There are many phish within the sea.
Hundreds of thousands of bogus phishing emails land in thousands and thousands of inboxes every day with one goal in thoughts—to tear off the recipient. Whether or not they’re out to crack your checking account, steal private info, or each, you may learn to spot phishing emails and preserve your self protected.
And a few of immediately’s phishing emails are certainly getting harder to identify.
They appear like they arrive from firms and belief, like your financial institution, your bank card firm, or companies like Netflix, PayPal, and Amazon. And a few of them look convincing. The writing and the format are crisp, and the general presentation appears to be like skilled. But nonetheless, there’s nonetheless one thing off about them.
And there’s actually one thing improper with that e mail. It was written by a scammer. Phishing emails make use of a bait-and-hook tactic, the place an pressing or engaging message is the bait and malware or a hyperlink to a phony login web page is the hook.
As soon as the hook will get set, a number of issues may occur. That phony login web page might steal account and private info. Or that malware may set up keylogging software program that steals info, viruses that open a again door by which knowledge can get hijacked, or ransomware that holds a tool and its knowledge hostage till a charge is paid.
Once more, you may sidestep these assaults if you know the way to identify them. There are indicators.
Let’s have a look at how prolific these assaults are, choose aside a number of examples, after which break down the issues it is best to search for.
Phishing assault statistics—the thousands and thousands of makes an attempt made every year.
Within the U.S. alone, greater than 300,000 victims reported a phishing assault to the FBI in 2022. Phishing assaults topped the checklist of reported complaints, roughly six occasions better than the second prime offender, private knowledge breaches. The precise determine is undoubtedly increased, provided that not all assaults get reported.
Taking a look at phishing assaults worldwide, one research means that greater than 255 million phishing makes an attempt have been made within the second half of 2022 alone. That marks a 61% improve over the earlier 12 months. One other research concluded that 1.2 in each 100 emails despatched contained a phishing assault.
But scammers gained’t at all times forged such a large web. Statistics level to an increase in focused spear phishing, the place the attacker goes after a selected individual. They are going to typically goal individuals at companies who’ve the authority to switch funds or make funds. Different targets embody individuals who have entry to delicate info like passwords, proprietary knowledge, and account info.
As such, the value of those assaults can get pricey. In 2022, the FBI acquired 21,832 complaints from companies that stated they fell sufferer to a spear phishing assault. The adjusted losses have been over $2.7 billion—a mean value of $123,671 per assault.
So whereas exacting phishing assault statistics stay considerably elusive, there’s no query that phishing assaults are prolific. And dear.
What does a phishing assault appear to be?
Almost each phishing assault sends an pressing message. One designed to get you to behave.
Some examples …
- “You’ve gained our money prize drawing! Ship us your banking info so we are able to deposit your winnings!”
- “You owe again taxes. Ship cost instantly utilizing this hyperlink or we are going to refer your case to legislation enforcement.”
- “We noticed what may be uncommon exercise in your bank card. Comply with this hyperlink to substantiate your account info.”
- “There was an unauthorized try to entry your streaming account. Click on right here to confirm your id.”
- “Your bundle was undeliverable. Click on the connected doc to offer supply directions.”
When set inside a pleasant design and paired with some official-looking logos, it’s simple to see why loads of individuals click on the hyperlink or attachment that comes with messages like these.
And that’s the difficult factor with phishing assaults. Scammers have leveled up their sport in recent times. Their phishing emails can look convincing. Not way back, you could possibly level to misspellings, awful grammar, poor design, and logos that appeared stretched or that used the improper colours. Poorly executed phishing assaults like that also make their manner into the world. Nevertheless, it’s more and more frequent to see much more subtle assaults immediately. Assaults that seem like a real message or discover.
Working example:
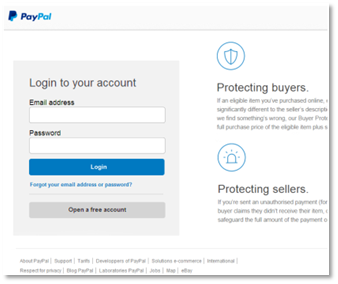 Say you bought an e mail that stated your PayPal account had a difficulty. Would you sort your account info right here should you discovered your self on this web page? If that’s the case, you’ll have handed over your info to a scammer.
