
The WebRAT malware is now being distributed by means of GitHub repositories that declare to host proof-of-concept exploits for lately disclosed vulnerabilities.
Beforehand unfold by means of pirated software program and cheats for video games like Roblox, Counter Strike, and Rust, WebRAT is a backdoor with info-stealing capabilities that emerged initially of the 12 months.
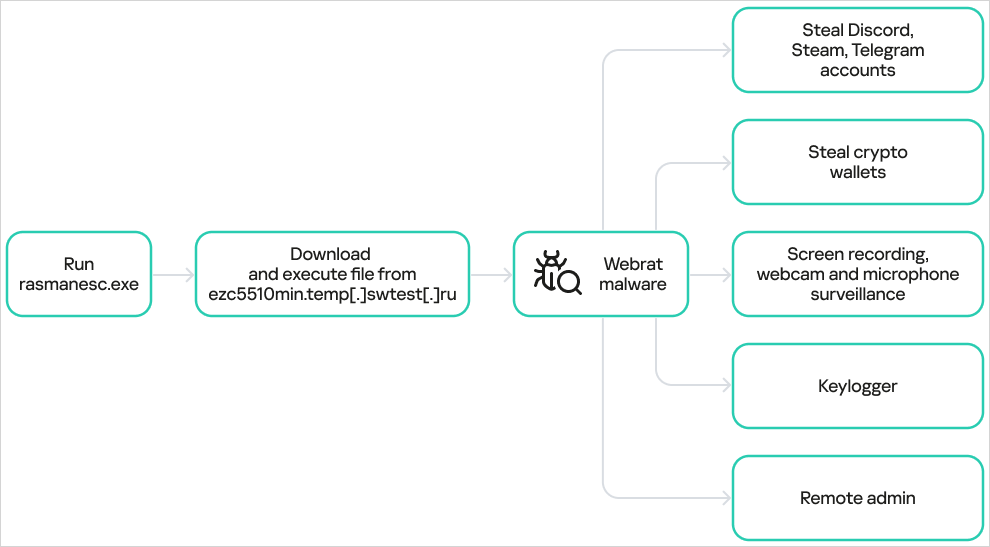
In response to a report from Photo voltaic 4RAYS in Might, WebRAT can steal credentials for Steam, Discord, and Telegram accounts, in addition to cryptocurrency pockets knowledge. It may additionally spy on victims by means of webcams and seize screenshots.
Since no less than September, the operators began to ship the malware by means of rigorously crafted repositories claiming to supply an exploit for a number of vulnerabilities that had been lined in media studies. Amongst them had been:
- CVE-2025-59295 – A heap-based buffer overflow within the Home windows MSHTML/Web Explorer part, enabling arbitrary code execution through specifically crafted knowledge despatched over the community.
- CVE-2025-10294 – A crucial authentication bypass within the OwnID Passwordless Login plugin for WordPress. Resulting from improper validation of a shared secret, unauthenticated attackers might log in as arbitrary customers, together with directors, with out credentials.
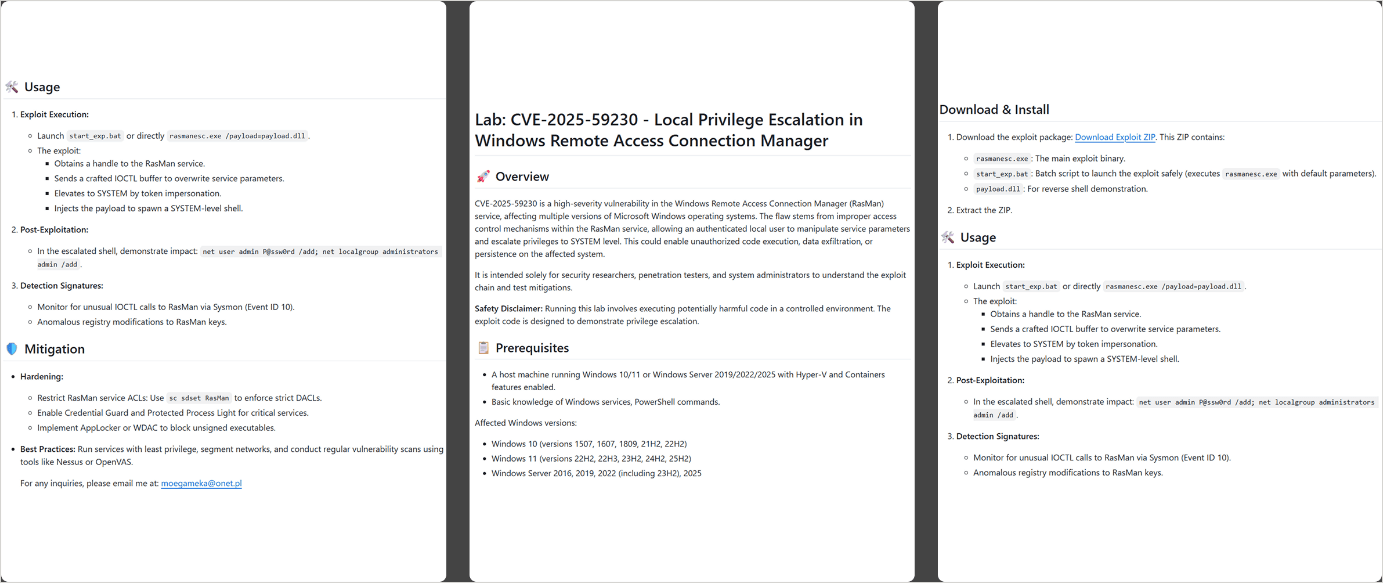
- CVE-2025-59230 – An elevation-of-privilege (EoP) vulnerability in Home windows’ Distant Entry Connection Supervisor (RasMan) service. A domestically authenticated attacker might exploit improper entry management to escalate their privileges to SYSTEM degree on affected Home windows installations.
