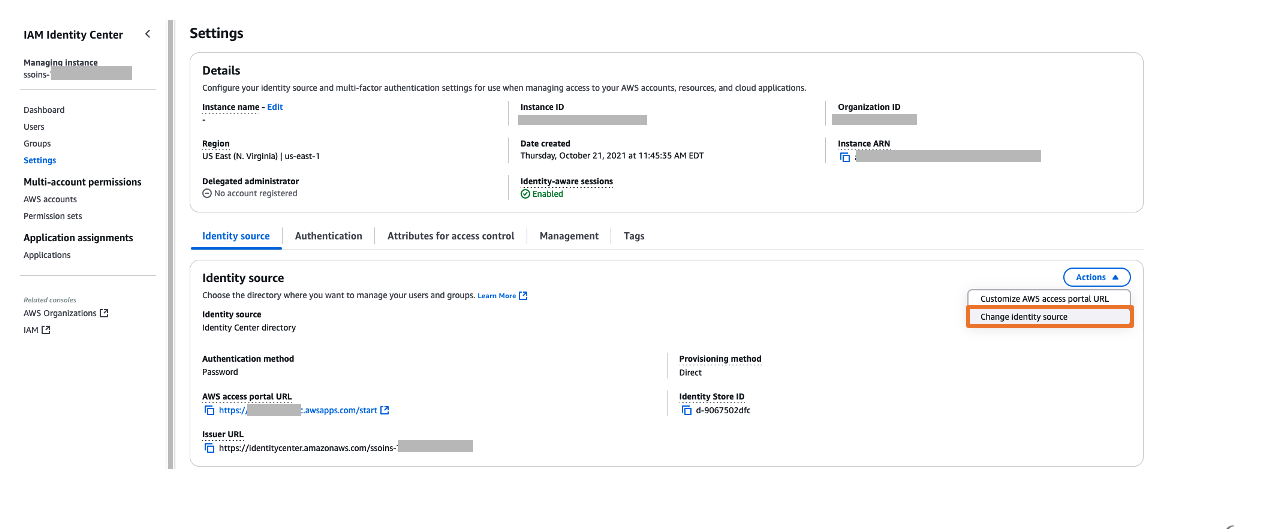
- For Select id supply, choose Exterior id supplier, then select Subsequent.
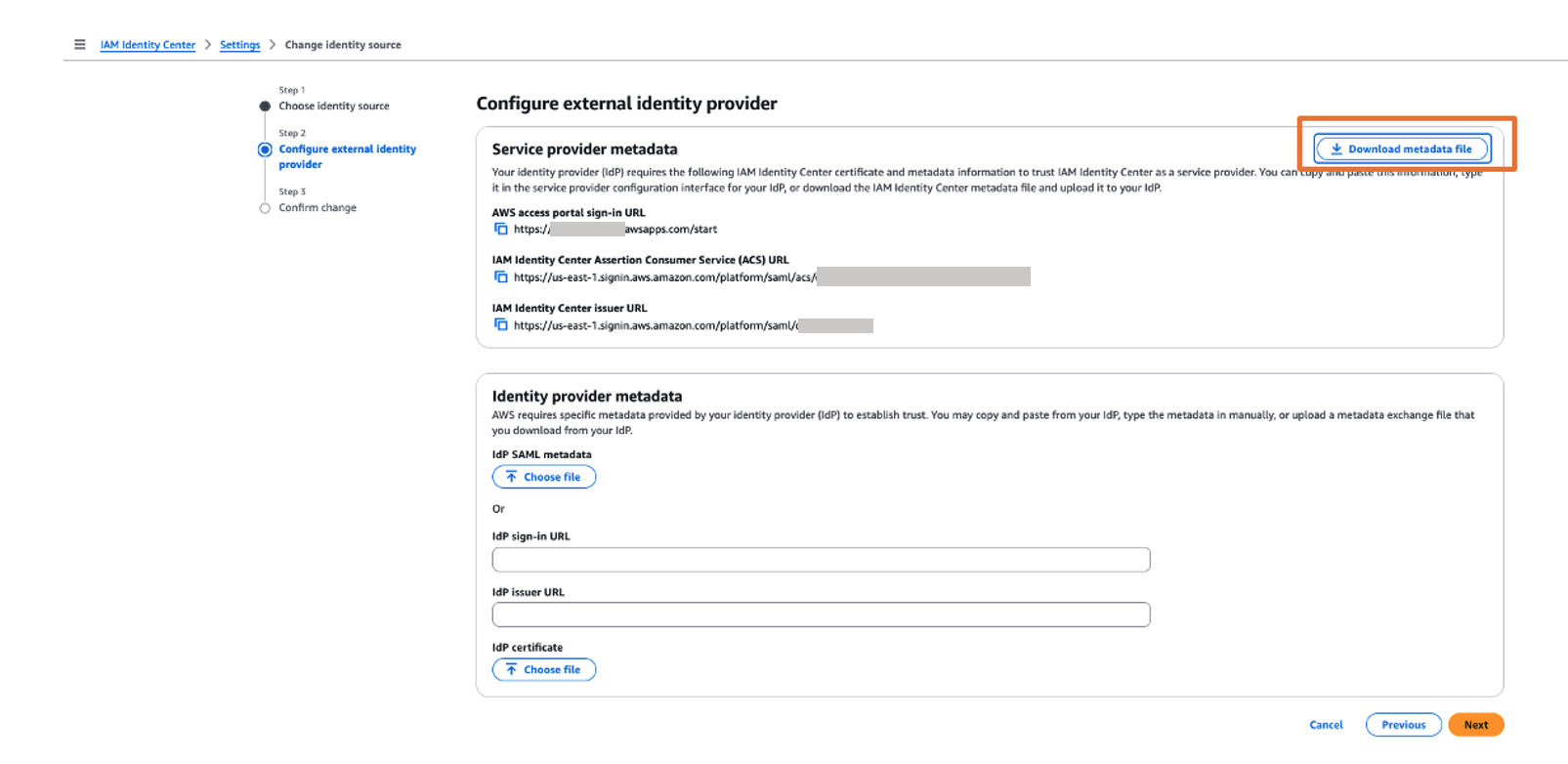
- Within the Service supplier metadata part, select Obtain metadata file to obtain the IAM Identification Middle metadata file.
You’ll use this service supplier metadata file within the subsequent step if you join Ping Identification with IAM Identification Middle.
- On the Identification supply tab, select Change id supply on the Actions dropdown menu.
- Return to the Ping Identification console and the SAML software web page.
- Within the SAML Configuration part, choose Import Metadata, add the metadata file you downloaded, then select Save.
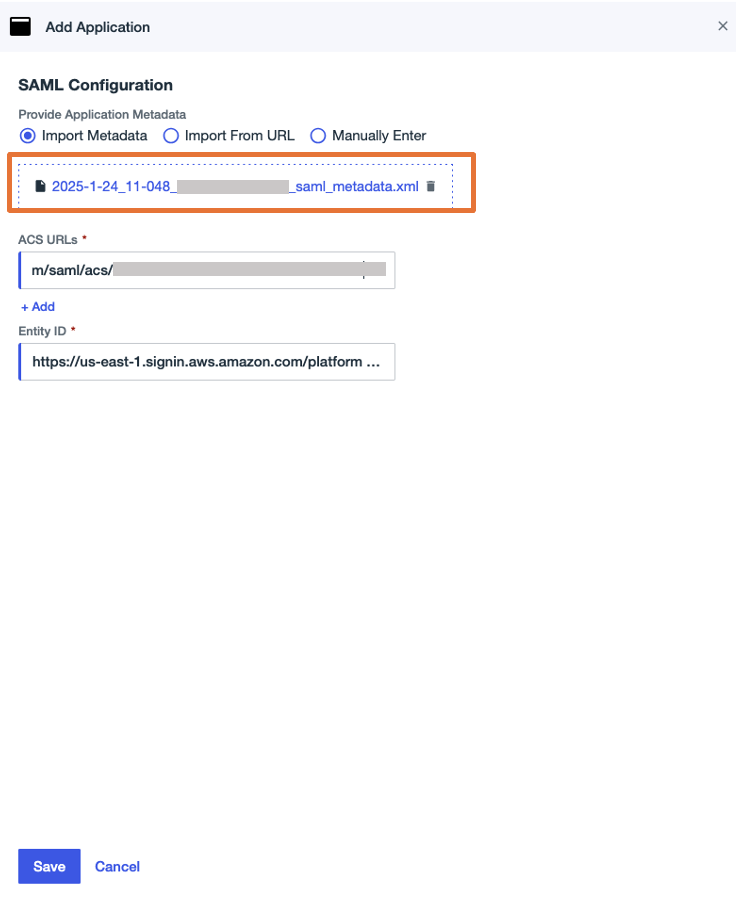
- On the Overview tab of the applying web page, select Obtain Metadata beneath Connection particulars to obtain the Ping Identification IdP metadata.
You’ll use this for the SAML configuration in IAM Identification Middle to arrange Ping Identification as an IdP within the subsequent step.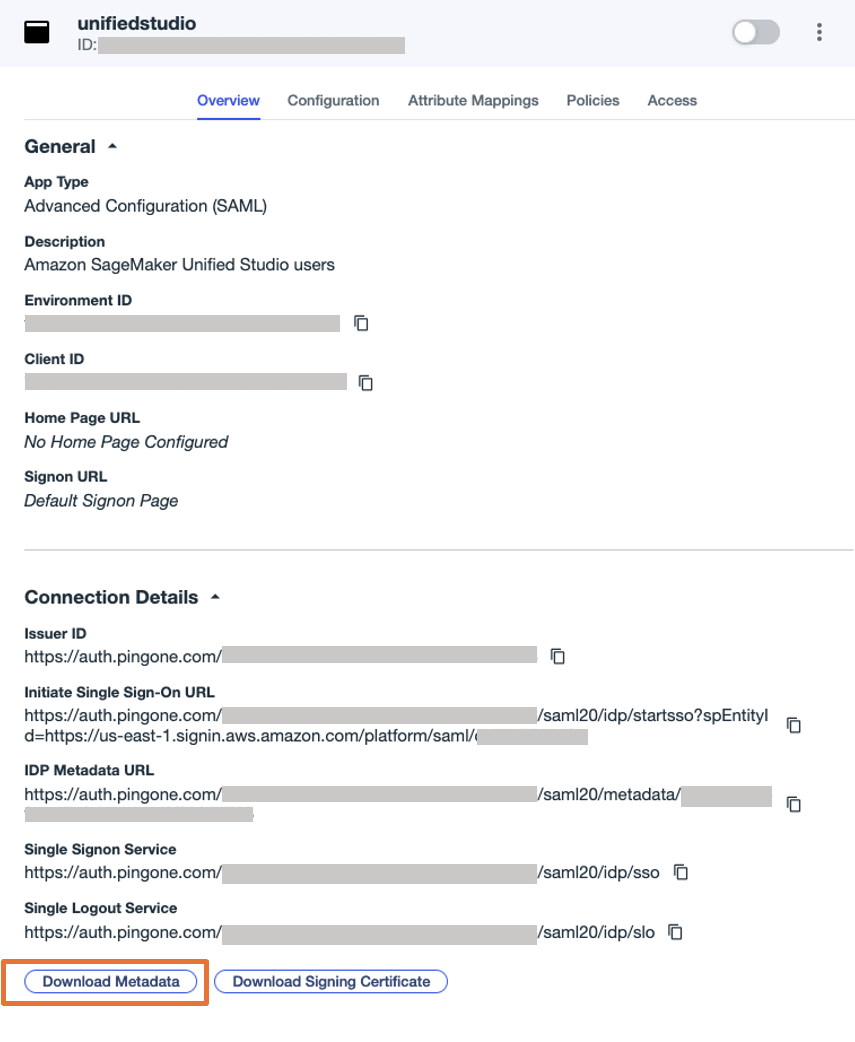
- Return to the IAM Identification Middle console and proceed configuring your id supply:
- Within the Identification supplier metadata part, select Select file beneath IdP SAML metadata, add the metadata file you downloaded from Ping Identification, then select Subsequent.
