Late final 12 months, safety researchers made a startling discovery: Kremlin-backed disinformation campaigns have been bypassing moderation on social media platforms by leveraging the identical malicious promoting know-how that powers a sprawling ecosystem of on-line hucksters and web site hackers. A brand new report on the fallout from that investigation finds this darkish advert tech trade is much extra resilient and incestuous than beforehand recognized.

Picture: Infoblox.
In November 2024, researchers on the safety agency Qurium printed an investigation into “Doppelganger,” a disinformation community that promotes pro-Russian narratives and infiltrates Europe’s media panorama by pushing pretend information via a community of cloned web sites.
Doppelganger campaigns use specialised hyperlinks that bounce the customer’s browser via a protracted collection of domains earlier than the pretend information content material is served. Qurium discovered Doppelganger depends on a complicated “area cloaking” service, a know-how that enables web sites to current totally different content material to search engines like google in comparison with what common guests see. The usage of cloaking providers helps the disinformation websites stay on-line longer than they in any other case would, whereas making certain that solely the focused viewers will get to view the meant content material.
Qurium found that Doppelganger’s cloaking service additionally promoted on-line relationship websites, and shared a lot of the identical infrastructure with VexTrio, which is considered the oldest malicious visitors distribution system (TDS) in existence. Whereas TDSs are generally utilized by respectable promoting networks to handle visitors from disparate sources and to trace who or what’s behind every click on, VexTrio’s TDS largely manages internet visitors from victims of phishing, malware, and social engineering scams.
BREAKING BAD
Digging deeper, Qurium seen Doppelganger’s cloaking service used an Web supplier in Switzerland as the primary entry level in a series of area redirections. In addition they seen the identical infrastructure hosted a pair of co-branded affiliate marketing online providers that have been driving visitors to sketchy grownup relationship websites: LosPollos[.]com and TacoLoco[.]co.
The LosPollos advert community incorporates many parts and references from the hit collection “Breaking Dangerous,” mirroring the fictional “Los Pollos Hermanos” restaurant chain that served as a cash laundering operation for a violent methamphetamine cartel.
The LosPollos promoting community invokes characters and themes from the hit present Breaking Dangerous. The brand for LosPollos (higher left) is the picture of Gustavo Fring, the fictional hen restaurant chain proprietor within the present.
Associates who join with LosPollos are given JavaScript-heavy “smartlinks” that drive visitors into the VexTrio TDS, which in flip distributes the visitors amongst a wide range of promoting companions, together with relationship providers, sweepstakes provides, bait-and-switch cellular apps, monetary scams and malware obtain websites.
LosPollos associates usually sew these good hyperlinks into WordPress web sites which have been hacked through recognized vulnerabilities, and people associates will earn a small fee every time an Web person referred by any of their hacked websites falls for one among these lures.
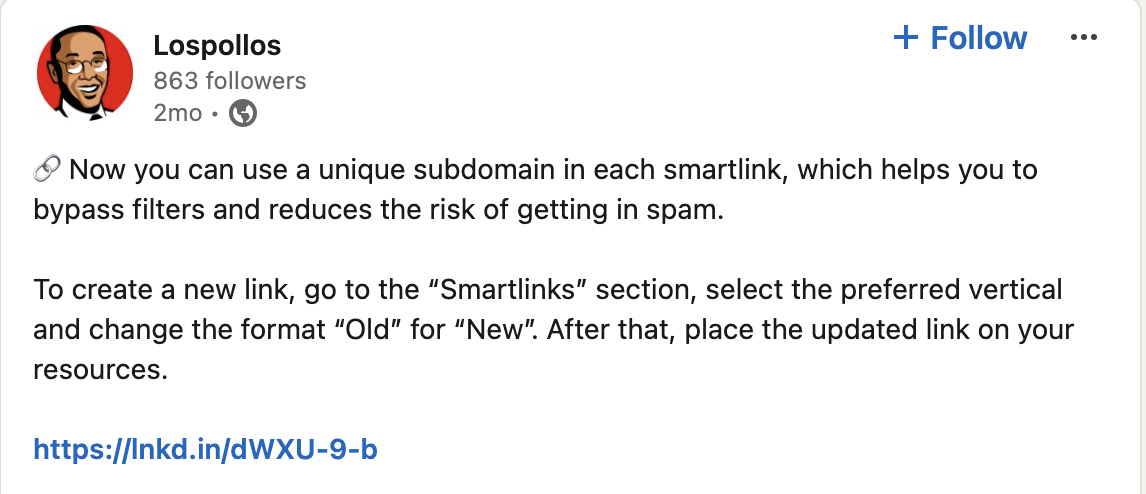
The Los Pollos promoting community selling itself on LinkedIn.
