In my final two blogs, I delved into the outcomes of the 2025 Cisco Segmentation Report to spotlight the significance of macro- and micro-segmentation and to establish the first challenges hindering segmentation journeys. In the present day, I dive additional into the survey outcomes to debate the advantages organizations can obtain once they efficiently implement a twin macro- and micro-approach to segmentation. The objective, after all, is to proceed highlighting insights into the present state of this vital cybersecurity idea and the place it might be headed sooner or later.
Three Advantages of a Profitable Segmentation Technique
The excellent news is that the survey outcomes point out that organizations additional alongside of their segmentation journeys are certainly attaining measurable advantages from their profitable macro- and micro-segmentation implementations.
1. Comprise Breaches
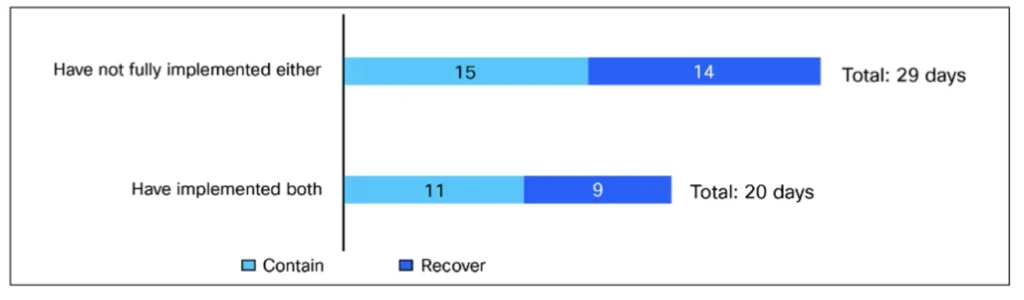
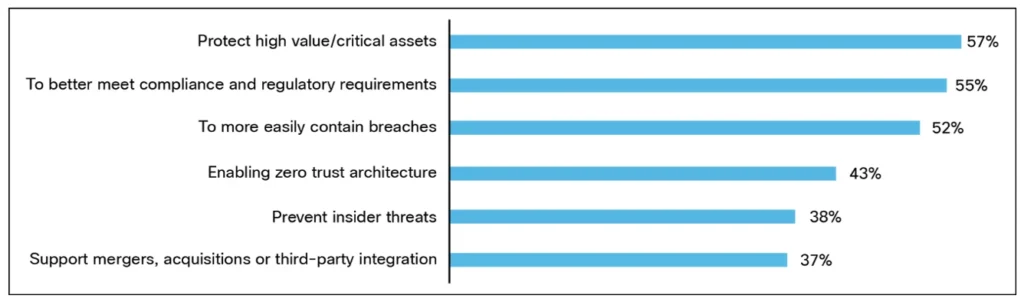
Everyone knows that it’s not a matter of in case your group will get breached, it’s a matter of when. And, when it occurs, you’ll must detect the assault, establish its targets, perceive the affect, comprise the breach, and get techniques again up and working as shortly as doable. Implementing each macro- and micro-segmentation permits sooner breach response by offering organizations with pre-made defensive limitations. The survey responses help this. Respondents from organizations which have absolutely applied macro- and micro-segmentation say that breach containment and restoration time take as much as 20 days on common, in contrast with the reported 29 days for organizations with out full implementation of each. This 31% sooner restoration time is an actual, measurable affect of a twin macro- and micro-segmentation strategy. It isn’t onerous to think about how the discount in containment and restoration comes about—in spite of everything, segmentation impedes attackers, thereby decreasing the post-breach effort.
2. Defend Excessive-Worth Property
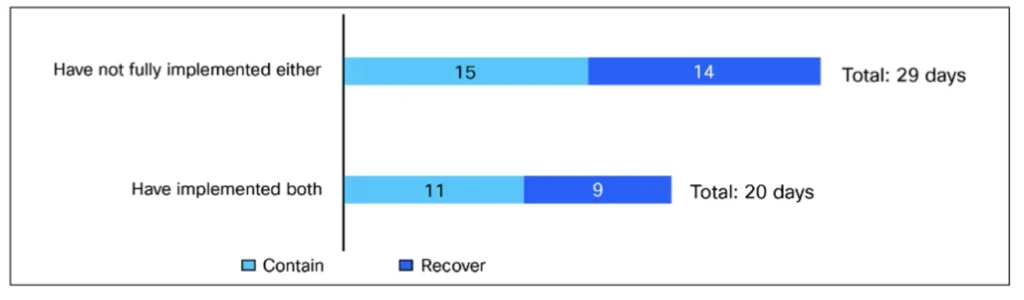
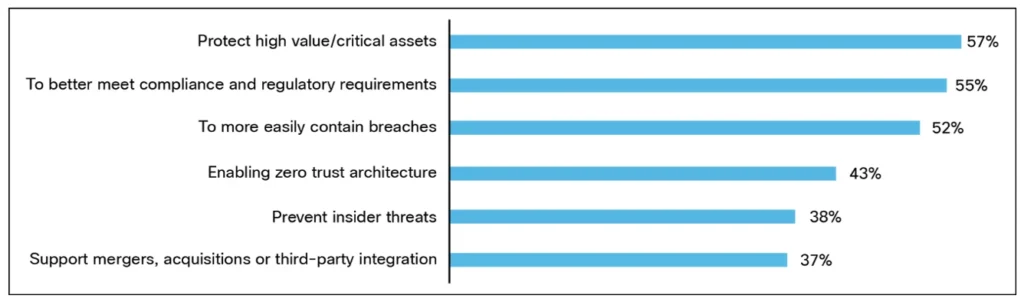
In line with the report, defending high-value/vital property (57%) is the more than likely driver for organizations implementing segmentation, together with delicate knowledge, functions, and techniques which might be vital for enterprise operations and continuity. On its face, defending vital property is beneficial, however stopping these property from falling into the fingers of risk actors preserves the group’s status amongst prospects, staff, shareholders, and different stakeholders. For instance, a corporation’s monetary data might be protected by deploying segmentation that takes under consideration the identification of customers. With such segmentation, solely staff within the finance group are allowed entry to finance functions. Whereas the sort of segmentation doesn’t stop all types of assaults, it does elevate the barrier to profitable assaults.
3. Meet Compliance Necessities
As soon as the basics of asset safety are in place, mature organizations lengthen segmentation into compliance-driven areas. This displays each regulatory calls for—in some main trade segments, similar to retail, healthcare, and finance, organizations’ viability depends upon their adherence to compliance requirements, together with PCI-DSS, HIPAA, and SOX (respectively)—and the pursuit of extra complete management throughout complicated environments. The survey report reveals that organizations with full segmentation deployment are extra doubtless (67% vs 54%) to have additionally segmented workloads with compliance necessities.
Acknowledging the Affect of Segmentation
Organizations which have absolutely applied a twin strategy to segmentation (33% of respondents) can level to measurable affect—together with higher breach containment, asset safety, and better concentrate on compliance. Clearly, these are sufficient incentives for the remaining organizations (67% of respondents) that don’t but have full segmentation deployments to take motion.
Should you haven’t already, take a look at the primary two blogs within the sequence, which debate the significance of segmentation and the challenges organizations face when implementing segmentation initiatives. Within the meantime, obtain the 2025 Cisco Segmentation Report back to be taught extra in regards to the state of segmentation in the present day and the place you match in opposition to related organizations.
We’d love to listen to what you suppose! Ask a query and keep linked with Cisco Safety on social media.
Cisco Safety Social Media