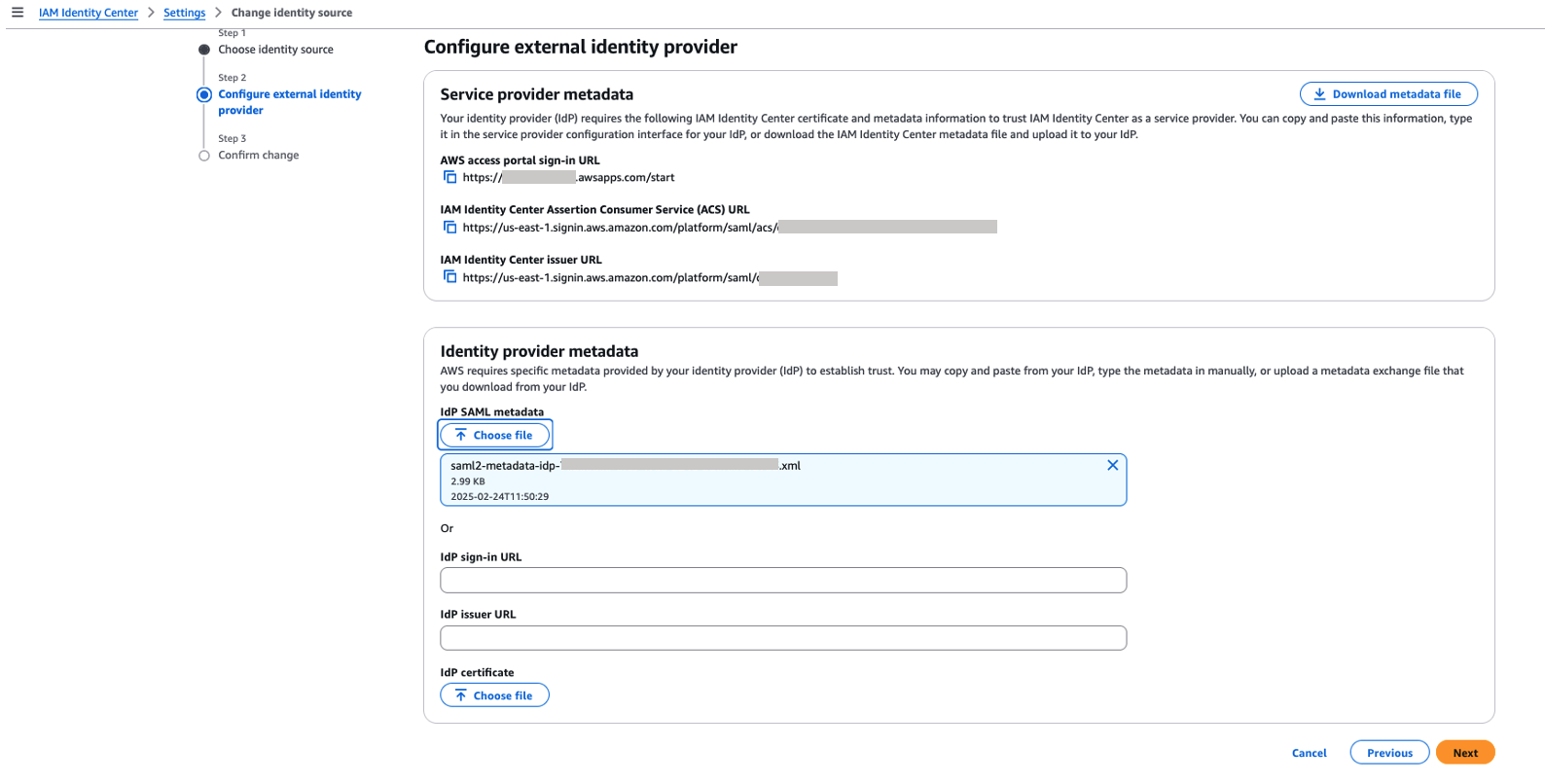
- Select Settle for to just accept the disclaimer.
- Select Change id supply.
- Within the Identification supplier metadata part, select Select file beneath IdP SAML metadata, add the metadata file you downloaded from Ping Identification, then select Subsequent.
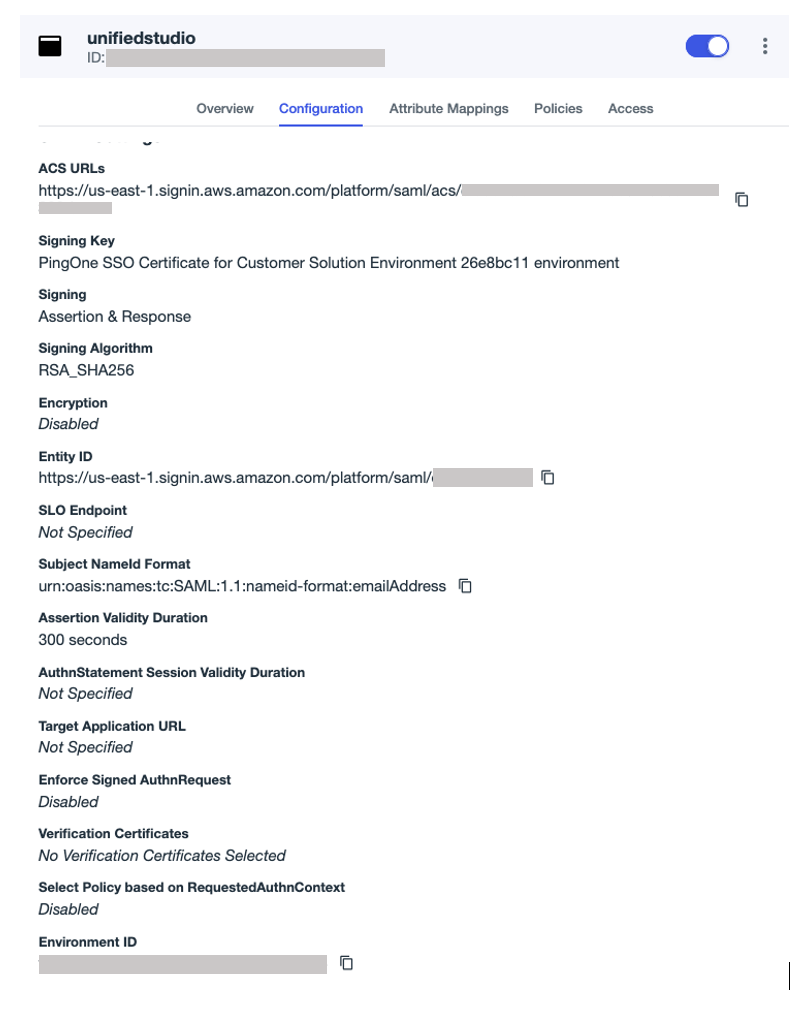
- Return to the Ping Identification console to finish the SAML configuration.
- On the Configuration tab, select the edit icon to replace the configuration:
- For Signal, select Signal Assertion & Response.
- For Topic Title ID, enter
urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress. - For Assertion Validity Period, enter
300. - Go away the remaining values as default.
- On the Attributes tab, select the edit icon.
- Select +Add so as to add two attribute mappings:
- Map the attribute
saml-subjecttoUsername, and depart Title format as default. - Map the attribute
https://aws.amazon.com/SAML/Attributes/PrincipalTag:Electronic mailtoElectronic mail Deal with,and set Title format to Unspecified. - Select Save.