Say you bought an e mail that stated your PayPal account had a difficulty. Would you sort your account info right here should you discovered your self on this web page? If that’s the case, you’ll have handed over your info to a scammer.
We took the screenshot above as a part of following a phishing assault to its finish—with out coming into any authentic information, after all. Actually, we entered a rubbish e mail handle and password, and it nonetheless allow us to in. That’s as a result of the scammers have been after different info, as you’ll quickly see.
As we dug into the positioning extra deeply, it appeared fairly spot on. The design mirrored PayPal’s fashion, and the footer hyperlinks appeared official sufficient. But then we appeared extra intently.
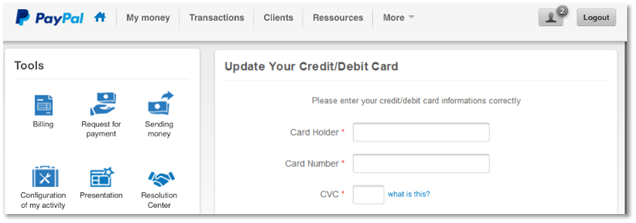 Be aware the refined errors, like “card informations” and “Configuration of my exercise.” Whereas firms make grammatical errors occasionally, recognizing them in an interface ought to increase an enormous crimson flag. Plus, the positioning asks for bank card info very early within the course of. All suspicious.
Be aware the refined errors, like “card informations” and “Configuration of my exercise.” Whereas firms make grammatical errors occasionally, recognizing them in an interface ought to increase an enormous crimson flag. Plus, the positioning asks for bank card info very early within the course of. All suspicious.
Right here’s the place the attackers actually received daring.
 They ask for financial institution “informations,” which not solely consists of routing and account numbers, however they ask for the account password too. As stated, daring. And completely bogus.
They ask for financial institution “informations,” which not solely consists of routing and account numbers, however they ask for the account password too. As stated, daring. And completely bogus.
Taken all collectively, the refined errors and the bald-faced seize for exacting account info clearly mark this as a rip-off.
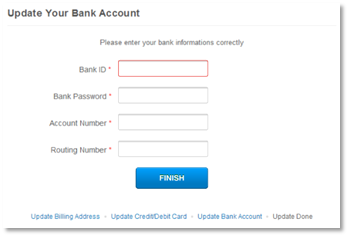
Let’s take a number of steps again, although. Who despatched the phishing e mail that directed us to this malicious web site? None apart from “paypal at inc dot-com.”
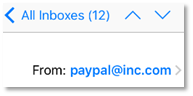 Clearly, that’s a phony e mail. And typical of a phishing assault the place an attacker shoehorns a well-recognized title into an unassociated e mail handle, on this case “inc dot-com.” Attackers can also gin up phony addresses that mimic official addresses, like “paypalcustsv dot-com.” Something to trick you.
Clearly, that’s a phony e mail. And typical of a phishing assault the place an attacker shoehorns a well-recognized title into an unassociated e mail handle, on this case “inc dot-com.” Attackers can also gin up phony addresses that mimic official addresses, like “paypalcustsv dot-com.” Something to trick you.
Likewise, the malicious web site that the phishing e mail despatched us to used a spoofed handle as effectively. It had no official affiliation with PayPal in any respect—which is proof optimistic of a phishing assault.
Be aware that firms solely ship emails from their official domains, simply as their websites solely use their official domains. A number of firms and organizations will checklist these official domains on their web sites to assist curb phishing assaults.
For instance, PayPal has a web page that clearly states the way it will and won’t contact you. At McAfee, we have now a whole web page devoted to stopping phishing assaults, which additionally lists the official e mail addresses we use.
Different examples of phishing assaults
Not each scammer is so subtle, no less than in the best way that they design their phishing emails. We are able to level to a couple phishing emails that posed as authentic communication from McAfee as examples.