In keeping with Qurium, TacoLoco is a visitors monetization community that makes use of misleading techniques to trick Web customers into enabling “push notifications,” a cross-platform browser customary that enables web sites to indicate pop-up messages which seem outdoors of the browser. For instance, on Microsoft Home windows programs these notifications usually present up within the backside proper nook of the display — simply above the system clock.
Within the case of VexTrio and TacoLoco, the notification approval requests themselves are misleading — disguised as “CAPTCHA” challenges designed to tell apart automated bot visitors from actual guests. For years, VexTrio and its companions have efficiently tricked numerous customers into enabling these web site notifications, that are then used to constantly pepper the sufferer’s machine with a wide range of phony virus alerts and deceptive pop-up messages.
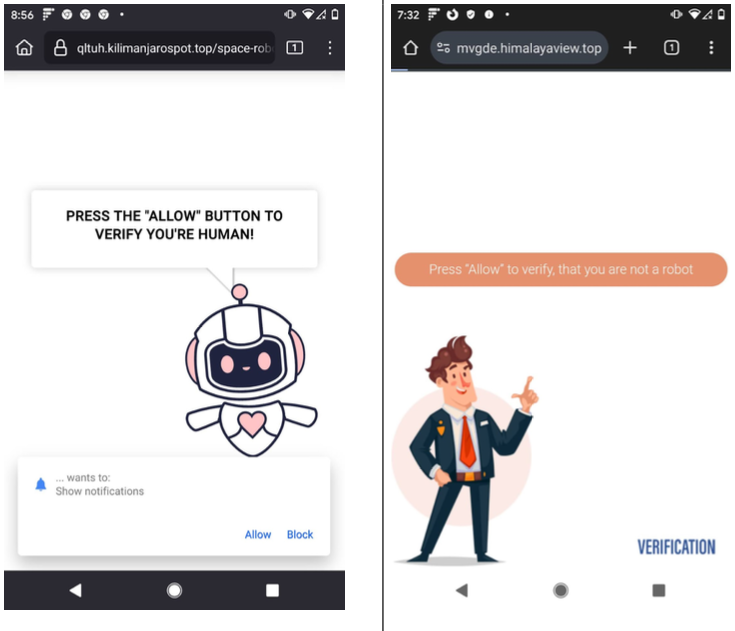
Examples of VexTrio touchdown pages that lead customers to just accept push notifications on their machine.
In keeping with a December 2024 annual report from GoDaddy, almost 40 % of compromised web sites in 2024 redirected guests to VexTrio through LosPollos smartlinks.
ADSPRO AND TEKNOLOGY
On November 14, 2024, Qurium printed analysis to help its findings that LosPollos and TacoLoco have been providers operated by Adspro Group, an organization registered within the Czech Republic and Russia, and that Adspro runs its infrastructure on the Swiss internet hosting suppliers C41 and Teknology SA.
Qurium famous the LosPollos and TacoLoco websites state that their content material is copyrighted by ByteCore AG and SkyForge Digital AG, each Swiss corporations which might be run by the proprietor of Teknology SA, Guilio Vitorrio Leonardo Cerutti. Additional investigation revealed LosPollos and TacoLoco have been apps developed by an organization known as Holacode, which lists Cerutti as its CEO.