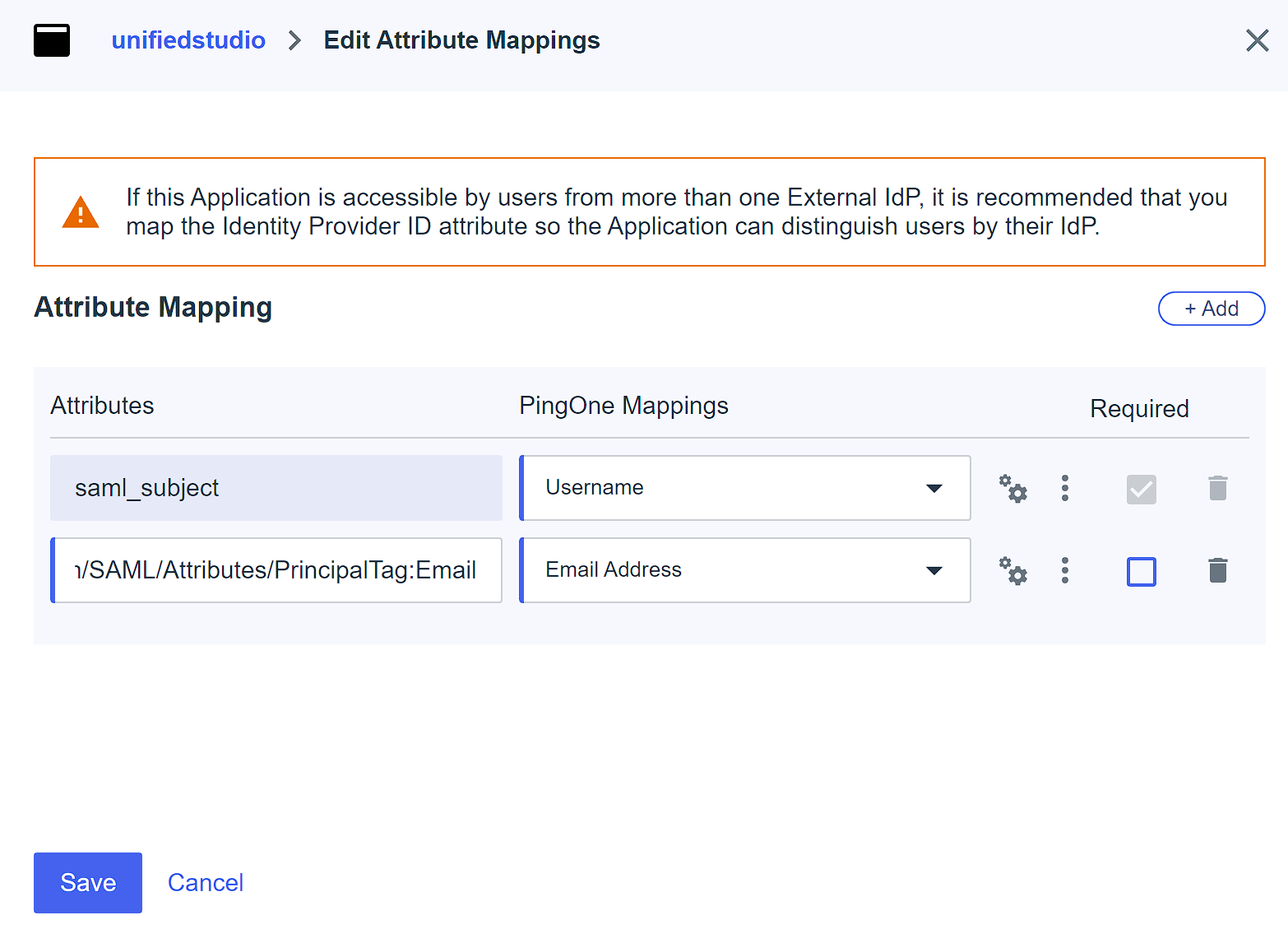
- Map the attribute
- On the PingOne Insurance policies tab, choose Single Issue, then select Save.
This put up makes use of single-factor authentication for demonstration functions solely. In your environments, observe your group’s safety requirements and governance framework.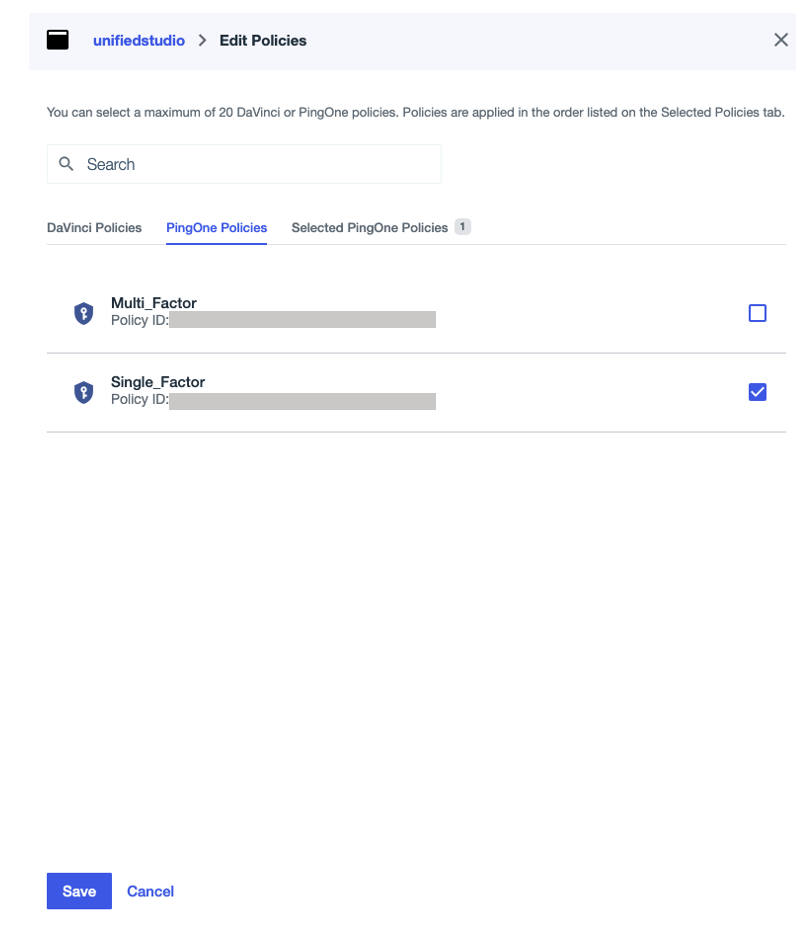
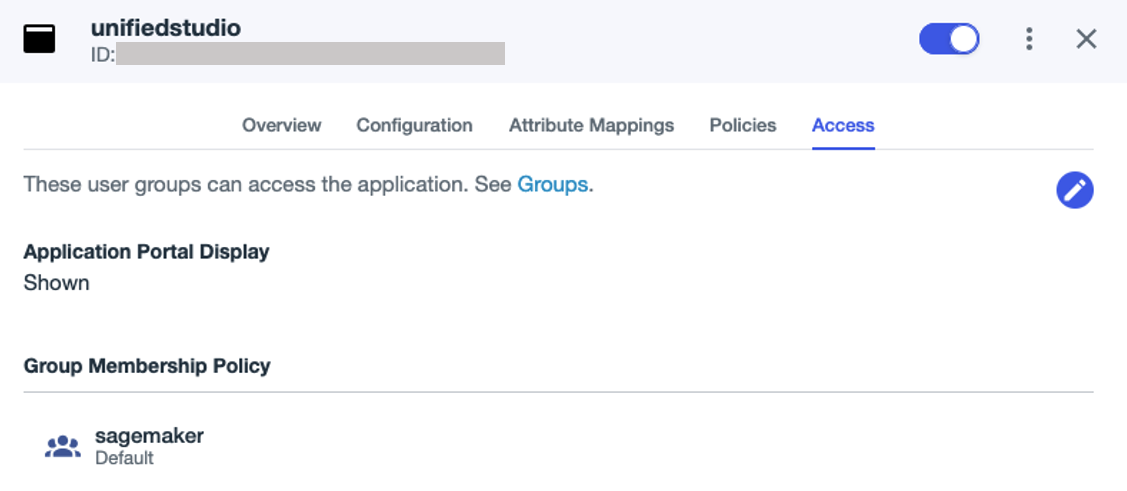
- On the Entry tab, seek for the
sagemakergroup beneath Group Membership Coverage, and assign theunifiedstudioSAML software to the group. - Allow the applying.
Arrange computerized provisioning of customers and teams from Ping Identification into IAM Identification Middle
To configure the automated provisioning of customers and teams between Ping Identification and IAM Identification Middle by means of SCIM, you will need to have entry to each administration consoles. Full the next steps:
- On the IAM Identification Middle console, select Settings within the navigation pane.
- Within the Computerized provisioning part, select Allow.
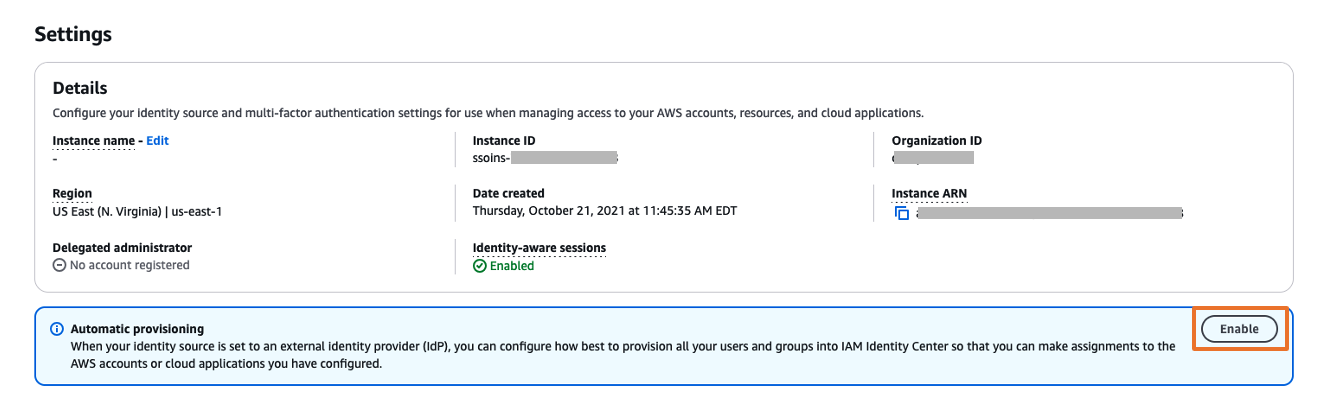
This allows computerized provisioning in IAM Identification Middle and shows the required SCIM endpoint and entry token data.
- Within the Inbound computerized provisioning dialog field, copy the values for SCIM endpoint and Entry token, then select Shut.
You’ll use these values to configure provisioning in Ping Identification within the subsequent step.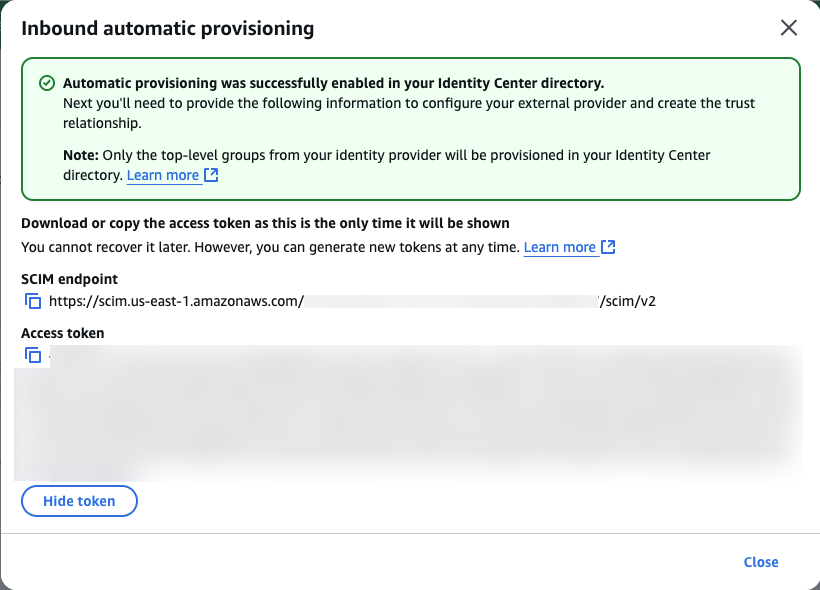
This completes the setup course of in IAM Identification Middle.