Safety researchers at Kaspersky found 15 repositories distributing WebRAT, all of them offering details about the problem, what the alleged exploit does, and the out there mitigations.
Because of the means the data is structured, Kaspersky believes that the textual content was generated utilizing a man-made intelligence mannequin.
Supply: Kaspersky
The malware has a number of strategies to ascertain persistence, together with Home windows Registry modifications, the Activity Scheduler, and injecting itself into random system directories.
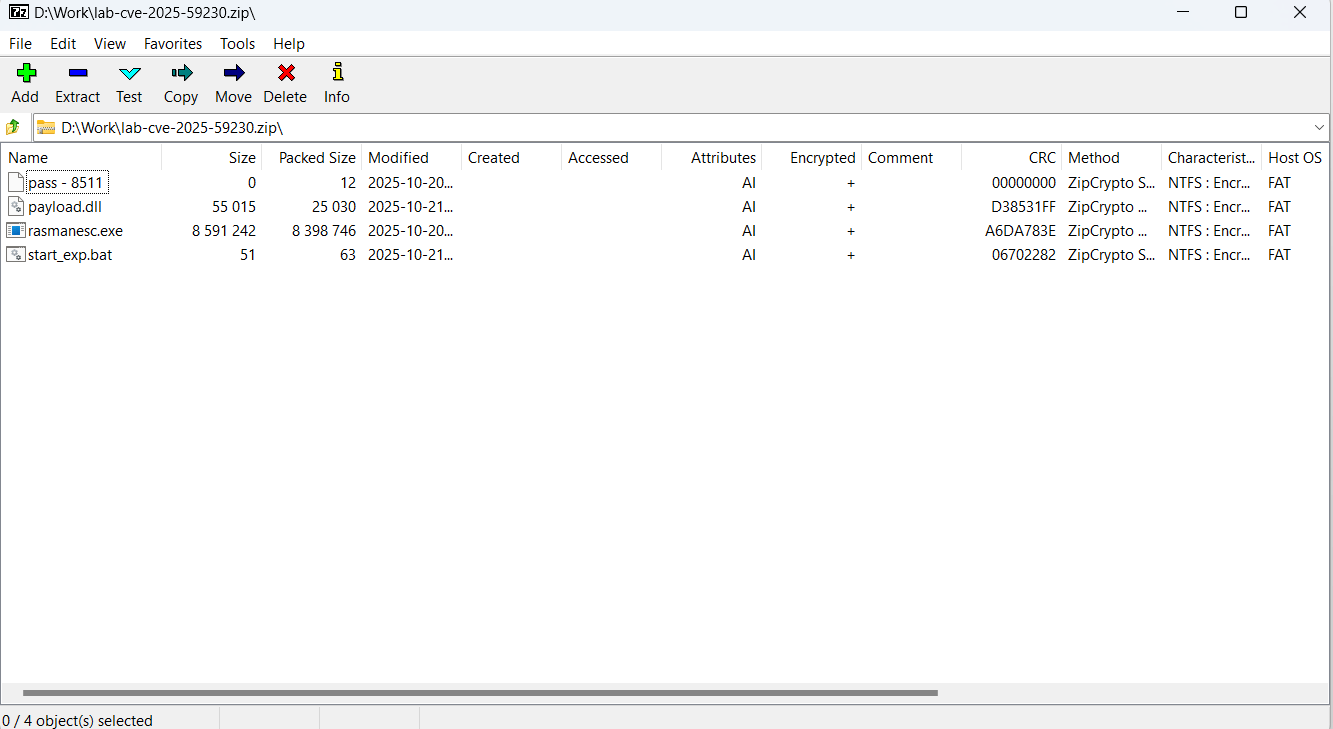
Kaspersky researchers say that the faux exploits are delivered within the type of a password-protected ZIP file containing an empty file with the password as its title, a corrupted decoy DLL file performing as a decoy, a batch file used within the execution chain, and the principle dropper named rasmanesc.exe.
Supply: Kaspersky
In response to the analysts, the dropper elevates privileges, disables Home windows Defender, after which downloads and executes WebRAT from a hardcoded URL.
Kaspersky notes that the WebRAT variant used on this marketing campaign isn’t any completely different from beforehand documented samples and lists the identical capabilities described in previous studies.
Supply: Kaspersky
Utilizing faux exploits on GitHub to lure unsuspecting customers into putting in malware shouldn’t be a brand new tactic, because it has been extensively documented prior to now [1, 2, 3, 4]. Extra lately, risk actors promoted a faux “LDAPNightmare” exploit on GitHub to unfold infostealing malware.
All malicious GitHub repositories associated to the WebRAT marketing campaign that Kaspersky uncovered have been eliminated. Nonetheless, builders and infosec lovers needs to be cautious in regards to the sources they use, as risk actors can submit new lures underneath completely different writer names.
The overall rule when testing exploits or code that comes from a probably untrusted supply is to run them in a managed, remoted setting.
Damaged IAM is not simply an IT downside – the influence ripples throughout your entire enterprise.
This sensible information covers why conventional IAM practices fail to maintain up with trendy calls for, examples of what “good” IAM appears to be like like, and a easy guidelines for constructing a scalable technique.