The apps marketed by Holacode embody quite a few VPN providers, in addition to one known as Spamshield that claims to cease undesirable push notifications. However in January, Infoblox mentioned they examined the app on their very own cellular units, and located it hides the person’s notifications, after which after 24 hours stops hiding them and calls for cost. Spamshield subsequently modified its developer identify from Holacode to ApLabz, though Infoblox famous that the Phrases of Service for a number of of the rebranded ApLabz apps nonetheless referenced Holacode of their phrases of service.
Extremely, Cerutti threatened to sue me for defamation earlier than I’d even uttered his identify or despatched him a request for remark (Cerutti despatched the unsolicited authorized risk again in January after his firm and my identify have been merely tagged in an Infoblox submit on LinkedIn about VexTrio).
Requested to touch upon the findings by Qurium and Infoblox, Cerutti vehemently denied being related to VexTrio. Cerutti asserted that his corporations all strictly adhere to the laws of the international locations through which they function, and that they’ve been fully clear about all of their operations.
“We’re a gaggle working within the promoting and advertising and marketing house, with an affiliate community program,” Cerutti responded. “I’m not [going] to say we’re good, however I strongly declare we now have no reference to VexTrio in any respect.”
“Sadly, as a giant participant on this house we additionally get to take care of loads of writer fraud, sketchy visitors, pretend clicks, bots, hacked, listed and resold writer accounts, and so on, and so on.,” Cerutti continued. “We bleed a number of cash to such malpractices and conduct common inner screenings and audits in a continuing battle to take away dangerous visitors sources. Additionally it is a extremely aggressive house, the place some upstarts will typically play soiled in opposition to extra established mainstream gamers like us.”
Working with Qurium, researchers on the safety agency Infoblox launched particulars about VexTrio’s infrastructure to their trade companions. Simply 4 days after Qurium printed its findings, LosPollos introduced it was suspending its push monetization service. Lower than a month later, Adspro had rebranded to Aimed World.
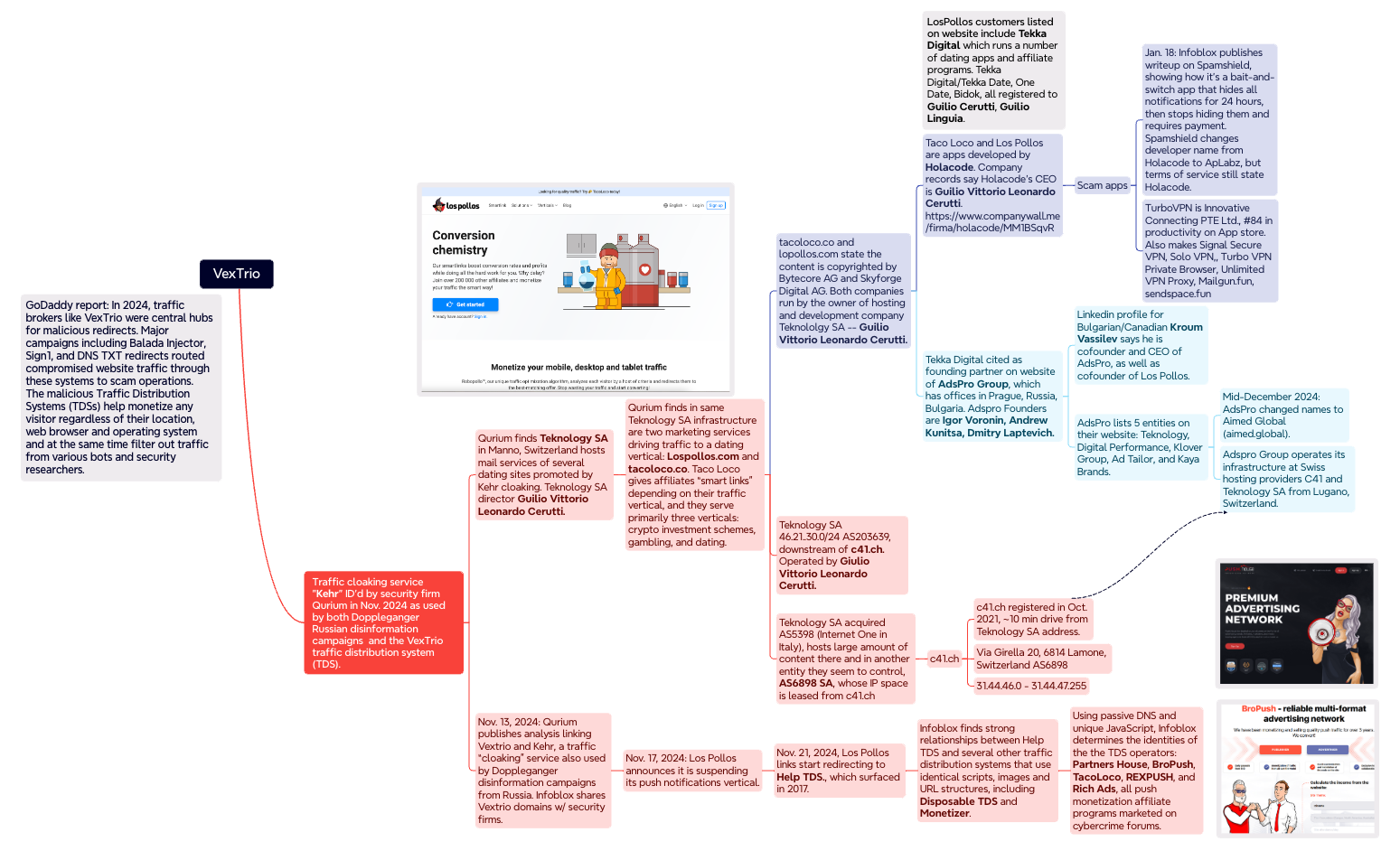
A thoughts map illustrating among the key findings and connections within the Infoblox and Qurium investigations. Click on to enlarge.
A REVEALING PIVOT