- Log in to the Ping Identification console.
- Within the navigation pane, select Integrations, then select Provisioning.
- Select the plus signal so as to add a brand new connection.
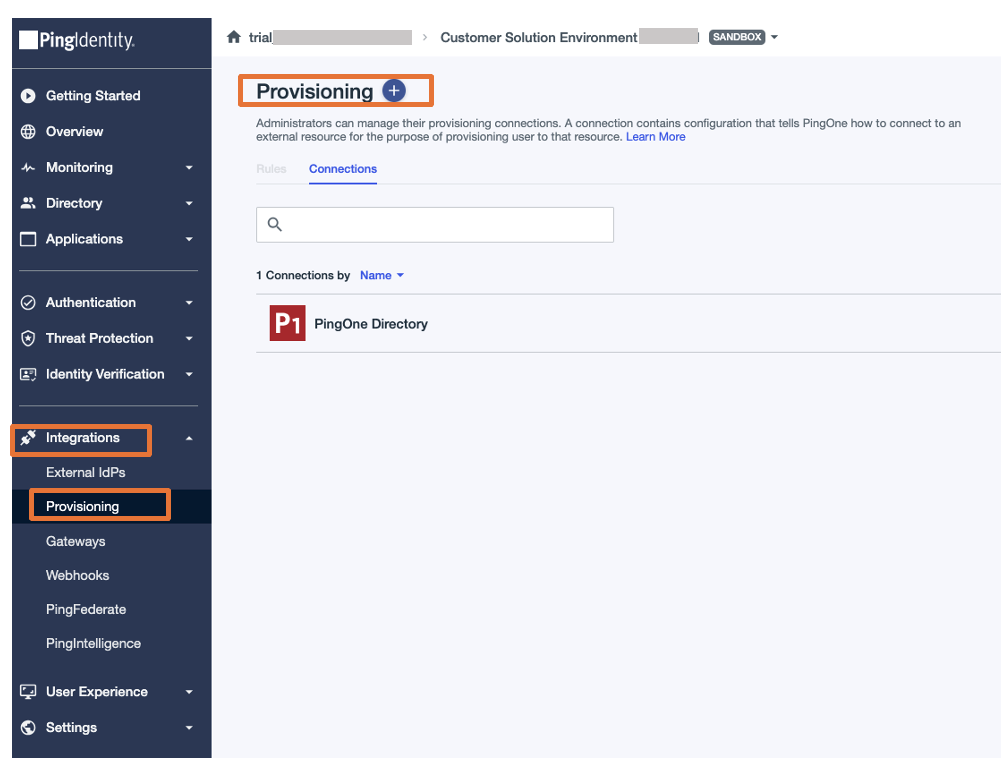
- For Select a connection sort, select Choose subsequent to Identification Retailer.
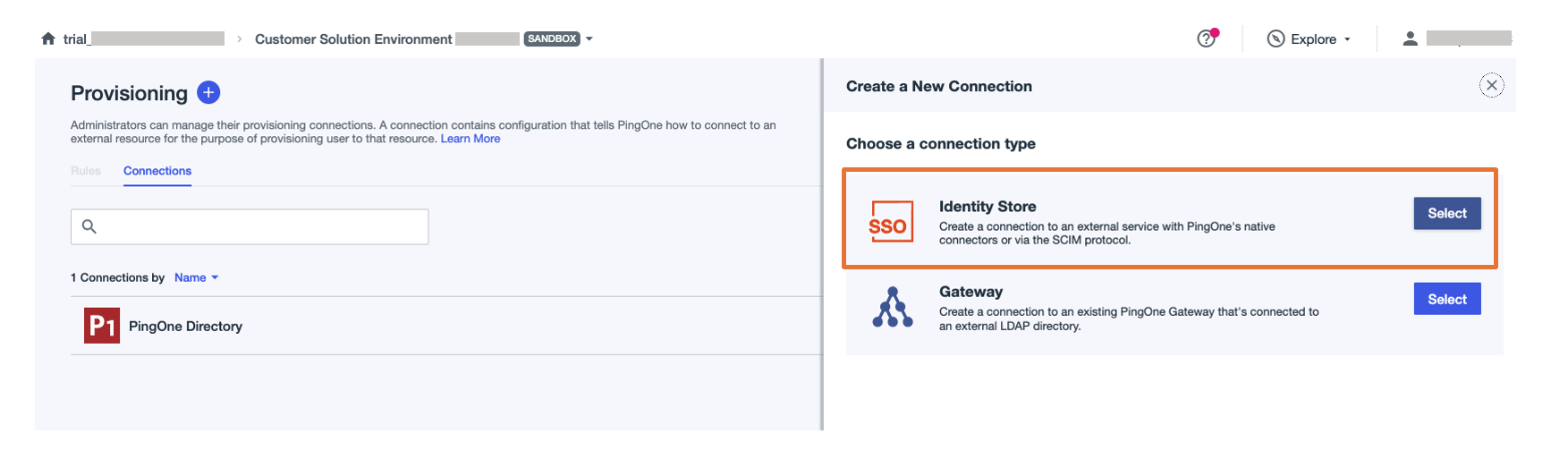
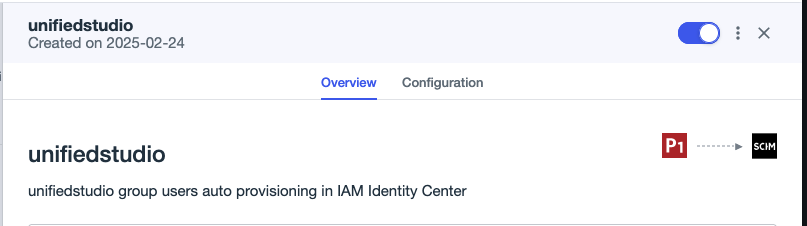
- Present a reputation (for this instance, we use
Identitycenter) and an elective description, then select Subsequent.
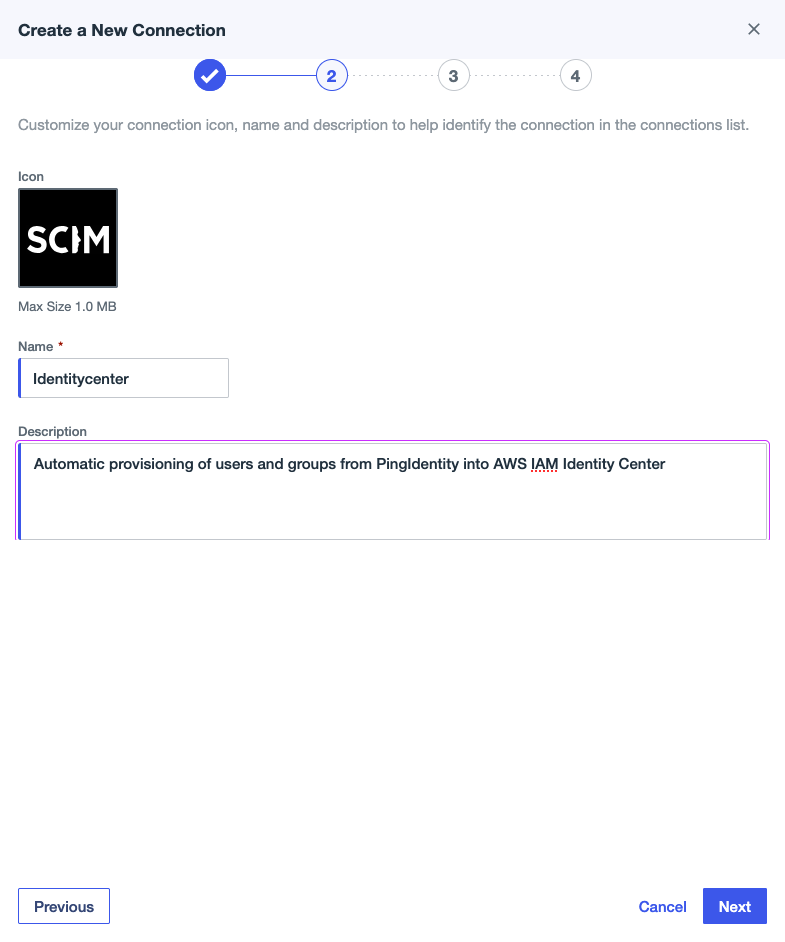
- Below Configuration Authentication, present the next configuration:
- For SCIM BASE URL, enter the SCIM endpoint from IAM Identification Middle.
- For Authentication Methodology, select OAuth 2 Bearer Token.
- For Oauth Entry Token, enter the entry token from IAM Identification Middle.
- For Auth Sort Header, select Bearer (default possibility).
- Select Check Connection to validate the connection between Ping Identification and IAM Identification Middle, then select Subsequent.
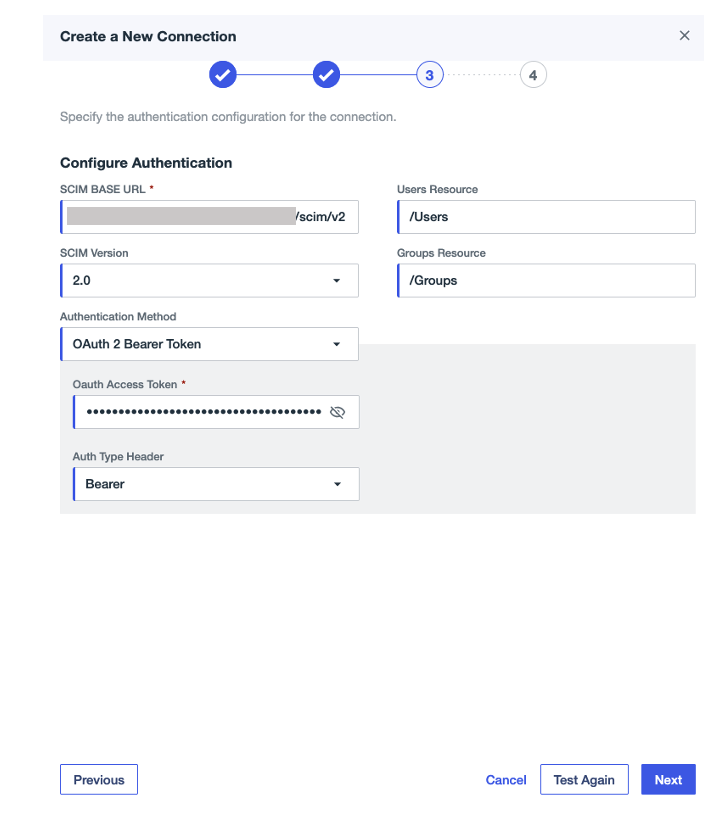
- Below Configuration Desire, present the next configuration:
- For Person Filter Expression, enter
userName Eq “%s”. - For Group Membership Dealing with, choose Merge.
