Menace actors have been exploiting a command injection vulnerability in Array AG Collection VPN gadgets to plant webshells and create rogue customers.
Array Networks fastened the vulnerability in a Might safety replace, however has not assigned an identifier, complicating efforts to trace the flaw and patch administration.
An advisory from Japan’s Pc Emergency and Response Crew (CERT) warns that hackers have been exploiting the vulnerability since at the very least August in assaults focusing on organizations within the nation.
The company stories that the assaults originate from the IP tackle 194.233.100[.]138, which can also be used for communications.
“Within the incidents confirmed by JPCERT/CC, a command was executed trying to put a PHP webshell file within the path /ca/aproxy/webapp/,” reads the bulletin (machine translated).
The flaw impacts ArrayOS AG 9.4.5.8 and earlier variations, together with AG Collection {hardware} and digital home equipment with the ‘DesktopDirect’ distant entry characteristic enabled.
JPCERT says that Array OS model 9.4.5.9 addresses the issue and offers the next workarounds if updating is just not attainable:
- If the DesktopDirect characteristic is just not in use, disable all DesktopDirect companies
- Use URL filtering to dam entry to URLs containing a semicolon
Array Networks AG Collection is a line of safe entry gateways that depend on SSL VPNs to create encrypted tunnels for safe distant entry to company networks, functions, desktops, and cloud assets.
Sometimes, they’re utilized by massive organizations and enterprises that must facilitate distant or cell work.
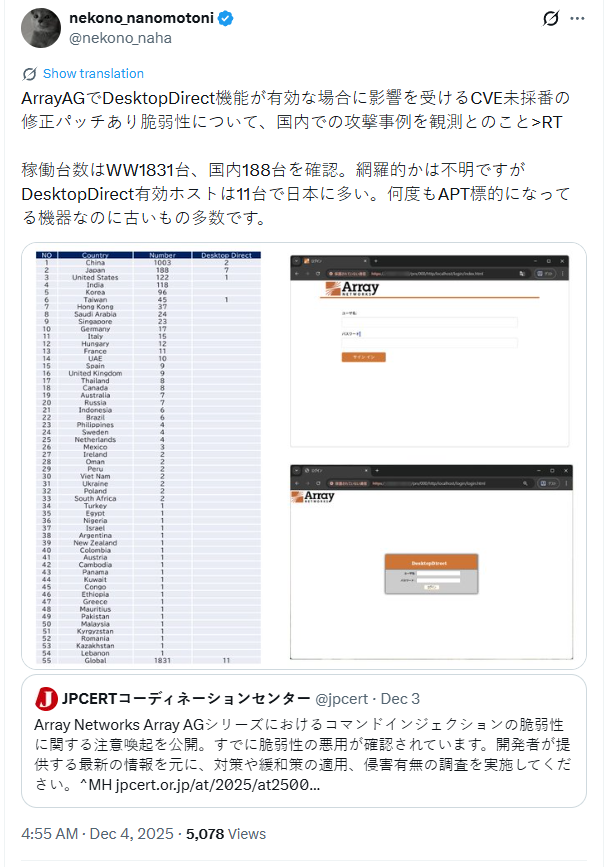
Macnica’s safety researcher, Yutaka Sejiyama, reported on X that his scans returned 1,831 ArrayAG cases worldwide, primarily in China, Japan, and the US.
The researcher verified that at the very least 11 hosts have the DesktopDirect characteristic enabled, however cautioned that the potential for extra hosts with DesktopDirect lively is important.
“As a result of this product’s consumer base is concentrated in Asia and many of the noticed assaults are in Japan, safety distributors and safety organizations outdoors Japan haven’t been paying shut consideration,” Sejiyama informed BleepingComputer.
BleepingComputer contacted Array Networks to ask whether or not they plan to publish a CVE-ID and an official advisory for the actively exploited flaw, however a reply was not accessible by publication time.
Final yr, CISA warned about lively exploitation focusing on CVE-2023-28461, a crucial distant code execution in Array Networks AG and vxAG ArrayOS.
Damaged IAM is not simply an IT drawback – the affect ripples throughout your complete enterprise.
This sensible information covers why conventional IAM practices fail to maintain up with fashionable calls for, examples of what “good” IAM appears like, and a easy guidelines for constructing a scalable technique.