In March 2025, researchers at GoDaddy chronicled how DollyWay — a malware pressure that has constantly redirected victims to VexTrio all through its eight years of exercise — all of the sudden stopped doing that on November 20, 2024. Nearly in a single day, DollyWay and a number of other different malware households that had beforehand used VexTrio started pushing their visitors via one other TDS known as Assist TDS.
Digging additional into historic DNS information and the distinctive code scripts utilized by the Assist TDS, Infoblox decided it has lengthy loved an unique relationship with VexTrio (no less than till LosPollos ended its push monetization service in November).
In a report launched immediately, Infoblox mentioned an exhaustive evaluation of the JavaScript code, web site lures, smartlinks and DNS patterns utilized by VexTrio and Assist TDS linked them with no less than 4 different TDS operators (not counting TacoLoco). These 4 entities — Companions Home, BroPush, RichAds and RexPush — are all Russia-based push monetization applications that pay associates to drive signups for a wide range of schemes, however largely on-line relationship providers.
“As Los Pollos push monetization ended, we’ve seen a rise in pretend CAPTCHAs that drive person acceptance of push notifications, notably from Companions Home,” the Infoblox report reads. “The connection of those business entities stays a thriller; whereas they’re actually long-time companions redirecting visitors to 1 one other, and so they all have a Russian nexus, there isn’t any overt frequent possession.”
Renee Burton, vp of risk intelligence at Infoblox, mentioned the safety trade usually treats the misleading strategies utilized by VexTrio and different malicious TDSs as a sort of legally gray space that’s largely related to much less harmful safety threats, corresponding to adware and scareware.
However Burton argues that this view is myopic, and helps perpetuate a darkish adtech trade that additionally pushes loads of straight-up malware, noting that a whole lot of hundreds of compromised web sites world wide yearly redirect victims to the tangled internet of VexTrio and VexTrio-affiliate TDSs.
“These TDSs are a nefarious risk, as a result of they’re those you possibly can hook up with the supply of issues like data stealers and scams that value shoppers billions of {dollars} a 12 months,” Burton mentioned. “From a bigger strategic perspective, my takeaway is that Russian organized crime has management of malicious adtech, and these are simply among the many teams concerned.”