- Go away the remaining settings as default and select Save.
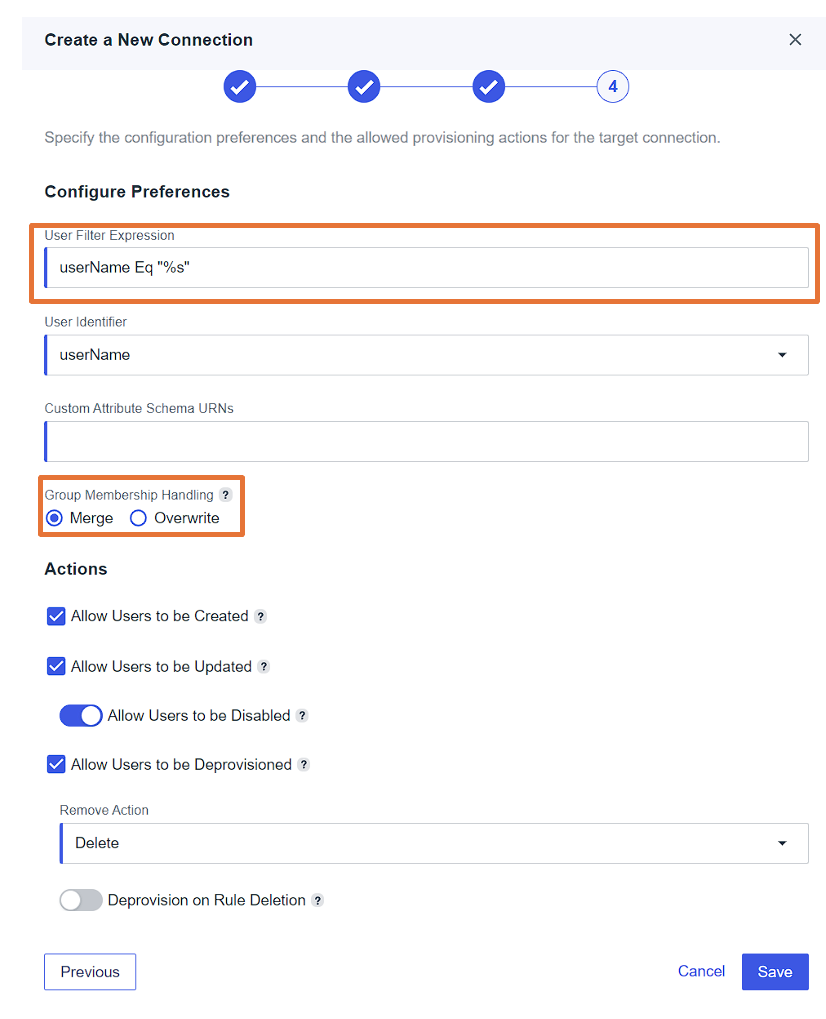
- For Person Filter Expression, enter
- On the Provisioning tab, select the plus signal, then select New Rule to create a rule for the SCIM connection.
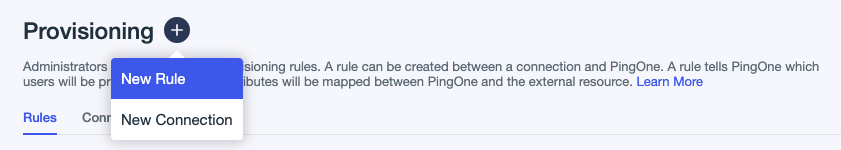
- Enter a reputation (for this instance,
unifiedstudio) and an elective description, then select Create Rule. - Below the newly created rule, select the plus signal subsequent to Accessible Connections so as to add the connection
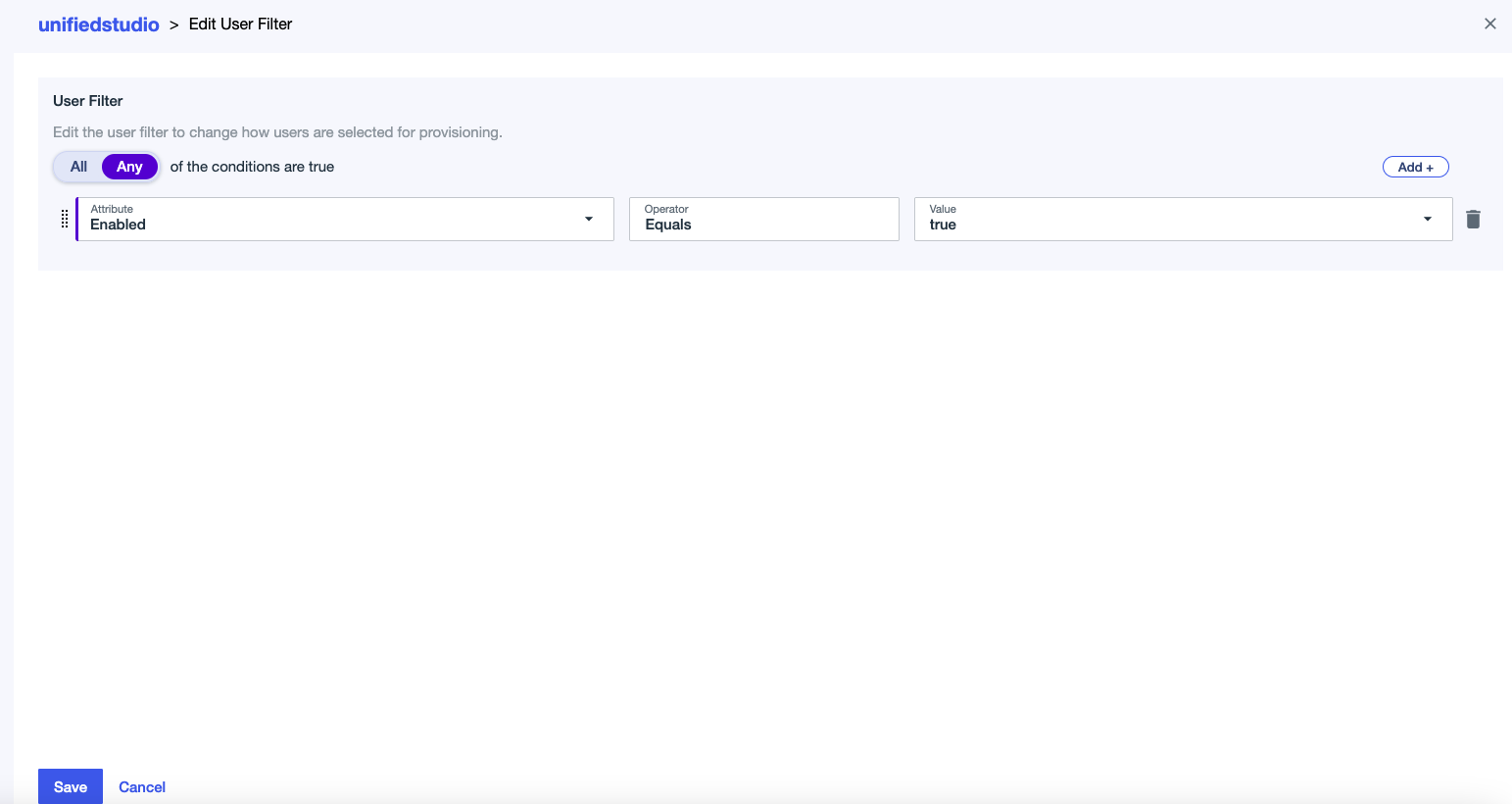
identitycenter, then select Save. - Edit the consumer filter:
- For Attribute, select Enabled.
- For Operator, select Equals.
- For Worth, select true.
- Select Save.
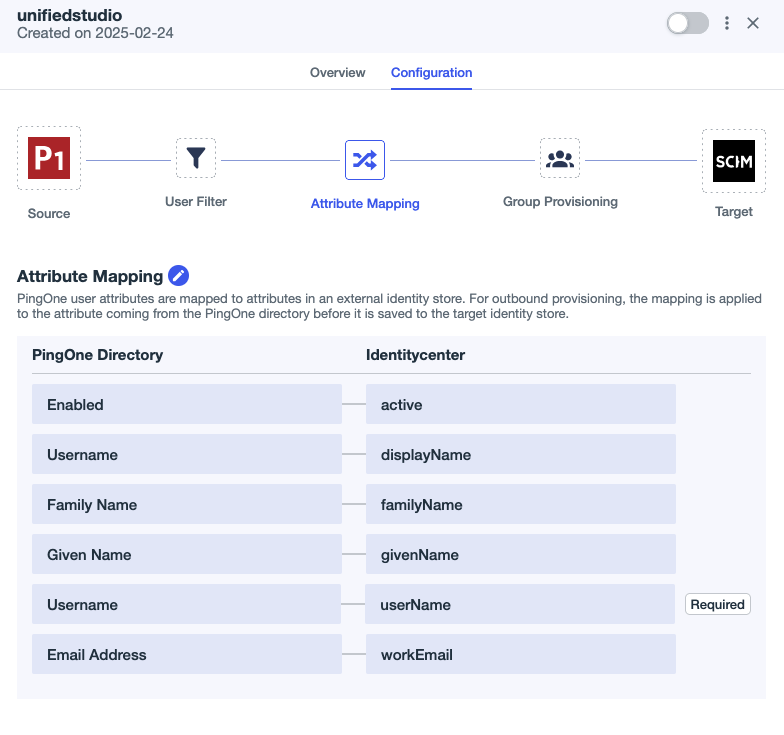
- Select the edit icon subsequent to Attribute Mapping and set the attribute mappings as proven within the following screenshot:
- Delete the Major Telephone attribute mapping as a result of it’s elective in AWS. Leaving this discipline clean may cause Ping Identification’s SCIM connector to generate errors throughout consumer provisioning.
- Add a brand new attribute referred to as
Usernamebeneath PingOne Listing after which map todisplayNamebeneath Identitycenter.
