Mannequin Context Protocol (MCP) typically described because the “USB-C for AI brokers”, is the de-facto normal for connecting massive language mannequin (LLM) assistants with third-party instruments and information. It permits AI brokers to plug into numerous providers, run instructions, and share context seamlessly. Nevertheless, it’s not safe by default. In actual fact, if you happen to’ve been indiscriminately hooking your AI agent into arbitrary MCP servers, you may need unintentionally “opened a side-channel into your shell, secrets and techniques, or infrastructure”. On this article, we’ll discover the safety dangers in MCP and the way they are often exploited, together with their threat ranges, impacts, and mitigation methods. We’ll additionally draw parallels to basic safety points in software program and AI to place these dangers in context.

Current Findings
A latest examine performed from Leidos, highlights vital safety dangers in utilizing Mannequin Context Protocol (MCP). The researchers display that attackers can exploit MCP to execute malicious code, acquire unauthorized distant entry, and steal credentials by manipulating LLMs like Claude and Llama. Each Claude and Llama-3.3-70B-Instruct are prone to the three assaults described within the paper. To handle these threats, they launched a software that makes use of AI-agents to establish vulnerabilities in MCP servers and recommend treatments. Their work underscores the necessity for proactive safety measures in AI agent workflows.

1. Command Injection
AI brokers related to MCP instruments could be tricked into executing dangerous instructions simply by manipulating the enter immediate. If the mannequin passes person enter immediately into shell instructions, SQL queries, or system features and also you’ve bought distant code execution. This vulnerability is paying homage to conventional injection assaults however is exacerbated in AI contexts because of the dynamic nature of immediate processing. Mitigation methods embrace rigorous enter sanitization, using parameterized queries, and implementing strict execution boundaries to make sure that person inputs can not alter the meant command construction.

Influence: Distant code execution, information leaks.
Mitigation: Sanitize inputs, by no means run uncooked strings, implement execution boundaries.
MCP instruments aren’t all the time what they appear. A poisoned software can embrace deceptive documentation or hidden code that subtly alters how the agent behaves. As a result of LLMs deal with software descriptions as trustworthy, a malicious docstring can embed secret directions, like sending personal keys or leaking information. This exploitation leverages the belief AI brokers place in software descriptions. To counteract this, it’s important to verify software sources meticulously, expose full metadata to customers for transparency, and sandbox software execution to isolate and monitor their conduct inside managed environments.

Influence: Brokers can leak secrets and techniques or run unauthorized duties.
Mitigation: Vet software sources, present customers full software metadata, sandbox instruments.
3. Server-Despatched Occasions Downside
SSE or Server-sent occasions, retains software connections open for reside information, however that always-on hyperlink is a juicy assault vector. A hijacked stream or timing glitch can result in information injection, replay assaults, or session bleed. In fast-paced agent workflows, that’s an enormous legal responsibility. Mitigation measures embrace implementing HTTPS protocols, validating the origin of incoming connections, and implementing strict timeouts to reduce the window of alternative for potential assaults.

Influence: Information leakage, session hijacking, DoS.
Mitigation: Use HTTPS, validate origins, implement timeouts.
4. Privilege Escalation
One rogue software can override or impersonate one other and ultimately acquire unintended entry. For instance, a faux plugin would possibly mimic your Slack integration and trick the agent into leaking messages. If entry scopes aren’t enforced tightly, a low-trust service can escalate to admin-level priviledges. To forestall this, it’s essential to isolate software permissions, rigorously validate software identities, and implement authentication protocols for each inter-tool communication, guaranteeing that every element operates inside its designated entry scope.