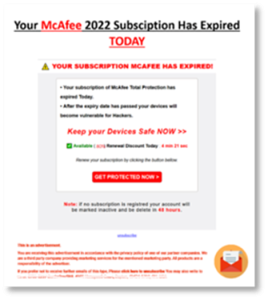
There’s quite a bit occurring on this first e mail instance. The scammers attempt to mimic the McAfee model, but don’t pull it off. Nonetheless, they do a number of issues to attempt to act convincing.
 Be aware using pictures and the field shot of our software program, paired with a distinguished “act now” headline. It’s not the fashion of pictures we use. Not that folks would usually know this. Nevertheless, some might need a passing thought like, “Huh. That doesn’t actually appear to be what McAfee normally sends me.”
Be aware using pictures and the field shot of our software program, paired with a distinguished “act now” headline. It’s not the fashion of pictures we use. Not that folks would usually know this. Nevertheless, some might need a passing thought like, “Huh. That doesn’t actually appear to be what McAfee normally sends me.”
Past that, there are a number of capitalization errors, some misplaced punctuation, and the “order now” and “60% off” icons look slightly slapped on. Additionally, word the little sprint of worry it throws in with a point out of “There are (42) viruses in your pc …”
Taken all collectively, somebody can readily spot that this can be a rip-off with a better look.
This subsequent advert falls into the much less subtle class. It’s virtually all textual content and goes heavy on the crimson ink. As soon as once more, it hosts loads of capitalization errors, with a number of gaffes in grammar as effectively. In all, it doesn’t learn easily. Neither is it simple on the attention, as a correct e mail about your account ought to be.
 What units this instance aside is the “commercial” disclaimer under, which tries to lend the assault some legitimacy. Additionally word the phony “unsubscribe” hyperlink, plus the (scratched out) mailing handle and cellphone, which all attempt to do the identical.
What units this instance aside is the “commercial” disclaimer under, which tries to lend the assault some legitimacy. Additionally word the phony “unsubscribe” hyperlink, plus the (scratched out) mailing handle and cellphone, which all attempt to do the identical.
This final instance doesn’t get our font proper, and the trademark image is awkwardly positioned. The same old grammar and capitalization errors crop up once more, but this piece of phishing takes a barely totally different strategy.
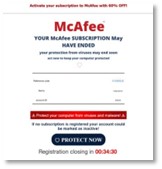 The scammers positioned just a little timer on the backside of the e-mail. That provides a level of shortage. They need you to suppose that you’ve about half an hour earlier than you might be unable to register for cover. That’s bogus, after all.
The scammers positioned just a little timer on the backside of the e-mail. That provides a level of shortage. They need you to suppose that you’ve about half an hour earlier than you might be unable to register for cover. That’s bogus, after all.
See any recurring themes? There are a number of for positive. With these examples in thoughts, get into the main points—how one can spot phishing assaults and how one can keep away from them altogether.
Find out how to spot and stop phishing assaults.
Simply as we noticed, some phishing assaults certainly seem fishy from the beginning. But generally it takes a little bit of time and a very vital eye to identify.
And that’s what scammers rely on. They hope that you just’re shifting shortly or in any other case just a little preoccupied if you’re going by your e mail or messages. Distracted sufficient so that you just may not pause to suppose, is this message actually legit?
Among the best methods to beat scammers is to take a second to scrutinize that message whereas retaining the next in thoughts …
They play in your feelings.
Concern. That’s an enormous one. Possibly it’s an angry-sounding e mail from a authorities company saying that you just owe again taxes. Or possibly it’s one other from a member of the family asking for cash as a result of there’s an emergency. Both manner, scammers will lean closely on worry as a motivator.
If you happen to obtain such a message, suppose twice. Contemplate if it’s real. As an example, contemplate that tax e mail instance. Within the U.S., the Inner Income Service (IRS) has particular tips as to how and when they are going to contact you. As a rule, they are going to seemingly contact you through bodily mail delivered by the U.S. Postal Service. (They gained’t name or apply strain ways—solely scammers do this.) Likewise, different nations may have related requirements as effectively.
They ask you to behave—NOW.
Scammers additionally love urgency. Phishing assaults start by stirring up your feelings and getting you to behave shortly. Scammers may use threats or overly excitable language to create that sense of urgency, each of that are clear indicators of a possible rip-off.