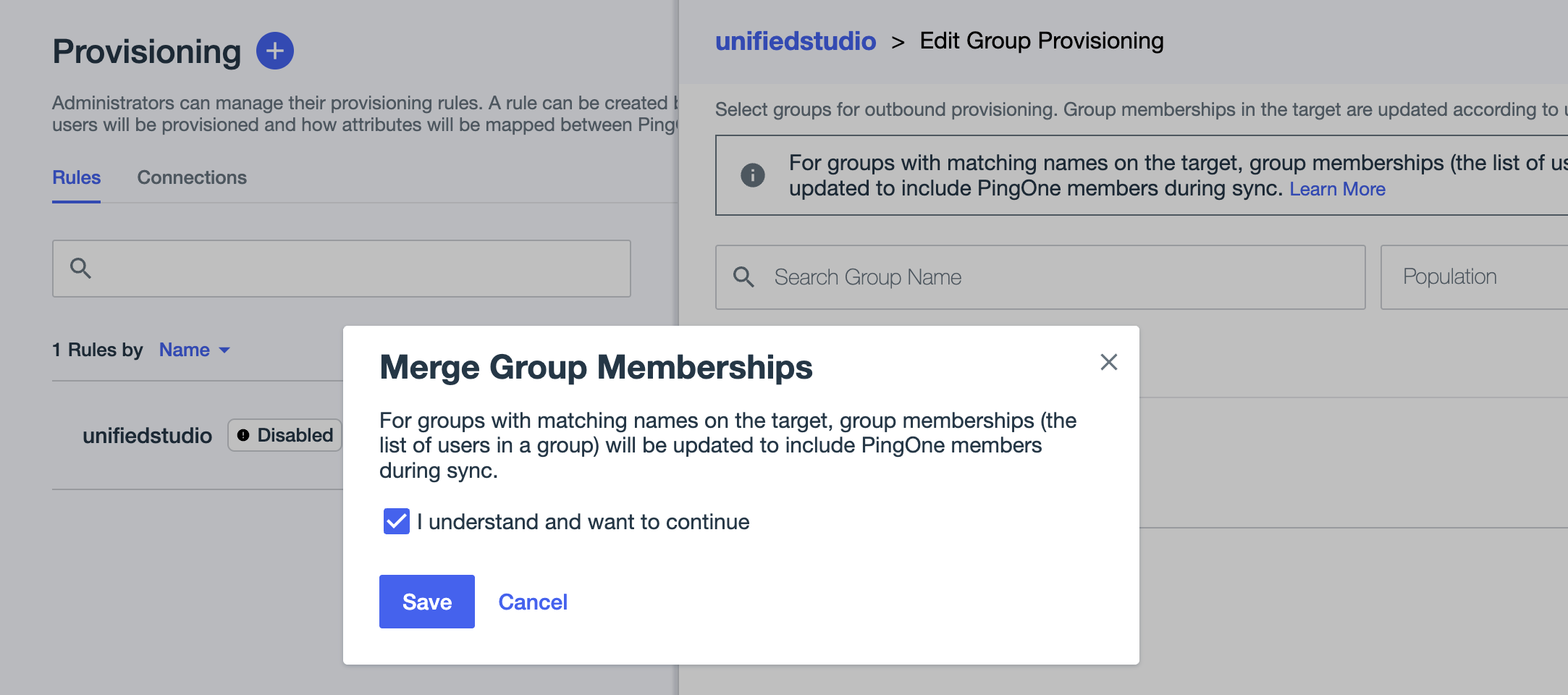
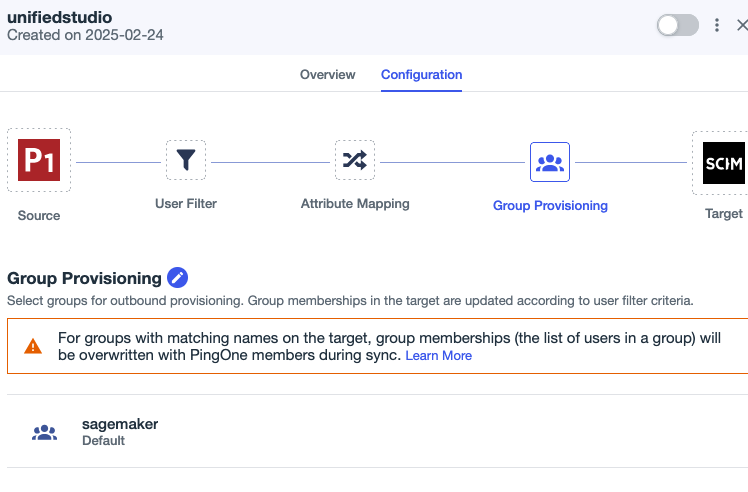
- Below Group Provisioning, select the
sagemakergroup if you wish to sync allsagemakergroup customers with auto provisioning.- Within the pop-up, choose I perceive and wish to proceed, then select Save.
- On the Provisioning web page, select the Connections tab.
- Allow the SCIM connection
Identitycenterand ruleunifiedstudio.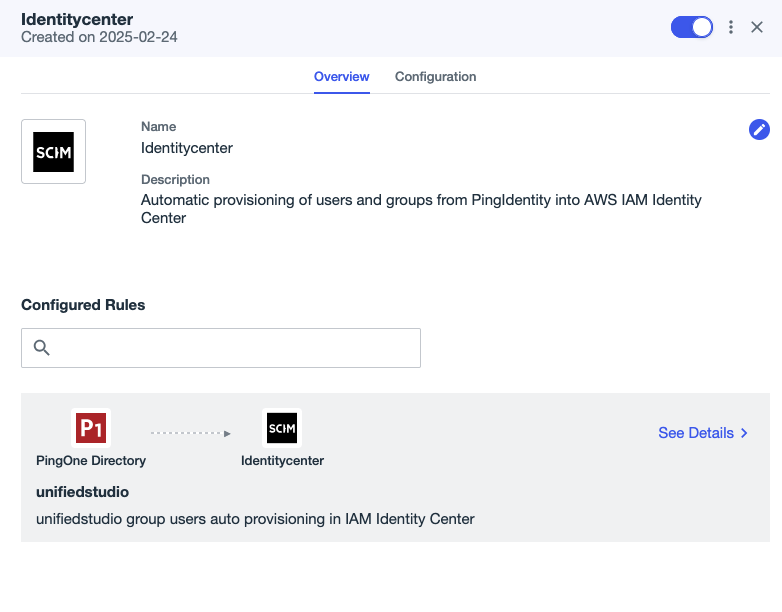
This completes the SCIM setup course of between Ping Identification and IAM Identification Middle.
Configure SageMaker Unified Studio SSO consumer entry
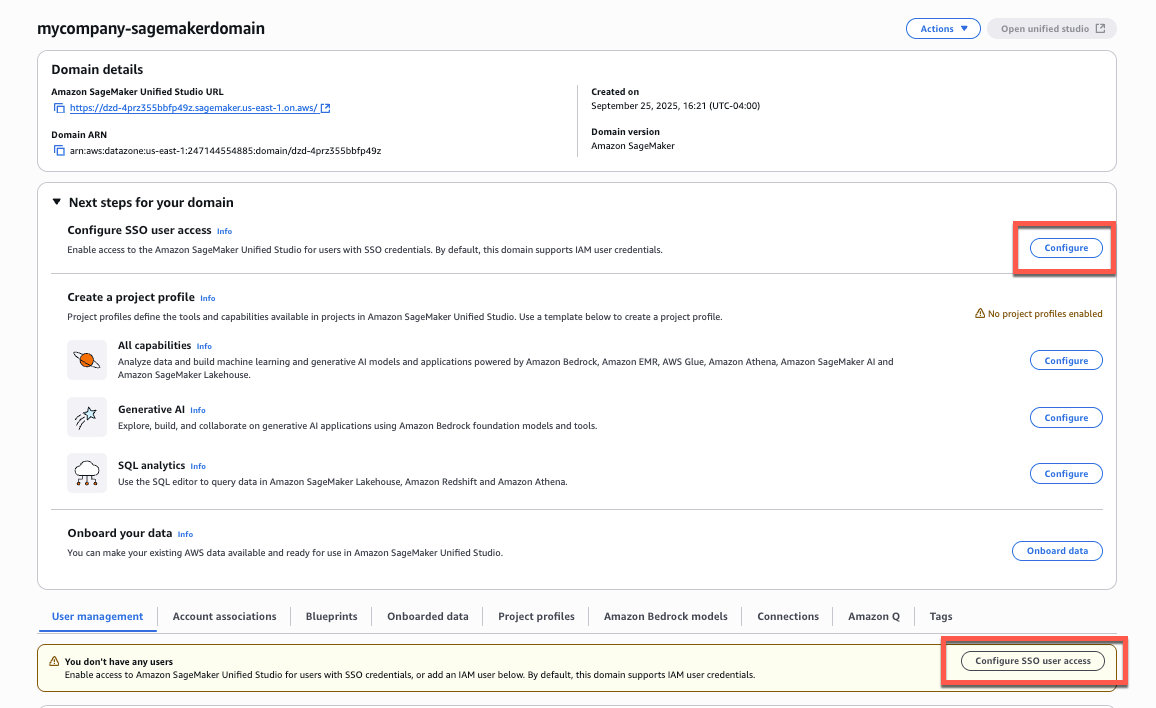
Full the next steps to configure SSO consumer entry to SageMaker Unified Studio in your SageMaker area:
- On the SageMaker console, select Domains within the navigation pane.
- Select the area for which you wish to configure SAML consumer entry.
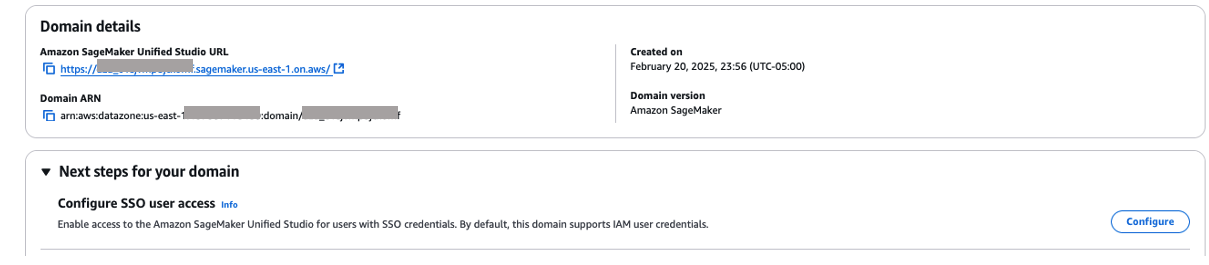
- On the area particulars web page, you will discover the SSO configuration in two places:
- From the primary area view, select Configure subsequent to Configure SSO consumer entry.
- Alternatively, scroll all the way down to the Person administration tab and select Configure SSO consumer entry.