WHAT CAN YOU DO?
As KrebsOnSecurity warned method again in 2020, it’s a good suggestion to be very sparing in approving notifications when shopping the Internet. In lots of instances these notifications are benign, however as we’ve seen there are quite a few dodgy corporations which might be paying web site house owners to put in their notification scripts, after which reselling that communications pathway to scammers and on-line hucksters.
If you happen to’d like to forestall websites from ever presenting notification requests, the entire main browser makers allow you to do that — both throughout the board or on a per-website foundation. Whereas it’s true that blocking notifications fully can break the performance of some web sites, doing this for any units you handle on behalf of your much less tech-savvy mates or members of the family would possibly find yourself saving everybody plenty of headache down the highway.
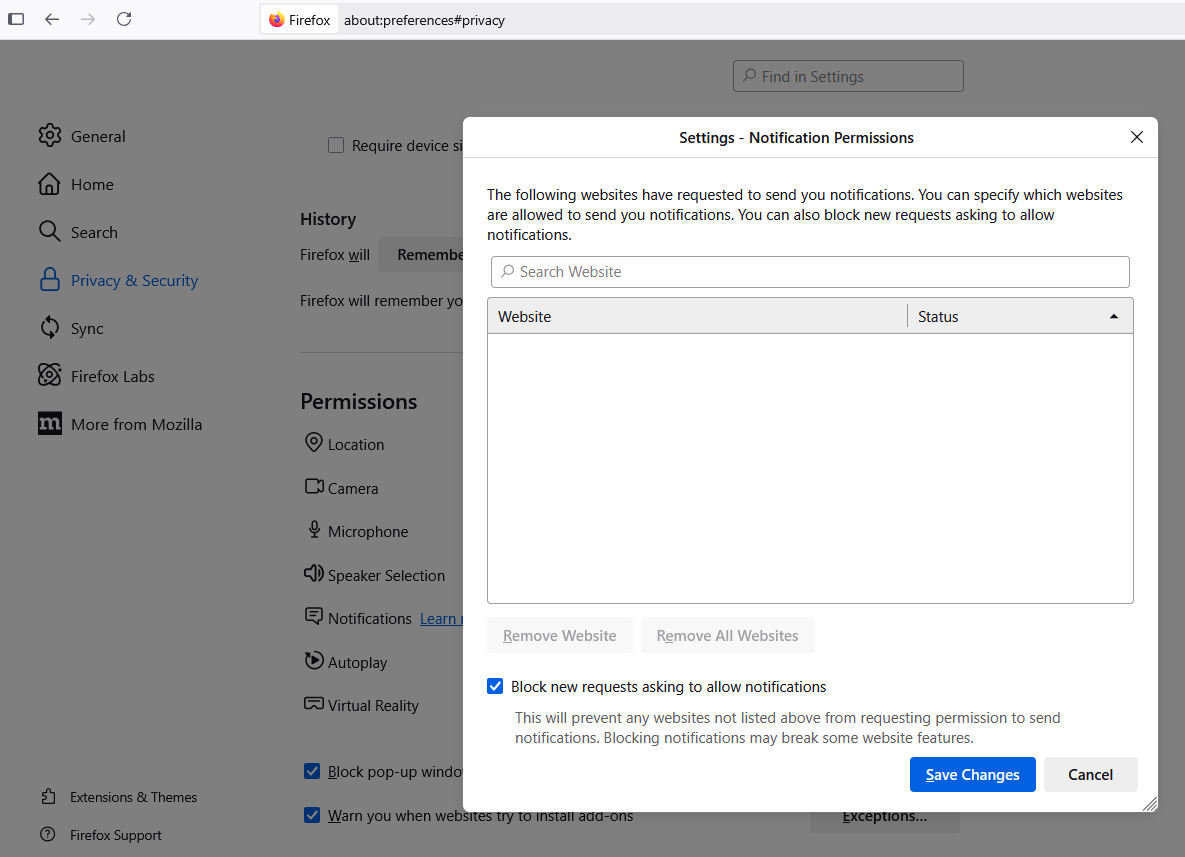
To change web site notification settings in Mozilla Firefox, navigate to Settings, Privateness & Safety, Permissions, and click on the “Settings” tab subsequent to “Notifications.” That web page will show any notifications already permitted and let you edit or delete any entries. Tick the field subsequent to “Block new requests asking to permit notifications” to cease them altogether.