Granted, authentic companies and organizations may attain out to inform you of a late cost or doable illicit exercise on one among your accounts. But they’ll take a much more skilled and even-handed tone than a scammer would. For instance, it’s extremely unlikely that your native electrical utility will angrily shut off your service should you don’t pay your past-due invoice instantly.
They need you to pay a sure manner.
Present playing cards, cryptocurrency, cash orders—these types of cost are one other signal that you just may be taking a look at a phishing assault. Scammers desire these strategies of cost as a result of they’re troublesome to hint. Moreover, shoppers have little or no solution to get better misplaced funds from these cost strategies.
Official companies and organizations gained’t ask for funds in these varieties. If you happen to get a message asking for cost in a type of varieties, you may guess it’s a rip-off.
They use mismatched addresses.
Right here’s one other manner you may spot a phishing assault. Take an in depth have a look at the addresses the message is utilizing. If it’s an e mail, have a look at the e-mail handle. Possibly the handle doesn’t match the corporate or group in any respect. Or possibly it does considerably, but it provides a number of letters or phrases to the title. This marks yet one more signal that you just may have a phishing assault in your fingers.
Likewise, if the message accommodates an online hyperlink, intently study that as effectively. If the title appears to be like in any respect unfamiliar or altered from the best way you’ve seen it earlier than, that may additionally imply you’re taking a look at a phishing try.
Defend your self from phishing assaults
- Go on to the supply. Some phishing assaults can look convincing. A lot so that you just’ll need to comply with up on them, like in case your financial institution stories irregular exercise in your account or a invoice seems to be late. In these instances, don’t click on on the hyperlink within the message. Go straight to the web site of the enterprise or group in query and entry your account from there. Likewise, when you have questions, you may at all times attain out to their customer support quantity or net web page.
- Comply with up with the sender. Hold an eye fixed out for emails that could be a spear phishing assault. If an e mail that appears prefer it got here from a member of the family, pal, or enterprise affiliate, comply with up with them to see in the event that they despatched it. Significantly if asks for cash, accommodates a questionable attachment or hyperlink, or just doesn’t sound fairly like them. Textual content, cellphone, or test in with them in individual. Don’t comply with up by replying to the e-mail, as it could have been compromised.
- Don’t obtain attachments. Some phishing assaults ship attachments filled with malware just like the ransomware, viruses, and keyloggers we talked about earlier. Scammers might go them off as an bill, a report, and even a proposal for coupons. If you happen to obtain a message with such an attachment, delete it. And most actually don’t open it. Even should you obtain an e mail with an attachment from somebody , comply with up with that individual. Significantly should you weren’t anticipating an attachment from them. Scammers will typically hijack or spoof e mail accounts of on a regular basis individuals to unfold malware.
- Hover over hyperlinks to confirm the URL. On computer systems and laptops, you may hover your cursor over hyperlinks with out clicking on them to see the online handle. If the URL appears to be like suspicious in any of the methods we talked about simply above, delete the message, and don’t ever click on.
Defend your self from e mail assaults even additional
On-line safety software program can shield you from phishing assaults in a number of methods.
For starters, it affords net safety that warns you when hyperlinks result in malicious web sites, akin to those utilized in phishing assaults. In the identical manner, on-line safety software program can warn you about malicious downloads and e mail attachments so that you just don’t find yourself with malware in your machine. And, if the unlucky does occur, antivirus can block and take away malware.
On-line safety software program like ours also can handle the basis of the issue. Scammers should get your e mail handle from someplace. Usually, they get it from on-line knowledge brokers, websites that collect and promote private info to any purchaser—scammers included.
Information brokers supply this info from public data and third events alike that they promote in bulk, offering scammers with large mailing lists that may goal 1000’s of potential victims. You’ll be able to take away your private information from among the riskiest knowledge dealer websites with our Private Information Cleanup, which might decrease your publicity to scammers by retaining your e mail handle out of their fingers.
In all, phishing emails have telltale indicators, some harder to see than others. But you may spot them when what to search for and take the time to search for them. With these assaults so prevalent and on the rise, taking a look at your e mail with a vital eye is a should immediately.