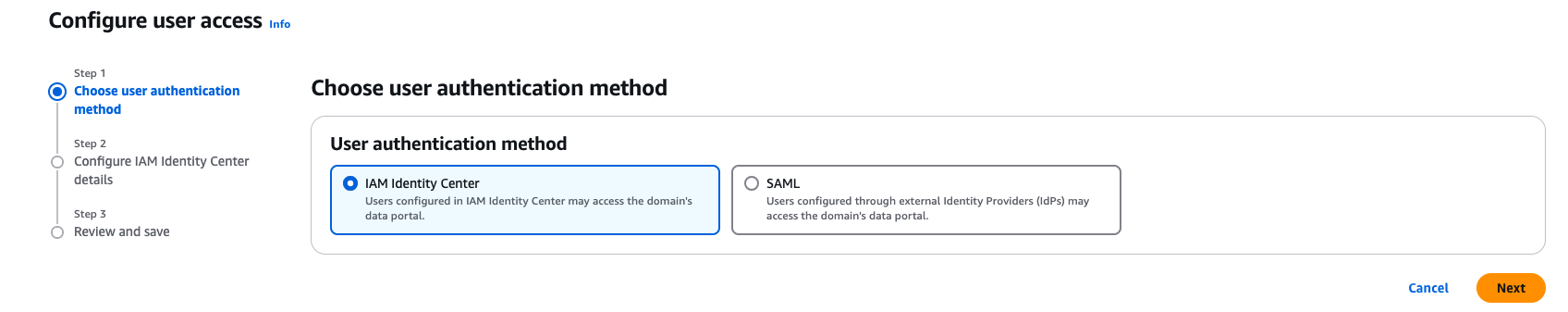
- On the Select consumer authentication technique web page, choose IAM Identification Middle, then select Subsequent.
- For Select consumer and group project technique, select from the next choices, then select Subsequent:
- Require assignments: Customers and teams should be explicitly added to the area to achieve entry. This offers extra granular management over who can entry the area.
- Don’t require assignments: All approved Ping Identification customers and teams can entry this area if they’ve been assigned to the SAML software in Ping Identification.
For both possibility, customers or teams should have entry to the Ping Identification SAML software (
unifiedstudioon this instance) to authenticate efficiently.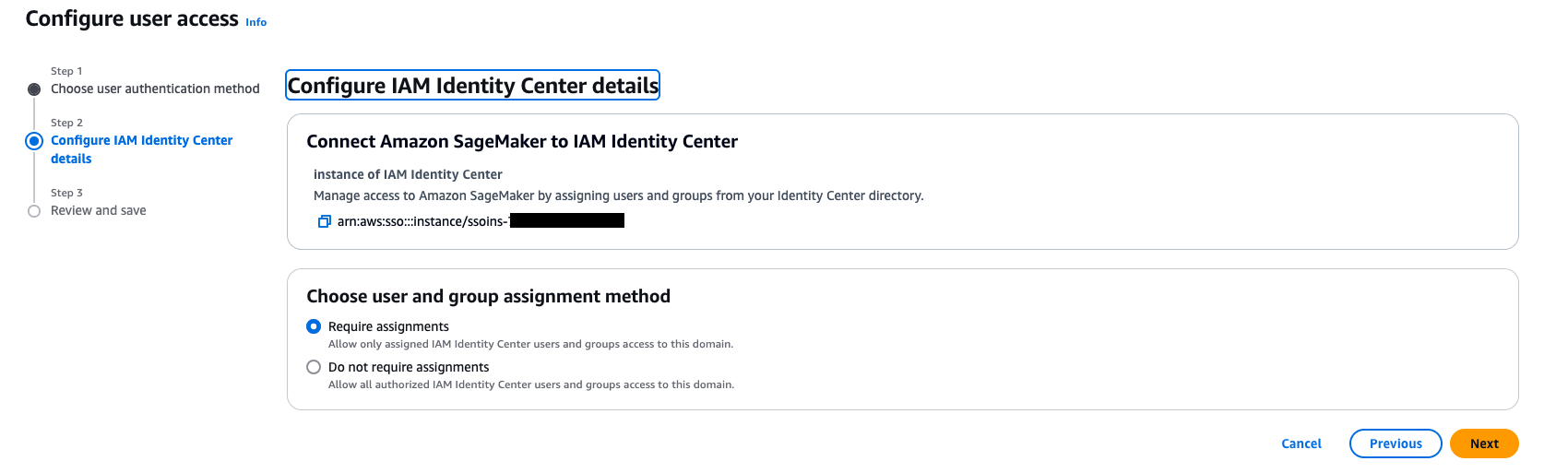
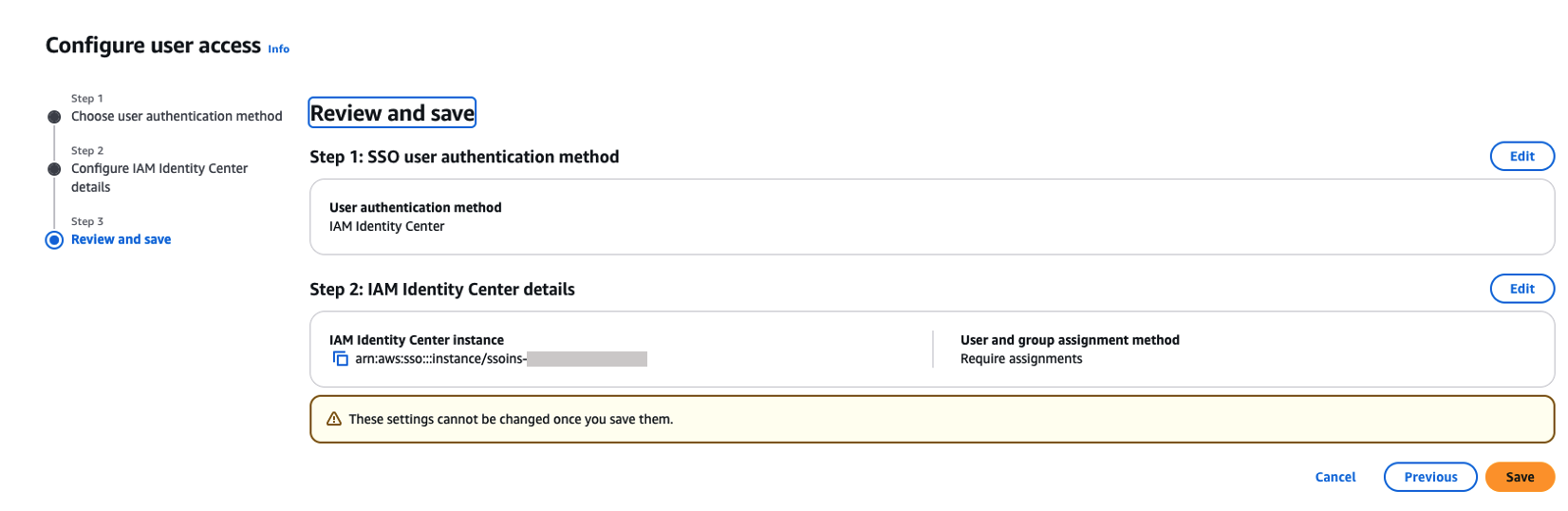
- On the Evaluate and save web page, overview your decisions and select Save. These settings can’t be modified after you save them.
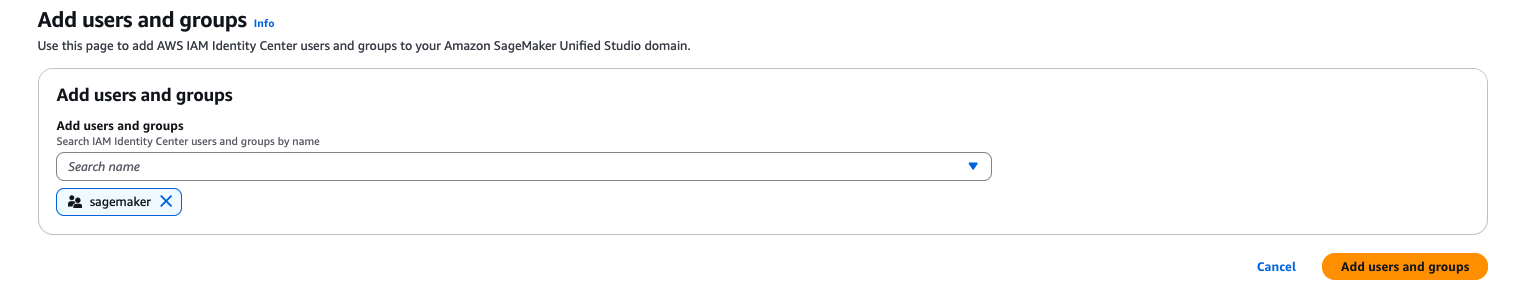
- For those who’ve chosen to require assignments, use the Add customers and teams part so as to add SAML customers and teams to your area.
Now, customers will be capable to entry SageMaker Unified Studio utilizing the area URL with their SSO credentials.