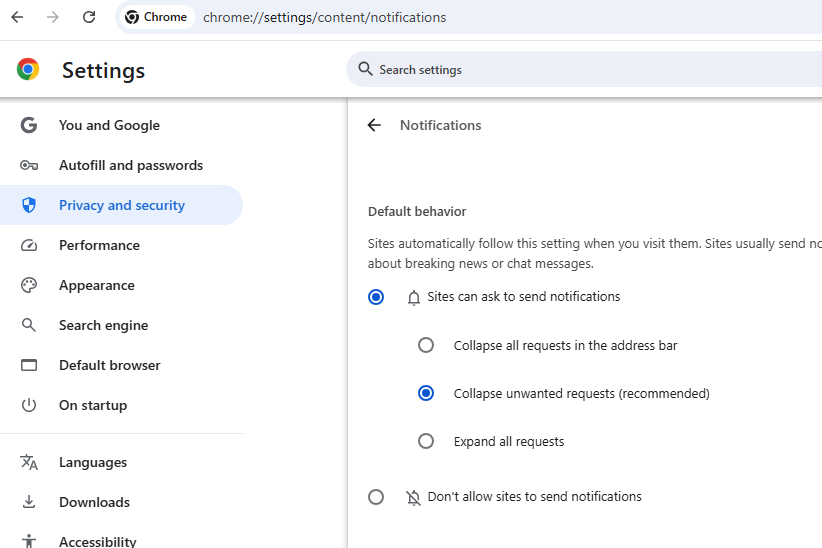
In Google Chrome, click on the icon with the three dots to the fitting of the deal with bar, scroll all the way in which all the way down to Settings, Privateness and Safety, Website Settings, and Notifications. Choose the “Don’t permit websites to ship notifications” button if you wish to banish notification requests ceaselessly.
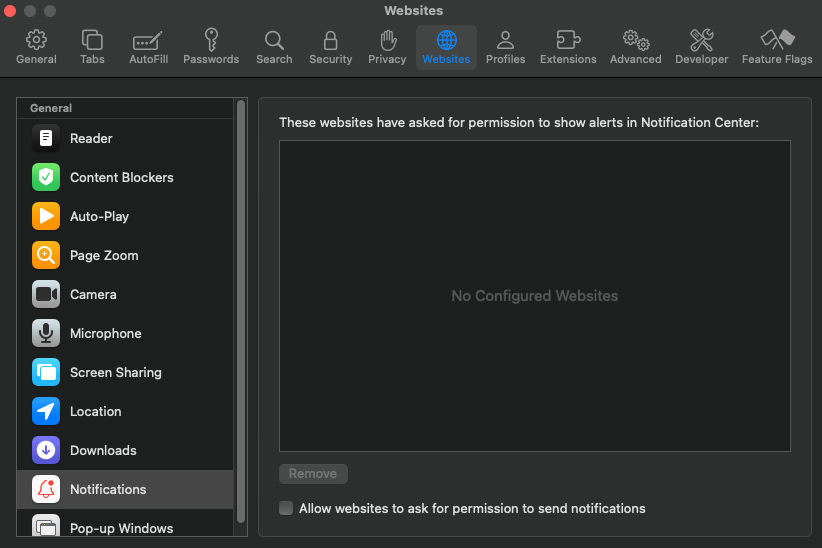
In Apple’s Safari browser, go to Settings, Web sites, and click on on Notifications within the sidebar. Uncheck the choice to “permit web sites to ask for permission to ship notifications” for those who want to flip off notification requests fully.