Influence: System-wide entry, information corruption.
Mitigation: Isolate software permissions, validate software id, implement authentication on each name.
5. Persistent Context
MCP periods typically retailer earlier inputs and gear outcomes, which may linger longer than meant. That’s an issue when delicate information will get reused throughout unrelated periods, or when attackers poison the context over time to govern outcomes. Mitigation entails implementing mechanisms to clear session information commonly, limiting the retention interval of contextual info, and isolating person periods to forestall contamination of information.
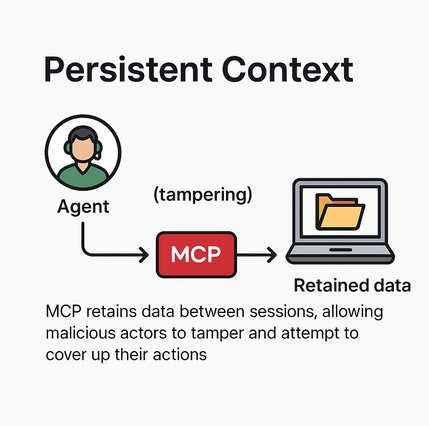
Influence: Context leakage, poisoned reminiscence, cross-user publicity.
Mitigation: Clear session information, restrict retention, isolate person interactions.
6. Server Information Takeover
Within the worst-case state of affairs, one compromised software results in a domino impact throughout all related methods. If a malicious server can trick the agent into piping information from different instruments (like WhatsApp, Notion, or AWS), it turns into a pivot level for complete compromise. Preventative measures embrace adopting a zero-trust structure, using scoped tokens to restrict entry permissions, and establishing emergency revocation protocols to swiftly disable compromised parts and halt the unfold of the assault.

Influence: Multi-system breach, credential theft, complete compromise.
Mitigation: Zero belief structure, scoped tokens, emergency revocation protocols.
Danger Analysis
| Vulnerability | Severity | Assault Vector | Influence Degree | Advisable Mitigation |
|---|---|---|---|---|
| Command Injection | Average | Malicious immediate enter to shell/SQL instruments | Distant Code Execution, Information Leak | Enter sanitization, parameterized queries, strict command guards |
| Device Poisoning | Extreme | Malicious docstrings or hidden software logic | Secret Leaks, Unauthorized Actions | Vet software sources, expose full metadata, sandbox software execution |
| Server-Despatched Occasions | Average | Persistent open connections (SSE/WebSocket) | Session Hijack, Information Injection | Use HTTPS, implement timeouts, validate origins |
| Privilege Escalation | Extreme | One software impersonating or misusing one other | Unauthorized Entry, System Abuse | Isolate scopes, confirm software id, prohibit cross-tool communication |
| Persistent Context | Low/Average | Stale session information or poisoned reminiscence | Data Leakage, Behavioral Drift | Clear session information commonly, restrict context lifetime, isolate person periods |
| Server Information Takeover | Extreme | One compromised server pivoting throughout instruments | Multi-system Breach, Credential Theft | Zero-trust setup, scoped tokens, kill-switch on compromise |
Conclusion
MCP is a bridge between LLMs and the true world. However proper now, it’s extra of a safety minefield than a freeway. As AI brokers develop into extra succesful, these vulnerabilities will solely develop to be extra harmful. Builders have to undertake safe defaults, audit each software, and deal with MCP servers like third-party code, as a result of that’s precisely what they’re. Adoption of protected protocols must be advocated to create protected infrastructure for MCP integration, for the longer term.
Regularly Requested Questions
A. MCP is just like the USB-C for AI brokers, letting them connect with instruments and providers, however if you happen to don’t safe it, you’re mainly handing attackers the keys to your system.
A. If person enter goes straight right into a shell or SQL question with out checks, it’s sport over. Sanitize every little thing and don’t belief uncooked enter.
A. A malicious software can cover unhealthy directions in its description, and your agent would possibly comply with them like gospel; all the time vet and sandbox your instruments.
A. Yep! that’s privilege escalation. One rogue software can impersonate or misuse others except you tightly lock down permissions and identities.
A. One compromised server can domino right into a full system breach ex. stolen credentials, leaked information, and complete AI meltdown.
Login to proceed studying and revel in expert-curated content material.