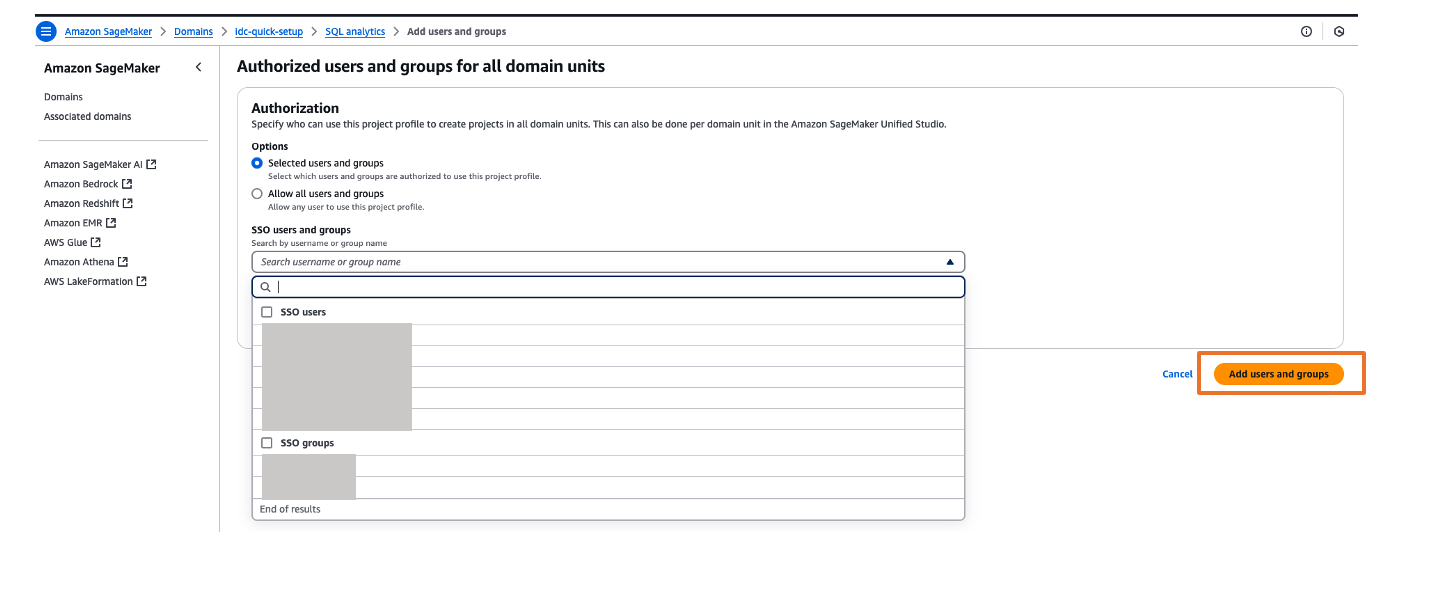
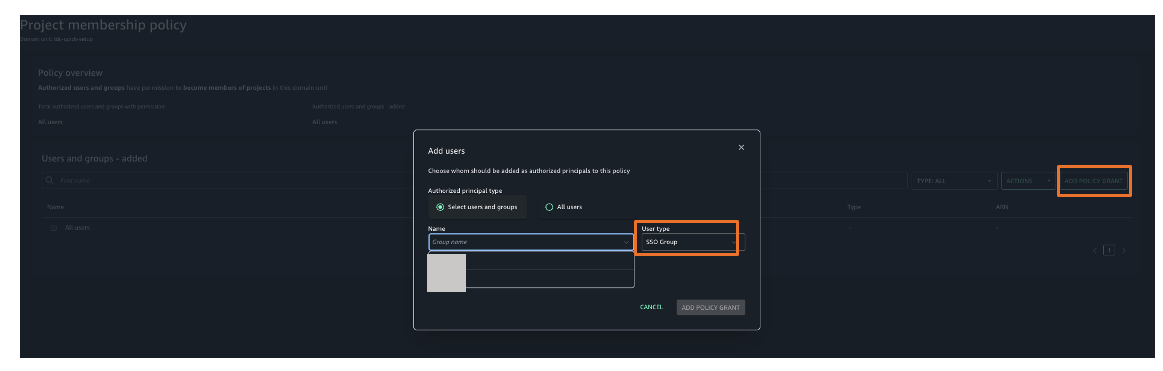
You’ll be able to discover totally different initiatives in your customers and assign these initiatives based mostly in your IdP consumer teams for fine-grained entry controls. For instance, you’ll be able to create totally different SAML consumer teams based mostly on their job perform in Ping Identification, then assign these Ping Identification teams to the unifiedstudio SAML software in Ping Identification, after which assign these Ping Identification SAML teams to their respective undertaking profiles in SageMaker Unified Studio. To assign undertaking profiles for his or her respective teams, select the Venture profiles tab and select your undertaking profile. On the Approved customers and teams web page, select Add, then select SSO teams. Select Add customers and teams button to finish the undertaking profile project.
Validate entry with Ping Identification customers
Full the next steps to validate entry:
- On the SageMaker area particulars web page, select the hyperlink for the SageMaker Unified Studio URL.
- Log in together with your consumer credentials.
After profitable login, you’ll be redirected to the SageMaker Unified Studio dwelling web page. Right here, you’ll be able to discover totally different initiatives to your customers and assign these initiatives based mostly in your SAML consumer teams for fine-grained entry management.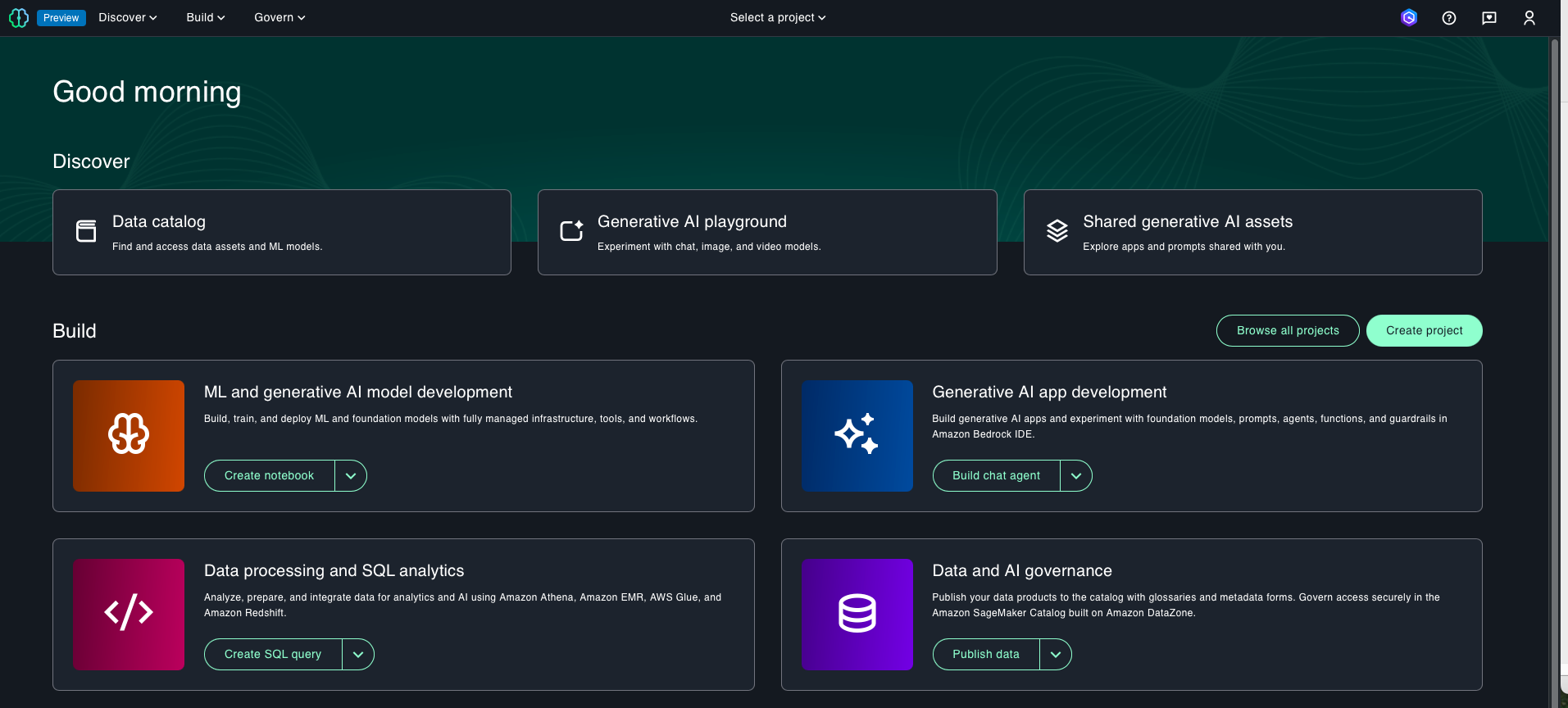
- To assign an authorization coverage, these Govern after which Area items.
- Select your SageMaker area, then select an appropriate authorization coverage. For this instance, we select Venture creation coverage.
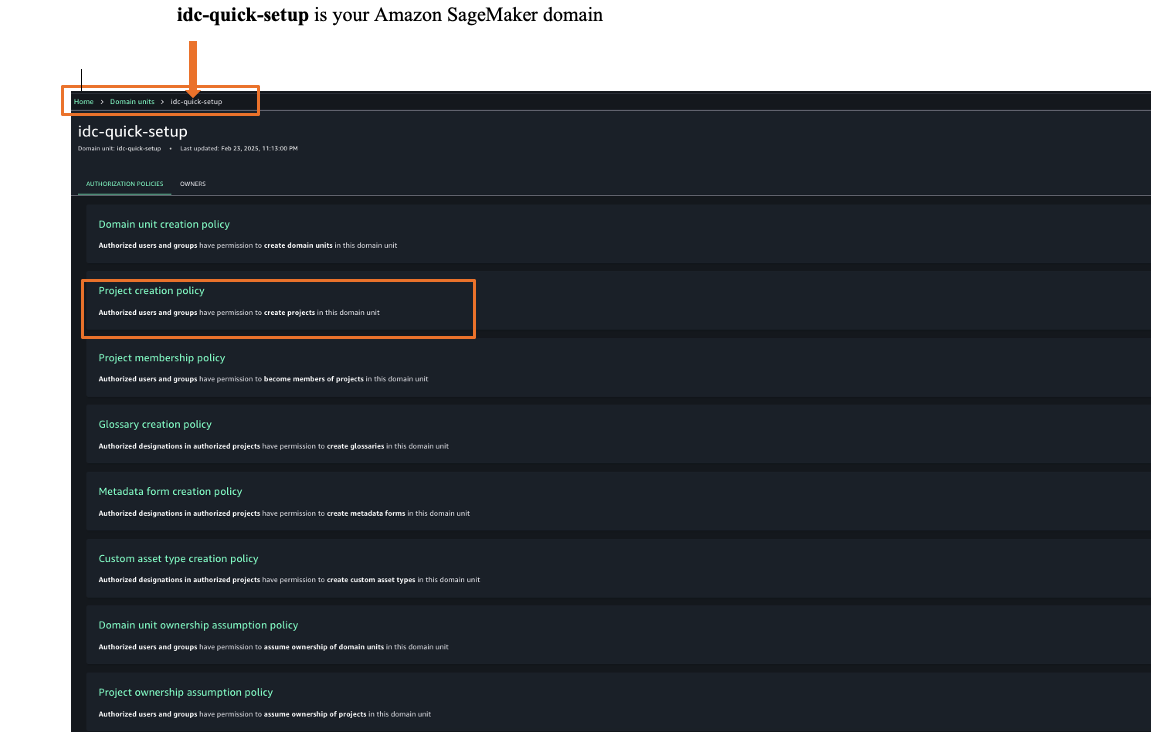
- Select Add coverage grant to assign consumer teams or customers to their respective undertaking profiles.
You might have efficiently federated SageMaker Unified Studio with Ping Identification as an IdP with IAM Identification Middle. You’ll be able to hook up with SageMaker Unified Studio through the use of your Ping Identification credentials.
Clear up
After you check out this answer, bear in mind to delete the assets you created to keep away from incurring future costs. For directions to delete your SageMaker Unified Studio area, check with Delete domains. If you wish to delete your Ping Identification account, attain out to Ping Identification for help.
Conclusion
On this put up, we demonstrated how one can arrange Ping Identification as an IdP over SAML authentication for SageMaker Unified Studio entry by means of IAM Identification Middle federation. To be taught extra, check with the Amazon SageMaker Unified Studio Person Information, which offers steering on how one can construct information and AI purposes utilizing SageMaker.
In regards to the authors

